Blockchain Analytics Explained: Methods, Use Cases, and Real-World Applications

Over recent years, the crypto ecosystem has evolved from a retail-driven experiment into a complex financial system used by exchanges, payment providers, custodians, and institutional investors. With this growth came more sophisticated fraud schemes, large-scale hacks, and cross-border laundering patterns. In parallel, international standard-setters and national authorities have tightened anti-money laundering, counter-terrorist financing, and sanctions requirements for VASPs (Virtual Asset Service Providers), bringing expectations closer to those applied to traditional financial institutions. In this environment, viewing a transaction in a blockchain explorer is no longer sufficient to understand its risk.
📘 Blockchain Analytics is the systematic analysis of on-chain transaction data to detect risk, trace assets, and understand relationships between wallets and entities. It brings together on-chain monitoring, transaction tracing, wallet clustering, fund flow analysis, and risk scoring to support both continuous compliance monitoring and deeper blockchain forensics.
In this article, we will explain how this discipline works in practice, how it differs from blockchain forensics, why it has become central to AML and sanctions compliance, and how it supports tracing and cross-chain analysis in a multi-chain ecosystem.
What Is Blockchain Analytics?
Blockchain analytics is the systematic collection, processing, and interpretation of on-chain data to identify risk, trace fund flows, and attribute wallet activity to specific entities or typologies. Rather than viewing each transaction in isolation, blockchain analytics builds a connected graph of addresses, transactions, and services, and uses it to highlight suspicious transactions and patterns relevant to compliance and investigations.
It is important to distinguish between:
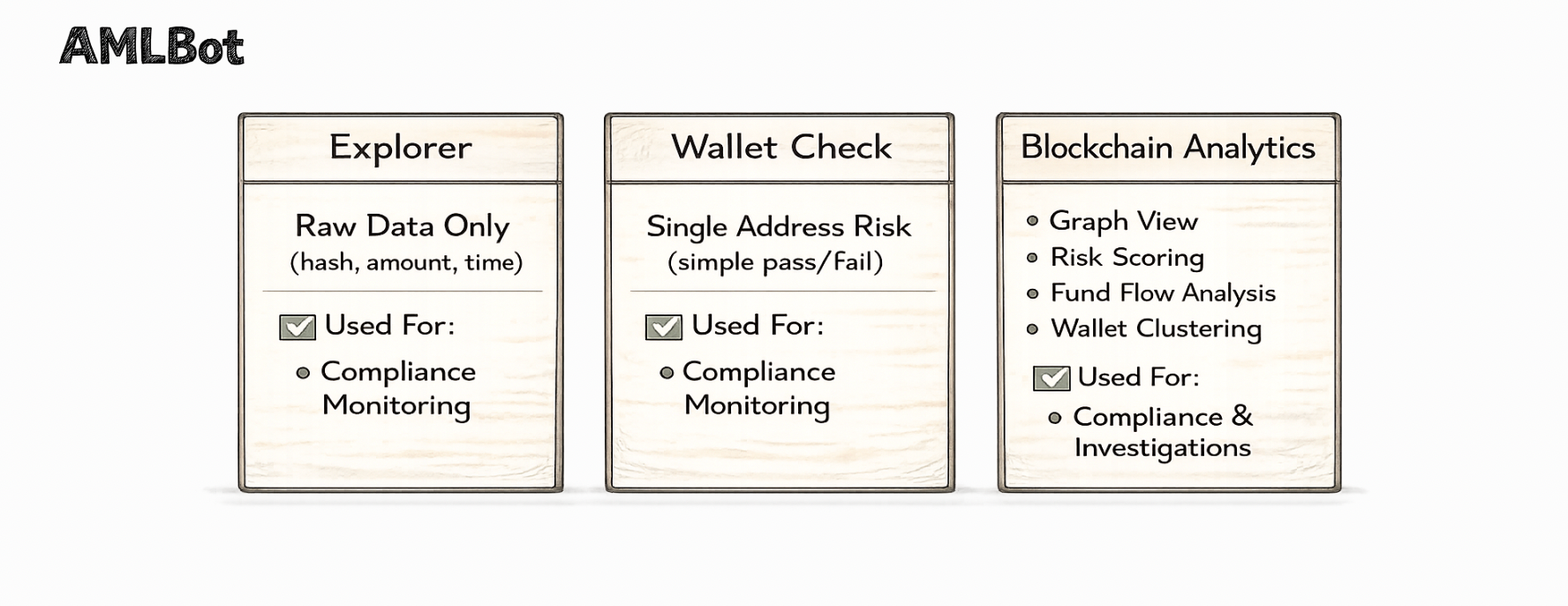
📘 Blockchain Explorers – public tools that display raw data (transaction hash, amount, fees, basic address relationships) but provide little or no risk context.
