Cross-Chain Analysis Explained: Tracing Crypto Across Multiple Blockchains

The modern crypto ecosystem spans hundreds of blockchains operating in parallel. Fund flows rarely remain within a single network: assets move between chains through bridges, decentralized exchanges, and wrapped token systems. Each transfer across a network boundary breaks transaction continuity. A movement that starts as ETH on Ethereum may appear on another chain as a wrapped equivalent after routing through liquidity pools and a DEX swap. For teams responsible for transaction tracing explained, these breaks create practical gaps in attribution and reconstruction.
Cross-chain analysis addresses this problem by correlating activity across separate ledgers and reconstructing multi-chain fund flows despite technical discontinuities. This article explains what causes tracing gaps, how cross-chain correlations are established in practice, and why results often carry probabilistic uncertainty.
What Is Cross-Chain Analysis
📘 Cross-chain analysis is the practice of tracing and correlating cryptocurrency transactions across multiple, separate blockchain networks. Unlike the framework described in blockchain analytics explained, which maps fund flows within a single ledger, cross-chain analysis must reconstruct movement that spans two or more independent networks, each with its own data structure, address format, and transaction model.
The distinction matters because the two disciplines operate on different assumptions. Single-chain tracing works within a single continuous ledger, with consistent address formats, referenced outputs, and full wallet history in one place. Cross-chain analysis lacks these conveniences: when assets move from Ethereum to Solana or from Bitcoin to BNB Chain, the deposit on one chain and the withdrawal on another are recorded independently, with no shared identifier linking them.
This is where the flow breaks down. Three structural factors create the discontinuity:
- Incompatible Architectures. Each blockchain uses its own address format and transaction model. Bitcoin's UTXO structure, Ethereum's account-based model, and Solana's runtime share no common schema, making direct cross-chain correlation technically non-trivial.
- Asset Conversion at Network Boundaries. When assets cross chains, their form changes: ETH becomes a wrapped equivalent, BTC becomes WBTC. The new token on the destination chain carries no on-chain reference to its origin.
- Scale of Fragmentation. The more networks involved, the harder the reconstruction. As multi-chain activity expands, cross-network correlations become increasingly complex, increasing the likelihood of attribution gaps across ledgers.
The cumulative result is an attribution gap: the analytical thread that connects a wallet to a real-world entity on one chain does not automatically extend across network boundaries. Cross-chain analysis refers to the structured methods used to re-establish that linkage across independent ledgers.
Why Cross-Chain Movement Complicates Tracing
Fund flow fragmentation is the most immediate problem. A single cross-chain transfer produces separate transaction records on independent ledgers, with no native link between them. When funds move across multiple networks in sequence, the activity exists as distributed fragments that must be aggregated and correlated to reconstruct the full path.
The scale of this problem is measurable: according to 2025 research, cross-chain investigations break down as follows:
- 33% involve more than three blockchains
- 27% involve more than five blockchains
- 20% span more than ten separate networks
Asset conversion at each network boundary deepens the problem. Assets do not cross chains in their native form. They are converted into representations that are technically new tokens on the destination network. ETH becomes a wrapped equivalent; BTC becomes WBTC on Ethereum or BTCB on BNB Chain. Each conversion creates a new token with its own contract address and transaction history, carrying no on-chain reference to the original asset it represents. For an investigator, this means the flow of funds cannot be traced by tracking a single asset. It must be reconstructed across multiple asset types, with their connections maintained off-chain in the bridge protocol's logic rather than in the ledger itself.