📘 Simple “Wallet Checks” – basic screening tools that verify whether an address appears on a sanctions list or blocklist, often without considering wider transaction history or counterparties.
📘 Full-Fledged Analytical Systems – platforms that combine on-chain monitoring, transaction tracing, wallet clustering, fund flow analysis, and risk scoring to provide a consolidated risk view at the address, transaction, and entity level.
In practice, this analytical infrastructure is applied in two principal domains:
- Compliance Monitoring, in which institutions screen deposits, withdrawals, and internal transfers for sanctions exposure, money laundering patterns, and other regulatory risks.
- Blockchain Forensics and Investigations, where analysts conduct deeper, case-driven work to reconstruct fund flows, identify related wallets, and prepare evidentiary materials.
Why Blockchain Analytics Is Critical for Crypto Businesses
For crypto businesses, this form of analytics has become core infrastructure rather than an optional add-on. Exchanges, custodians, payment providers, and other VASPs are now expected to identify, assess, and mitigate financial crime risks in a manner comparable to traditional financial institutions. Risk-based AML, CTF (Counter-Terrorist Financing), and sanctions obligations apply directly to their virtual asset activities. Under FATF Recommendation 15, VASPs must be licensed or registered and “subject to effective systems for monitoring or supervision” for AML/CFT purposes, bringing them firmly within the global regulatory perimeter.
In this environment, these analytics provide the factual basis for risk assessment, day-to-day monitoring, and investigations across the full lifecycle of customer and transactional activity.
AML and Regulatory Monitoring
From a legal and compliance standpoint, this infrastructure underpins monitoring for crypto businesses. It helps institutions:
- Implement risk-based AML programs in line with FATF standards for virtual assets and VASPs, including the expectation that firms identify and manage money-laundering and terrorist-financing risks arising from virtual asset services.
- Fulfill recordkeeping and so-called “Travel Rule” obligations under frameworks such as the U.S. Bank Secrecy Act. For example, 31 C.F.R. § 1010.410(e)–(f) requires certain financial institutions to keep records of who sends funds, who receives them, and the essential details of the transfer. When a crypto business is treated as a money services business, these recordkeeping and information-sharing duties also apply to many of its crypto transfers.
- Comply with EU rules on information accompanying transfers of funds and certain crypto-assets, notably Regulation (EU) 2023/1113, which obliges CASPs (Crypto-asset Service Providers) to collect and transmit defined originator and beneficiary data with each relevant transfer.
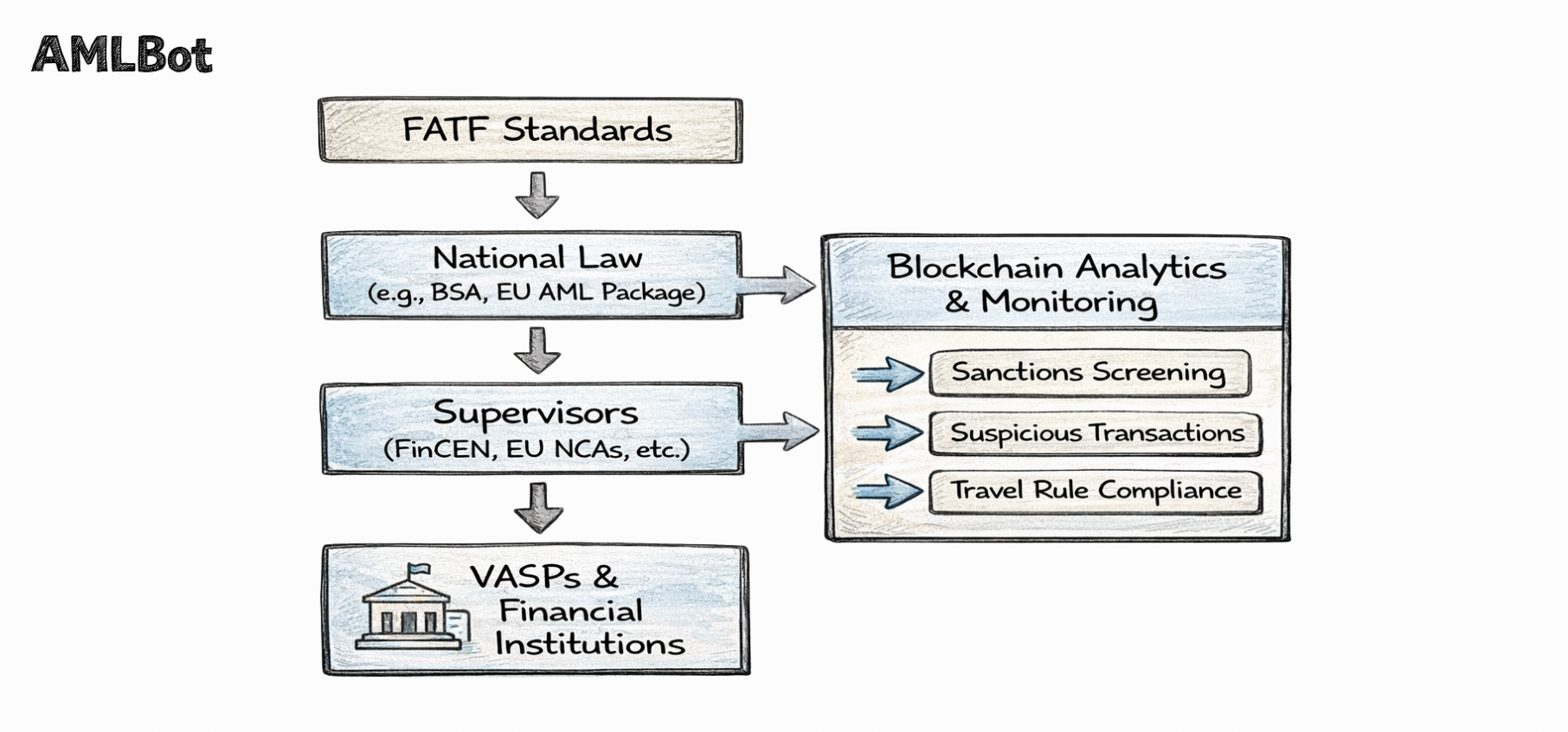
The diagram above presents a simplified conceptual framework illustrating how international standards, national legislation, supervisory oversight, and operational compliance tools interact. It does not imply a formal legal hierarchy, but rather reflects how regulatory expectations translate into practical monitoring obligations for regulated entities.
It is important to distinguish between regulatory obligations and the technological solutions used to meet them. Supervisory authorities generally require effective AML, sanctions, and recordkeeping controls, but they do not mandate specific software tools. Blockchain analytics functions as an operational compliance layer that enables institutions to fulfill these obligations in the context of virtual asset activity. Operationally, these tools support:
- Sanctions Exposure Screening – checking whether wallets or transactions are linked to sanctioned persons, entities, or jurisdictions. Authorities such as OFAC have clarified that sanctions compliance obligations are the same regardless of whether a transaction is denominated in digital currency or in fiat, which means crypto flows must be screened with the same rigor as bank transfers. In practice, this involves both traditional sanctions list screening and blockchain-based exposure analysis to detect indirect interaction with sanctioned actors.
- Risk Monitoring and Continuous Screening – automated surveillance of inbound and outbound flows against typologies such as repeated interaction with mixers, high-risk exchanges, or ransomware-associated clusters.
- Review of Suspicious Transactions – flagging transactions with high-risk indicators for manual review and, where appropriate, escalation to suspicious activity reports or other regulatory filings.
In practice, these capabilities are often integrated into an on-chain transaction monitoring platform that provides dashboards, alert queues, and audit trails for compliance teams.
Fraud and Scam Detection
Beyond formal AML and sanctions obligations, this analytics layer is central to fraud and scam detection. It enables crypto businesses to:
- Detect scams early by monitoring for patterns typical of investment frauds, phishing campaigns, or impersonation schemes. For example, repeated deposits from addresses previously linked to scam activity.
- Recognize risk patterns using historical labels, typologies, and analytical models to identify suspicious transactions that may not breach a single rule in isolation but form part of a broader risky pattern.
- Monitor and analyze fund flows as assets move between addresses, services, and networks, assessing whether an incident is contained, escalating, or already laundered. In practice, this fund flow analysis is often combined with detailed transaction tracing at the case level.
Risk Exposure Across Multiple Blockchains
Modern crypto crime rarely remains confined to a single network. Attackers frequently:
- Move assets through bridges to mint wrapped tokens or shift value to other blockchains.