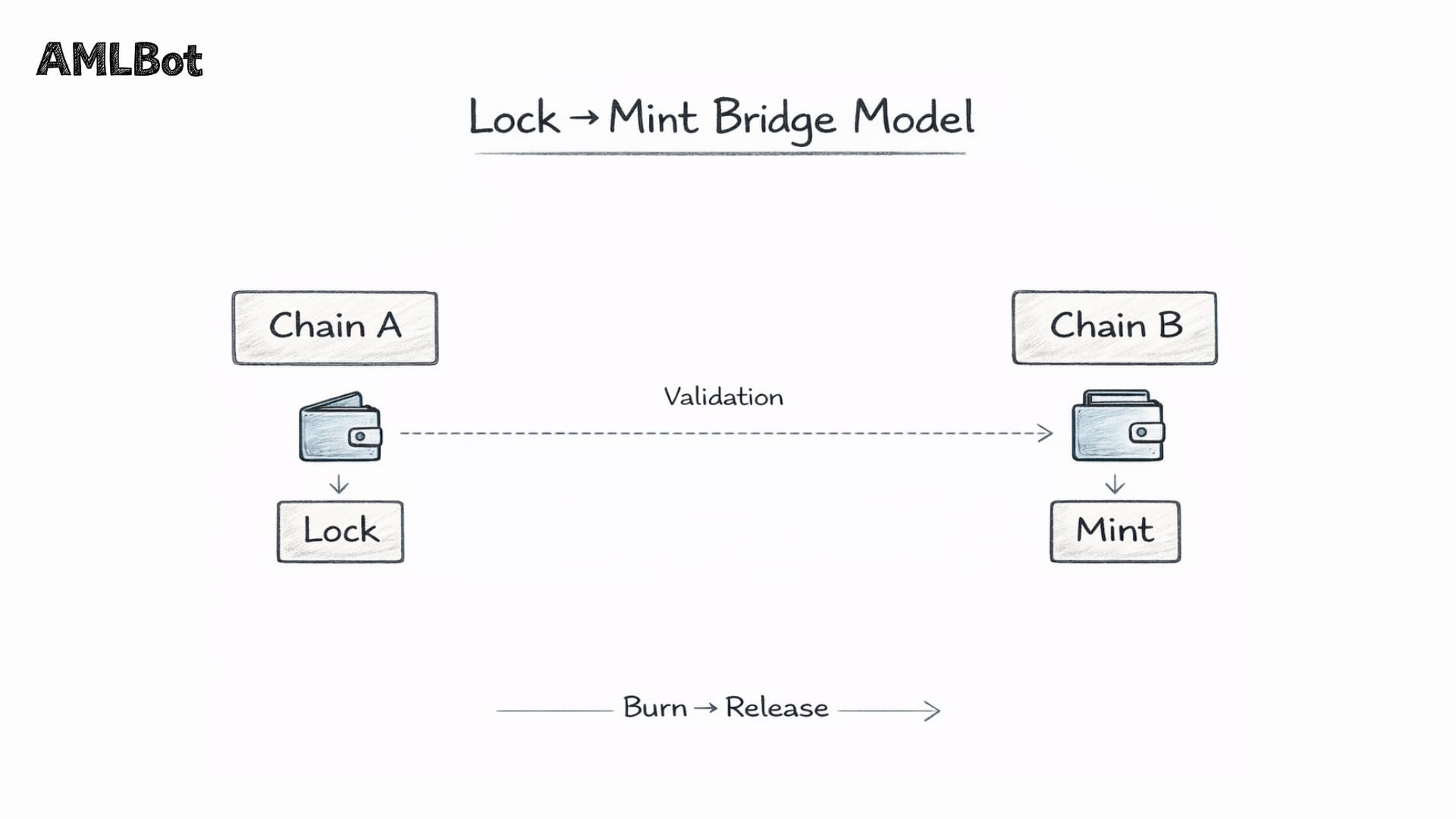
Loss of direct transaction continuity follows from both factors above. In single-chain tracing, each transaction links directly to the next through shared addresses or referenced outputs. Cross-chain transfers break this continuity at every hop. The deposit transaction on the source chain and the mint or release transaction on the destination chain are structurally independent events. They must be correlated through indirect signals, matching values, timing windows, and bridge contract event logs, rather than through any native transactional reference. This inference-based reconstruction introduces uncertainty that direct ledger tracing does not.
Attribution gaps are the cumulative analytical consequence. When an investigator establishes that a wallet cluster belongs to a known entity, that attribution is valid only on the chain where it was built. After a cross-chain transfer to a new network and a fresh address, the established identity does not follow. The destination wallet starts with no transaction history, no connection to known entities, and no behavioral profile. Each hop requires attribution to be re-established on a new network.
The Core Mechanisms Behind Cross-Chain Transfers
Cross-chain movement is not a single technology. It is a family of mechanisms, each operating differently and each creating distinct challenges for transaction tracing. Understanding how assets travel between networks is essential to understanding why reconstruction becomes complex. Three mechanisms dominate the current multi-chain landscape: blockchain bridges, decentralized exchanges, and wrapped token protocols. In practice, these are rarely used in isolation. A single fund flow may pass through all three in sequence.