- Use decentralized exchanges (DEXs) and aggregators to conduct rapid swaps between assets and stablecoins.
- Route funds through several chains to fragment exposure and complicate attribution.
This behaviour creates multi-chain risk and makes cross-chain analysis a core component of modern crypto risk analytics. Resources discussing cross-chain transaction analysis challenges explain how bridge contracts, wrapped assets, and liquidity pools complicate both continuous monitoring and investigative work, and why purpose-built analytics are needed to reconnect these fragments into coherent fund-flow narratives.
How Blockchain Analytics Works
In practice, this discipline is implemented as a layered process. First, on-chain data is collected and normalized. Then it is transformed into a transaction graph and enriched with clustering, entity tagging, and risk scoring. On top of this technical infrastructure, institutions run on-chain monitoring for day-to-day compliance and support case-based investigations when incidents or alerts arise.
Data Collection and On-Chain Monitoring
Analytics providers typically operate full nodes or indexers for the networks they support and continuously ingest blocks as they are produced. This data ingestion covers transactions and other relevant protocol events needed to reconstruct fund flows over time. On top of this raw data, the provider builds an on-chain monitoring and surveillance layer, which generally includes:
- Normalizing addresses, transaction types, and formats across different blockchains.
- Applying rules and analytical models that detect patterns associated with higher AML, CTF, or fraud risk.
- Storing historical activity to enable long-term behavioural analysis and trend detection.
The result is a monitoring infrastructure that enables institutions to observe on-chain flows in near real time without managing low-level node operations themselves.
Transaction Graph Analysis
Once data is ingested, it is modeled as a transaction graph, where nodes represent addresses or entities and edges represent transfers between them. This graph modeling makes it possible to: map fund flows from an initial source wallet through intermediaries to potential cash-out points; identify connections between addresses, services, and known entities that would not be visible from isolated transactions. Within this graph, investigators and analysts can perform a structured fund flow analysis, focusing on the direction, timing, and sequencing of transfers, as well as the use of intermediaries and services.
Wallet Clustering and Entity Identification
On most public blockchains, a single user or service typically controls many addresses. Wallet clustering is the process of grouping addresses that likely belong to the same underlying entity based on observed behaviour and technical indicators.
Once such clusters are formed, they can be linked to specific entities, for example, exchanges, custodial services, darknet markets, scam operations, or sanctioned organizations, using: publicly available information (such as published deposit addresses), information disclosed by law enforcement or supervisory authorities, and internal or proprietary investigative findings.
This entity-tagging process is essential for meaningful risk attribution. Rather than assessing risk at the level of a single address, compliance teams can see whether a customer is interacting with a high-risk exchange, a mixing service, or a cluster associated with sanctions or known criminal activity.
Risk Scoring and Alerts
Finally, analytics platforms apply risk scoring models that combine multiple factors, such as:
- The nature of counterparties (for example, a regulated exchange versus a sanctioned mixer).
- Indicators derived from typologies and behavioural patterns (for example, rapid in-and-out movements and the concentration of funds from high-risk clusters).
- Geographic considerations and relevant sanctions lists.
Each address or transaction is assigned a score representing the assessed level of AML, CTF, or sanctions risk. Thresholds are then used to automatically generate alerts, which feed into the institution’s continuous monitoring and case-management workflows. Compliance teams review these alerts, document their assessment, and, where appropriate, escalate to suspicious activity reports, internal investigations, or referrals to law-enforcement authorities.
Blockchain Analytics vs Blockchain Forensics
Although the two terms are sometimes used interchangeably, blockchain analytics and blockchain forensics describe different stages of the risk-management and enforcement lifecycle.
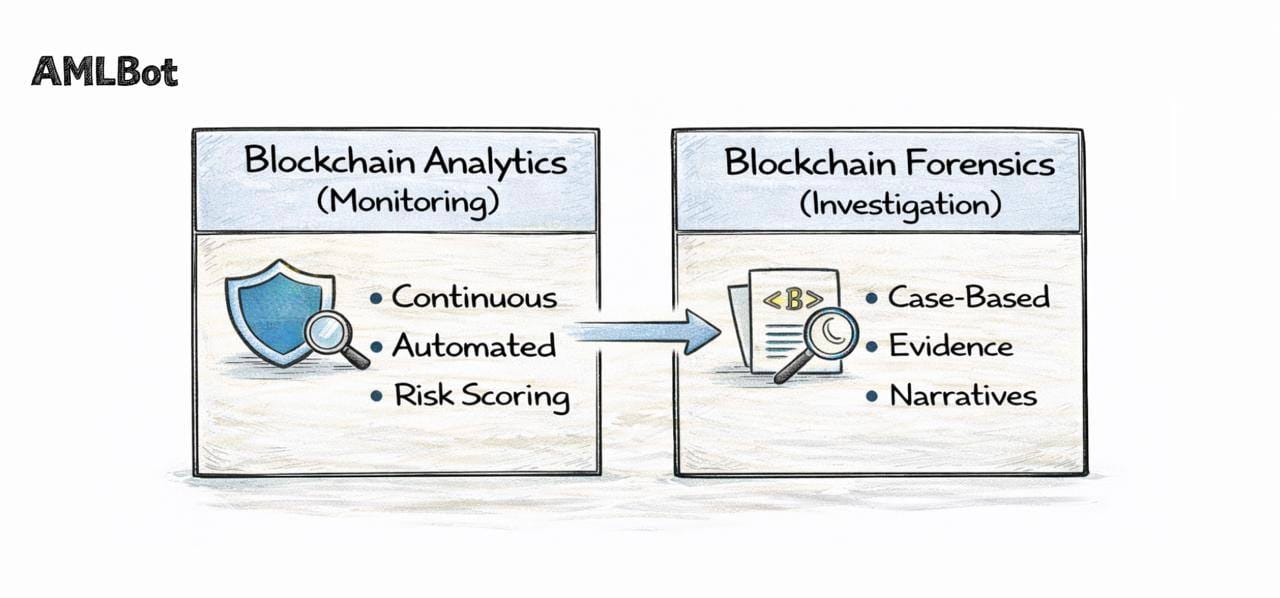
Blockchain Analytics focuses on ongoing monitoring and risk detection. It is continuous, largely automated, and closely integrated with AML, CTF, and sanctions workflows. The primary objective is to screen for activity, identify suspicious transactions, and generate alerts requiring further review.
Blockchain Forensics, by contrast, refers to case-driven investigation and evidence building. It typically begins once an incident is identified, such as a hack, scam, or regulatory inquiry, and involves detailed case reconstruction, wallet and entity attribution, and the preparation of documentation that can be relied on by regulators, law enforcement authorities, or courts.
In practice, monitoring alerts generated by blockchain analytics often escalate into formal investigations conducted using forensic methods.
Cross-Chain Complexity and Modern Challenges
The shift to a multi-chain crypto ecosystem has significantly increased the complexity of both monitoring and investigations. Illicit actors rarely remain on a single network and instead use multiple technical mechanisms to move value across chains and assets.
Common Patterns:
- (a) Chain Hopping – rapidly moving value between blockchains to fragment the audit trail and reduce the visibility of a single, linear path.
- (b) Use of Bridges – locking assets on one chain and minting wrapped representations on another. If these bridge flows are not modelled correctly, simple tracing can appear to “break” at the bridge contract.
- (c) Activity on DEXs and Aggregators – using decentralized exchanges and routing protocols to swap between tokens and stablecoins at scale, often in a short time window, which complicates the reconstruction of a clear sequence of trades.
- (d) Use of Mixers and Privacy Tools – inserting layers that increase obfuscation and make attribution more difficult, even though they do not make analysis impossible in all cases.
In this environment, effective cross-chain analysis requires a unified view of activity across multiple blockchains, explicit modelling of bridge contracts and wrapped assets, and an understanding of how liquidity pools and routing mechanisms affect observable fund flows.
Resources on cross-chain transaction analysis describe how providers link “before bridge” and “after bridge” activity to reconstruct coherent fund-flow narratives despite these obstacles and to support both compliance monitoring and investigative work.