Blockchain Bridges
📘 Blockchain Bridge is a protocol that enables assets to move between two networks that cannot natively communicate. The dominant architecture is the lock-and-mint model: a user deposits tokens into a smart contract on the source chain, where they are held in escrow. A set of validators or oracles monitors the deposit, confirms it meets the required conditions, and authorizes the minting of an equivalent quantity of tokens on the destination chain. To reverse the process, the minted tokens are burned, and the original assets are released from escrow.
Variations on this model address different technical constraints:
- Burn-and-mint, used by Circle's Cross-Chain Transfer Protocol for native USDC, destroys tokens on the source chain and issues new ones natively on the destination, rather than wrapping them.
- Liquidity-based bridges draw from pre-funded liquidity pools on each supported chain, enabling faster transfers by matching deposits against existing reserves rather than waiting for cross-chain message confirmation.
- Intent-based bridges, used by protocols such as Across, invert the flow entirely: users declare a desired outcome and competitive relayers fulfill the order, with settlement occurring after the fact.
Bridge protocols also differ in their trust architecture. Custodial bridges rely on an intermediary, such as a validator set, multisig group, or centralized custodian, to authorize transfers. Wrapped Bitcoin (WBTC), for example, relies on BitGo to hold the underlying BTC. Non-custodial bridges rely instead on cryptographic verification: smart contracts validate cross-chain messages using mechanisms such as Merkle proofs, light clients, or zero-knowledge proofs.
For tracing purposes, the distinction is structural. Custodial bridges may maintain off-chain records to support correlation, while non-custodial bridges rely solely on cryptographic validation and do not introduce additional identity metadata beyond what the blockchain itself records.