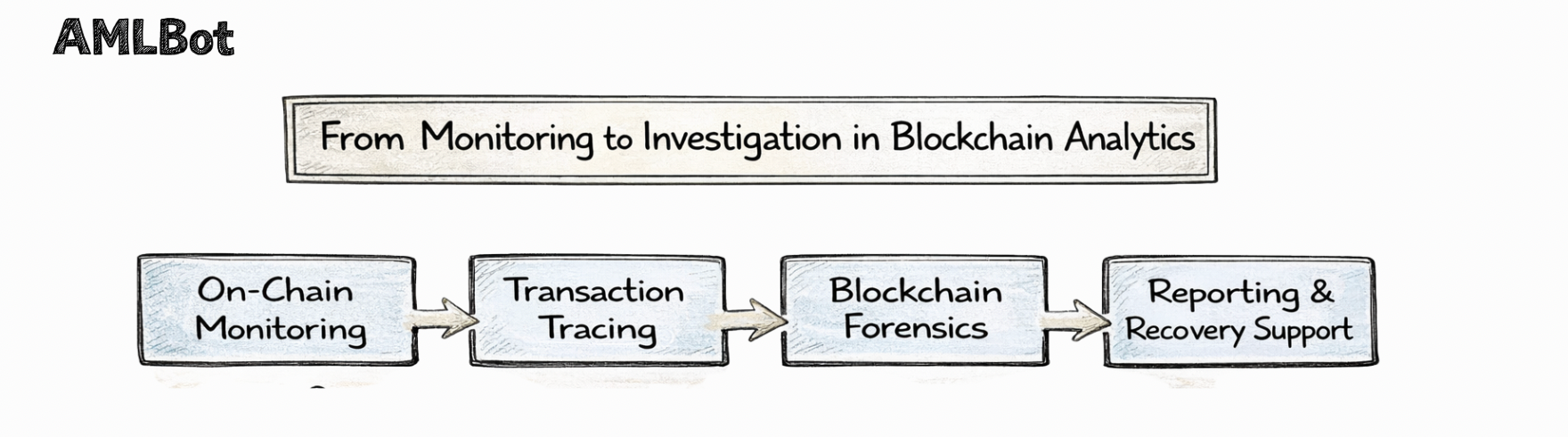
From Monitoring to Investigation
In a mature compliance program, the analytics layer supports a structured progression from automated monitoring to formal investigation. Monitoring is primarily about screening and alerting, while investigation is about examining specific cases in depth, reconstructing facts, and preparing evidence that can be relied on by internal decision-makers, regulators, or law-enforcement authorities.
In practice, the typical sequence is:
- On-Chain Monitoring And Screening. Transactions are monitored in real time for sanctions exposure, links to high-risk entities, and typologies associated with money laundering, terrorist financing, or fraud.
- Alert Generation. Transactions or addresses that exceed predefined risk thresholds are flagged as suspicious transactions and converted into alerts within the monitoring system.
- Internal Review. Compliance Analysts review alerts, apply customer context (KYC data, expected business activity, prior history), and decide whether to close the alert, escalate it, or block the transaction pending further analysis.
- Investigation And Fund Tracing. Where escalation is warranted, investigators perform detailed transaction tracing and fund flow reconstruction, using forensic-grade tools to follow assets across wallets, services, and, where relevant, multiple blockchains. This is the point where monitoring transitions into blockchain forensics: the focus shifts from general screening to case-specific fact-finding and evidence building.
- Reporting And External Action. Depending on the outcome, the institution may prepare internal reports, file suspicious activity reports or equivalent regulatory filings, cooperate with law-enforcement authorities, or engage with other intermediaries (such as exchanges or stablecoin issuers) that may be able to restrict further movement of funds.
This end-to-end process shows how continuous monitoring and targeted investigation are functionally linked. Monitoring identifies potential issues; forensic work explains them, reconstructs what happened, and documents the findings. No responsible provider can promise that funds will be returned in a given case, but robust analytical work and investigations increase the likelihood of identifying laundering paths, locating potential freeze points, and supporting recovery efforts where practical options exist.
Use Cases of Blockchain Analytics
These capabilities are used across the crypto ecosystem as shared infrastructure for risk management, compliance, and enforcement. The same core capabilities, on-chain monitoring, transaction tracing, wallet clustering, and fund flow analysis, are applied differently by each type of stakeholder, but the objectives are similar: reduce exposure to financial crime, support informed decision-making, and produce defensible reporting.
Exchanges
Centralized Exchanges sit at the intersection of retail, institutional, and OTC flows, and are often the first point where regulators expect robust controls over virtual asset activity. These analytical capabilities help exchanges manage these expectations by providing a concrete view of where funds originate, where they are going, and how customers behave on-chain.
Typical applications include:
- Monitoring incoming deposits for sanctioned exposure and links to known scam clusters or other high-risk entities.
- Screening withdrawal destinations to identify high-risk services, mixers, or wallets that have previously been associated with illicit activity.
- Detecting interaction with high-risk entities, such as darknet markets or platforms subject to law enforcement or regulatory action.
- Investigating suspicious large transfers or unusual behavioural patterns where transaction size, frequency, or counterparties deviate from a customer’s expected profile.