Decentralized Exchanges and Routing
Decentralized exchanges (DEXs) enable token swaps without a central intermediary. Most operate on an Automated Market Maker (AMM) model, executing trades against liquidity pools, smart contracts holding token reserves, without account registration or identity verification.
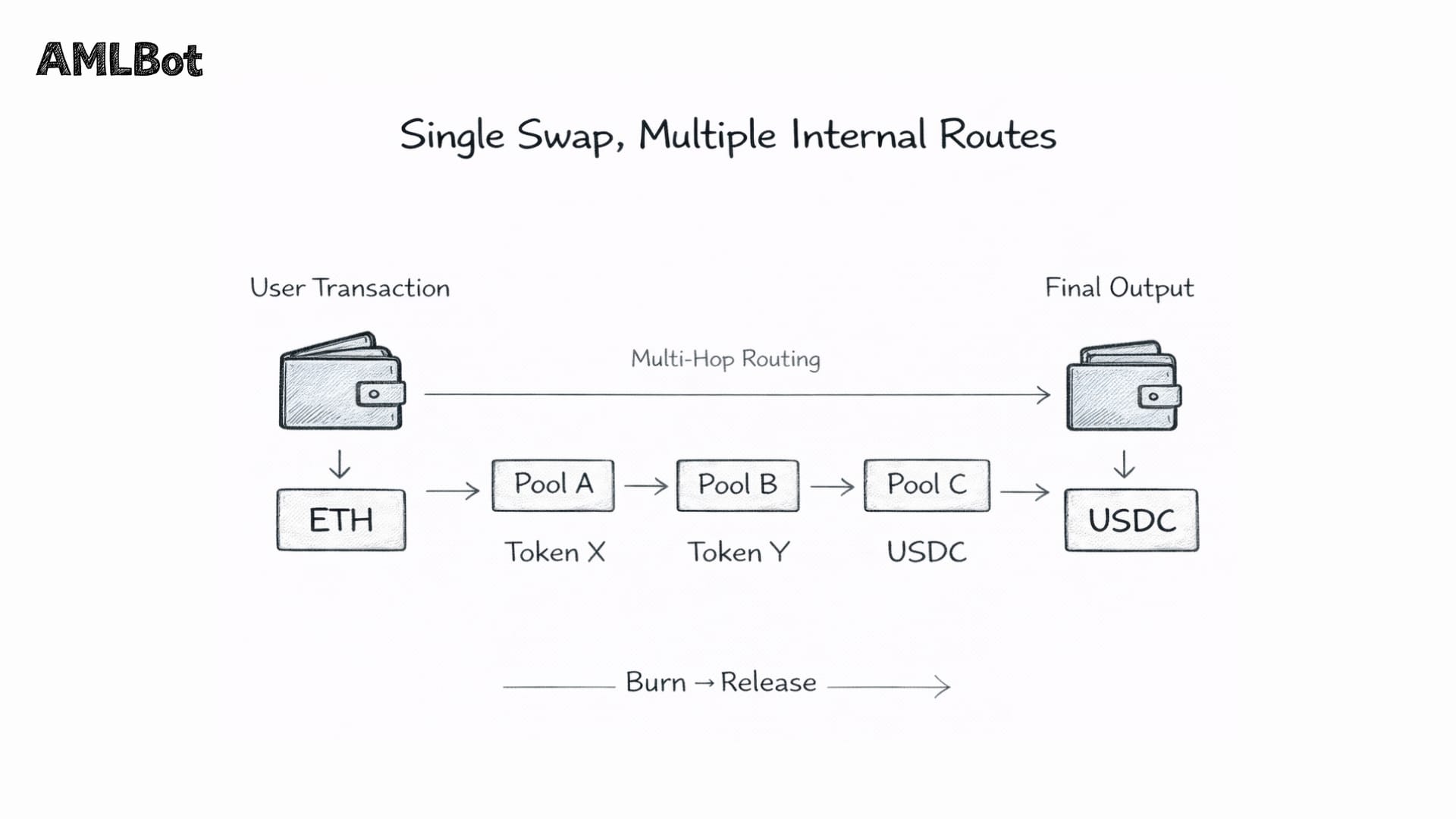
From a tracing perspective, the primary effect is asset transformation. A fund flow entering a DEX as ETH may exit as USDC, DAI, or another token, altering the asset profile even if the transaction remains on the same chain. Multi-step routing increases this complexity. DEX aggregators such as 1inch distribute a single swap across multiple venues and intermediate tokens to optimize execution, meaning one user transaction may internally contain multiple swaps across several liquidity pools.
Even in the absence of deliberate evasion, multi-hop routing fragments the transaction trail and changes asset types, complicating cross-network value correlation. When combined sequentially with bridging mechanisms, these processes materially increase the analytical complexity of reconstruction.
Wrapped Tokens and Asset Representation
A wrapped token is a synthetic representation of an asset from one blockchain issued on another network. It enables value from a non-compatible chain, such as Bitcoin, to circulate within a smart contract ecosystem such as Ethereum. The original asset is held in custody (by a smart contract or centralized custodian), and a corresponding token is issued at a 1:1 peg.
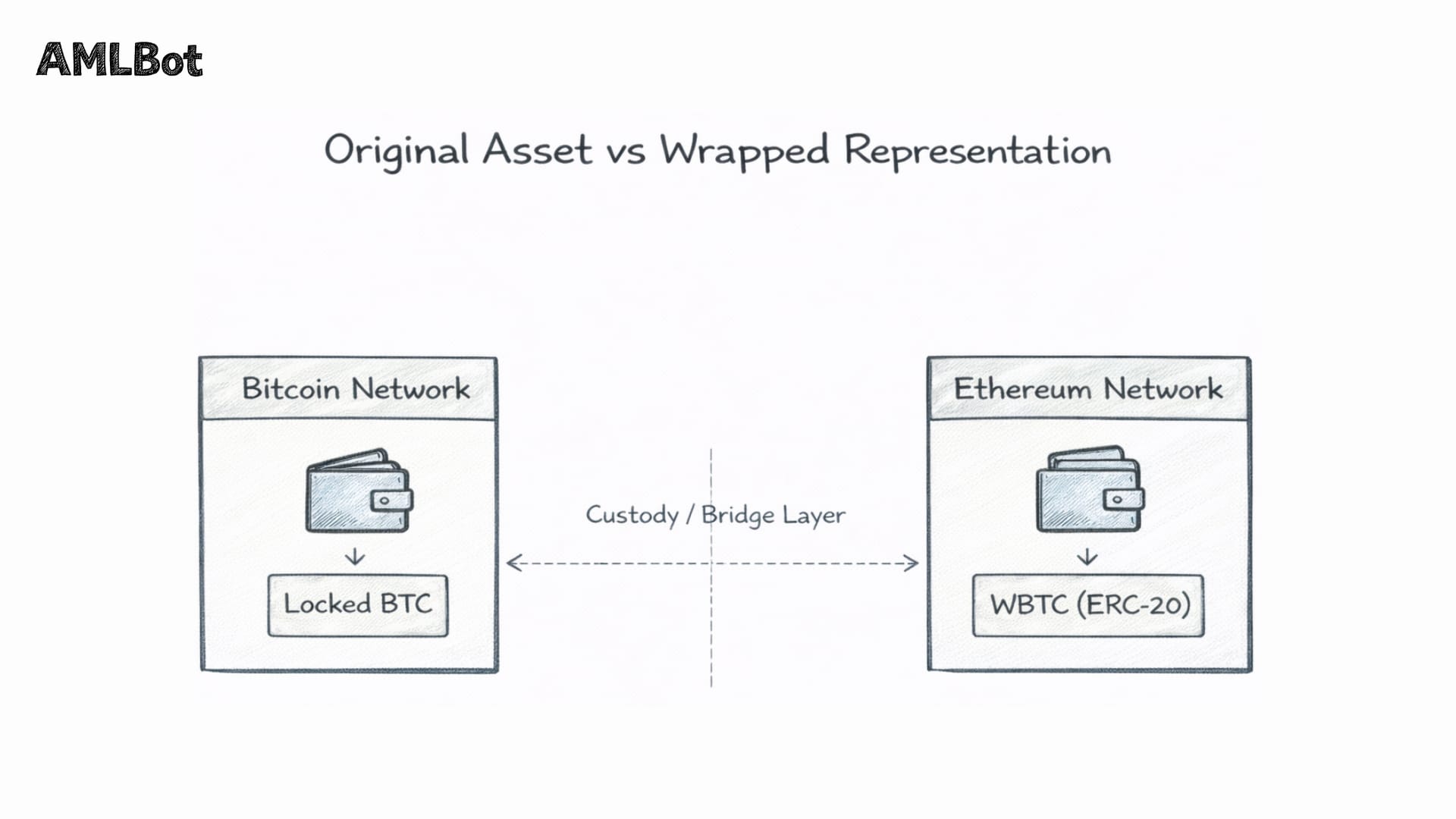
Common Examples:
- Wrapped Bitcoin (WBTC) – an ERC-20 token backed by BTC held by a custodian;
- Wrapped Ether (wETH) – a tokenized representation of ETH conforming to the ERC-20 standard.
Multiple wrapped variants of the same asset may exist across different chains, each with distinct custody and issuance models:
- WBTC – ERC-20 on Ethereum, custodied by BitGo;
- renBTC – formerly issued via Ren Protocol;
- tBTC – backed by a decentralized threshold network;
- BTCB – issued on BNB Chain.
The analytical challenge is structural: the wrapped token and the original asset are separate on-chain objects with no native ledger link. WBTC on Ethereum has its own contract address and transaction history, neither of which appears in the Bitcoin Ledger. The relationship between the locked BTC and circulating WBTC exists within the bridge or custodian framework rather than within either blockchain’s native data.
Correlation across this boundary depends on identifying the relevant lock, mint, or custody relationship and reconstructing the connection across ledgers. When multiple wrapped variants are involved, each representation must be evaluated independently. There is no unified cross-chain view of a single underlying asset.
Cross-Chain Tracing Techniques
Because no native link connects events across separate blockchains, cross-chain tracing relies on correlation rather than direct ledger continuity. Investigators evaluate multiple signals to determine whether activity on one network corresponds to activity on another. These signals differ in strength and reliability.
One foundational indicator is temporal proximity. Cross-chain transfers typically produce paired events: a lock or burn on the source chain and a mint or release on the destination. These occur within a constrained time window defined by bridge design and confirmation requirements. Temporal alignment narrows potential matches but does not, in itself, establish linkage.
Transaction value provides an additional signal. The amount received on the destination network generally reflects the source amount minus protocol and gas fees. Because bridge fee structures follow defined rules, expected outputs can be estimated. Alignment between the timing and the adjusted value strengthens the correlation, though the result remains probabilistic.