By structuring these checks, exchanges can demonstrate that they have taken reasonable steps to manage sanctions, AML, and fraud risks associated with their platforms.
Custodians
Custodians and wallet providers are responsible for safeguarding client assets and ensuring their use remains consistent with legal and contractual expectations. They often manage large volumes of addresses and balances for many clients, which makes an aggregated on-chain view essential. Analytics tools support this role by enabling custodians to:
- Conduct ongoing monitoring of managed wallets, identifying inbound and outbound activity that may raise sanctions, AML, or fraud concerns.
- Perform internal compliance checks to ensure activity aligns with stated business models, client profiles, and applicable regulatory requirements.
- Produce exposure reporting by client, asset type, or jurisdiction for management, auditors, or supervisory authorities.
This allows custodians to demonstrate that they understand how client assets move on-chain and respond appropriately to elevated risk.
Payment Providers
Crypto payment processors and other payment service providers must manage risk at both the merchant and transaction levels. They sit between payers, merchants, and sometimes multiple intermediaries, making transparency over flows particularly important.
Analytics helps them:
- Carry out merchant risk assessment by analyzing historical flows to and from merchant wallets, including links to high-risk services or typologies.
- Implement transaction screening before settlement, so that payments from or to sanctioned, blocked, or otherwise high-risk counterparties can be identified before funds are finalized.
- Detect fraud exposure, for example, where particular merchants or customers are repeatedly linked to addresses associated with scams or other abuse.
These measures support both contractual risk management and regulatory expectations around fraud and financial crime prevention.
Compliance Teams
Within exchanges, custodians, and payment providers, internal compliance teams use these analytics as working tools rather than as background systems. Their role is to interpret alerts, apply context, and ensure that risk decisions are properly documented.
In practice, they rely on analytics to:
- Review and dispose of alerts generated by on-chain monitoring, recording rationales and outcomes for each decision.
- Escalate suspicious transactions for enhanced due diligence or formal investigation where risk indicators or customer information warrant a deeper review.
- Prepare internal reports for senior management, boards, or risk committees, summarizing exposure trends, significant incidents, and remediation actions.
In this way, blockchain analytics becomes part of the institution’s broader governance and reporting framework, not just a technical tool.
Law Enforcement Support
Law enforcement and regulatory authorities use these analytics to understand how suspected illicit funds move through the crypto ecosystem and to support legal proceedings. Their focus is less on day-to-day monitoring and more on reconstructing specific events and building a defensible evidentiary record. Key uses include:
- Fund flow reconstruction across addresses, services, and chains to determine how proceeds of crime or other illicit funds have been transferred and where they are currently held.
- Evidence preparation, including diagrams, timelines, and explanatory narratives, for use in criminal prosecutions, administrative actions, or supervisory measures.
- Cooperation with exchanges and other intermediaries, using analytical findings to identify potential freeze or seizure points where legal powers allow, and to request additional information.
These use cases show how blockchain analytics supports not only private risk reduction, but also public-interest enforcement and the integrity of the broader financial system.
Tools Used in Blockchain Analytics
In practice, this work relies on a combination of software components rather than a single application. These components can be grouped into several broad categories, each serving a specific role in monitoring, analysis, and reporting.
- Monitoring Dashboards – provide high-level exposure metrics, alert lists, and trend views across customers, assets, and jurisdictions. They allow compliance staff and management to see where risk is concentrated and how it evolves over time.
- On-chain Analytics and Investigation Platforms – support detailed case-level work, including transaction tracing, wallet clustering, and fund flow analysis. These tools are used when an alert is escalated, and a more granular reconstruction of events is required.
- Case-Management and Reporting Systems – integrate on-chain findings with internal customer records, documents, and workflow steps, so that investigations, decisions, and reports are tracked in a structured way.
Many institutions choose to implement these capabilities through an integrated investigation environment, such as the AMLBot Tracer Tool, which allows users to move from a high-level risk view to granular transaction-level analysis within a single platform.
The Future of Blockchain Analytics
Looking ahead, several structural trends are likely to shape the development of these analytical capabilities over the coming years:
- Multi-Chain and Modular Ecosystems. The continued growth of rollups, app-chains, sidechains, and modular execution layers means that activity is increasingly distributed across many domains and settlement layers. Analytics will need to correlate data across these environments, providing a consolidated view of risk that is not confined to a single base chain.
- Regulatory Expansion and Harmonisation. International standard-setters such as FATF continue to assess implementation of Recommendation 15 and the Travel Rule, encouraging jurisdictions to strengthen supervision of VASPs and virtual asset activities. In parallel, frameworks such as the EU’s AML package and Regulation (EU) 2023/1113 on information accompanying transfers of funds and crypto-assets illustrate a trend toward more detailed and prescriptive rules, with similar initiatives emerging in other regions. As these regimes mature, blockchain analytics will be expected to support more granular reporting and evidentiary standards.
- Greater Automation. As transaction volumes and alert counts grow, analytics platforms are integrating more advanced models to prioritize alerts, detect emerging patterns, and reduce false positives in line with risk-based expectations. The objective is not to replace human judgment, but to ensure that resources are focused on the highest-risk cases.
- Responsible Use of AI in Analytics. AI techniques are increasingly applied to clustering, anomaly detection, and narrative reconstruction in investigations. At the same time, regulators and institutions emphasize the need for explainability, auditability, and alignment with data protection obligations. Future blockchain analytics solutions are therefore likely to combine AI-driven insights with clear governance, documentation, and human oversight.
Taken together, these developments suggest that this discipline will continue to evolve from a specialized investigative capability into a core supervisory and compliance infrastructure for the crypto ecosystem.

What Is Blockchain Analytics?
It is the systematic analysis of on-chain transaction data to identify risk, trace fund flows, cluster related wallets, and detect suspicious activity. It goes beyond a simple blockchain explorer by using graph analysis, wallet clustering, entity tagging, and risk scoring to interpret patterns rather than just display raw data.
How Does Blockchain Analytics Differ from a Blockchain Explorer?
A blockchain explorer shows raw data, such as addresses, timestamps, and amounts for individual transactions. Blockchain analytics tools interpret that data by building transaction graphs, identifying connections between wallets, assigning risk levels, and reconstructing fund flows across multiple transactions and, in many cases, across multiple blockchains.
Is Blockchain Analytics the Same as Blockchain Forensics?
No. Blockchain analytics usually refers to continuous monitoring and risk detection for compliance purposes. Blockchain forensics involves deeper, case-specific investigations, evidence building, and fund flow reconstruction for legal, regulatory, or recovery proceedings.
How Do Crypto Businesses Use Blockchain Analytics for AML Compliance?
Crypto businesses use blockchain analytics to monitor incoming and outgoing transactions, screen wallet interactions for sanctions exposure, detect suspicious transactions, and generate documentation for AML and sanctions compliance. These activities support obligations under frameworks such as FATF Recommendation 15, the EU AML package, and the U.S. Bank Secrecy Act, including expectations around risk-based monitoring and reporting of illicit fund flows.
Can Blockchain Analytics Identify Wallet Owners?
Blockchain analytics, in itself, does not reveal personal identities from addresses alone. However, it can perform wallet clustering and attribute clusters to known entities, such as exchanges, services, or sanctioned organizations, based on transaction patterns, publicly available information, and investigative data.
What Is Transaction Tracing in Blockchain Analytics?
Transaction tracing is the process of following the movement of funds from one wallet to another across a sequence of transactions, often through multiple services and chains. It is a core element of blockchain forensics and is used to understand how assets move from an initial source (such as a victim) to potential cash-out points or freeze locations.
Why Is Cross-Chain Analysis Important?
Illicit funds often move across multiple blockchains via bridges and decentralized exchanges (DEXs). Cross-chain analysis links activity before and after such movements so that investigators can reconstruct fund flows even when assets change form or network. Without it, risk assessments remain incomplete in a multi-chain ecosystem.
Can Blockchain Analytics Prevent Crypto Scams?
These tools cannot prevent all scams, especially where victims voluntarily send funds. However, it can help detect high-risk wallet interactions earlier, flag suspicious patterns, and support investigations and potential freezing efforts after fraud has occurred, thereby reducing the impact of some incidents.
What Industries Rely on Blockchain Analytics?
Exchanges, custodians, payment providers, OTC (Over-the-Counter) desks, and fintech companies use blockchain analytics for compliance and risk management. Compliance teams and law-enforcement agencies rely on it for monitoring, investigations, and evidence preparation in criminal, regulatory, and supervisory cases.
What Are the Limitations of Blockchain Analytics?
Blockchain analytics depends on available on-chain data and the quality of entity tagging. Privacy tools, mixers, and complex cross-chain patterns can increase uncertainty and make attribution more difficult. Nevertheless, with robust data collection, graph analysis, and investigative methods, fund flows can often still be reconstructed to a level sufficient for risk management or evidentiary purposes.