When bridge contracts publish structured event logs, contract-level data can support a more direct linkage. Some architectures emit cross-chain message identifiers that appear in both source and destination records, enabling stronger forms of matching. In their absence, correlation relies on indirect indicators.
Liquidity-based bridges introduce further complexity. Transfers are fulfilled from pooled reserves rather than paired deposit-withdrawal events, meaning no single on-chain transaction directly corresponds to another. In such systems, correlation depends on evaluating liquidity inflows, outflows, and rebalancing behavior over time. Conclusions are inherently statistical.
Once funds arrive on a destination network, analysis extends to identifying exit points. Subsequent transfers may lead to centralized exchanges, OTC services, or other identifiable counterparties. Because destination addresses are often newly created, behavioral context becomes relevant, including rapid onward transfers, asset conversion through decentralized routing, or dispersion across multiple wallets. When funds intersect with a Regulated Virtual Asset Service Provider (VASP), the reconstructed flow may connect to the entity's identity records.
Cross-chain tracing, therefore combines temporal, quantitative, structural, and behavioral indicators to produce an inferential reconstruction that must be interpreted within defined confidence levels.
Common Multi-Chain Laundering Patterns
Documented investigations and blockchain intelligence research have identified recurring patterns that exploit structural properties of the multi-chain environment.
Chain hopping is the foundational pattern. It involves moving assets across multiple blockchains in sequence, with each transfer generating a new address, asset format, and transaction history on a separate ledger. Each network crossing requires re-establishing attribution, increasing analytical complexity. Industry research and documented investigations identify chain hopping as a recurrent laundering typology in multi-chain cases.
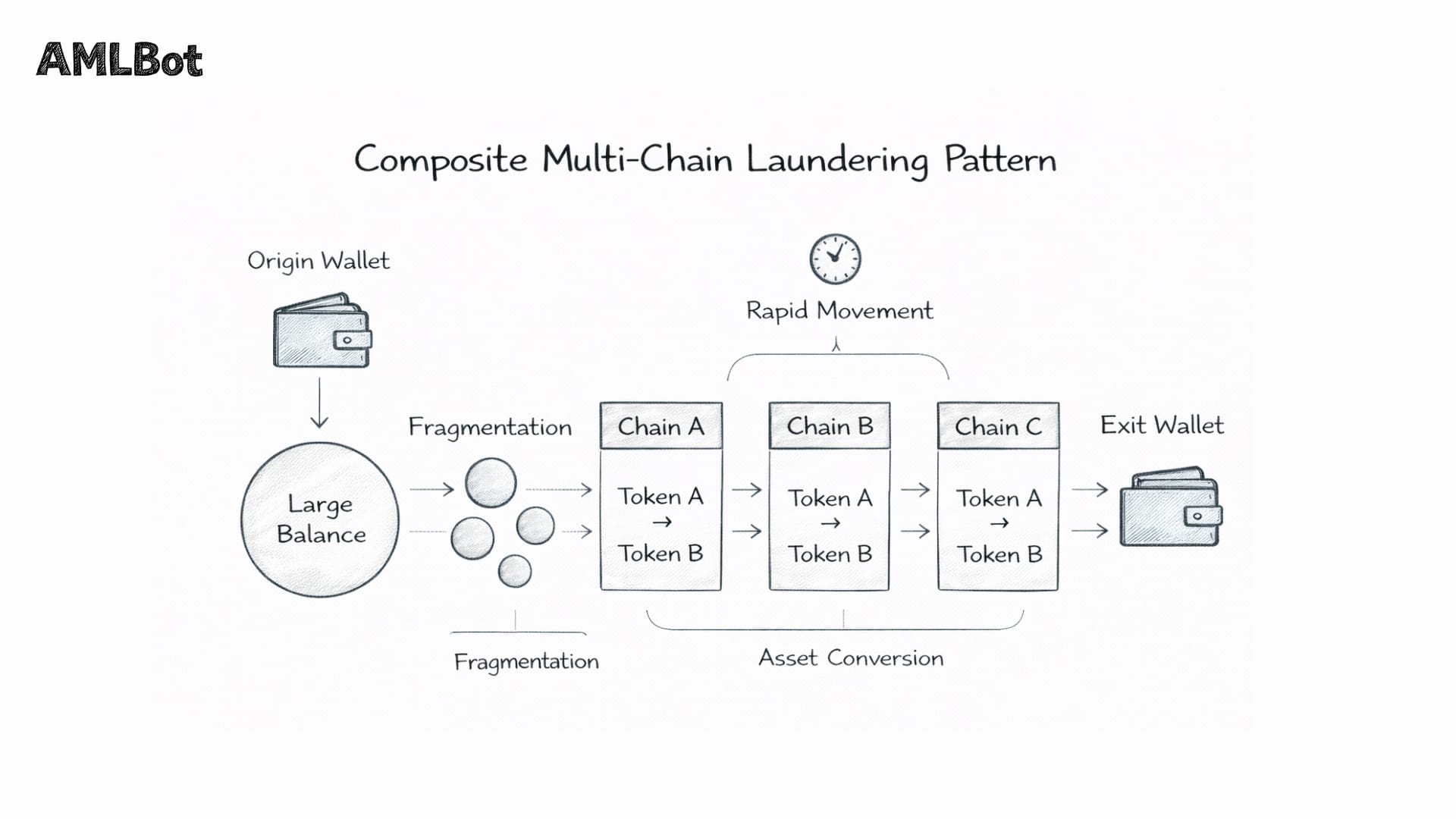
Two structural variants are commonly observed. Sequential hopping moves funds linearly from one chain to another. Parallel hopping splits a balance across multiple chains simultaneously before recombination at a later stage, requiring concurrent analysis across networks.
Bridge-to-DEX Routing combines network transfer and asset conversion in close succession. Funds are bridged to a destination chain and then passed through decentralized exchange swaps. The bridge changes the network context; the swap alters the asset type. As a result, both the address trail and the asset trail are disrupted, and correlation must account for independent structural changes across chains and token formats.
Rapid network switching refers to the tempo of movement rather than its structure. Funds may traverse multiple chains within short time intervals, compressing the window available for monitoring and review. The speed of execution increases the difficulty of real-time detection and correlation across systems that operate with indexing and attribution latency.
Asset fragmentation across chains reduces transaction visibility from a tracing perspective. Instead of moving a large balance in a single transfer, funds are divided into smaller amounts and distributed across multiple networks. On any individual chain, the transactions may appear unremarkable in isolation. Reconstructing the full flow requires aggregating activity across networks and identifying common origin patterns.
In practice, these patterns frequently appear in combination. Fragmentation may precede chain hopping; bridge-to-DEX routing may follow a network transfer; rapid switching may compress the entire sequence into a short timeframe. The analytical challenge lies not in recognizing an isolated tactic, but in identifying the composite structure across chains and asset types simultaneously.
For a deeper explanation of how these tactics combine into full laundering sequences — including chain hopping, bridge-to-DEX routing, mixer use, and fragmentation — see Layering in Crypto AML: How It Works and How to Detect It.
Cross-Chain Analysis vs Standard Transaction Tracing
Transaction Tracing in crypto and cross-chain analysis share the same investigative objective but operate under materially different conditions. They rely on different data environments, apply different correlation methods, and produce conclusions with different evidentiary characteristics.
Standard transaction tracing occurs within a single blockchain. Transactions reference prior outputs, addresses follow a consistent format, and wallet history is maintained in a single continuous ledger. Investigators work within a unified record that can be traversed forward or backward without crossing technical boundaries.
Cross-chain analysis operates across multiple independent ledgers that share no native interoperability. Rather than traversing a single graph, investigators correlate discrete events recorded on separate networks. The two approaches differ across several structural dimensions:
- Data Scope – single-chain tracing evaluates activity within one ledger; cross-chain analysis aggregates activity across multiple independent networks.
- Transaction Continuity – within one chain, continuity is ledger-native; across chains, relationships must be inferred.
- Address Structure – formats remain consistent within a single network; across networks, incompatible schemas require separate handling.
- Asset Identity – the asset being traced remains stable in single-chain analysis; in cross-chain movement, asset representation may change at each network boundary.
- Attribution Confidence – single-chain conclusions rely on native transaction references; cross-chain conclusions depend on the strength of multi-network correlation.
- Analytical Complexity – single-chain tracing involves linear graph traversal; cross-chain analysis requires multi-ledger reconstruction with uncertainty compounding at each hop.
The difference is therefore not only technical but probabilistic. Single-chain tracing rests on directly recorded ledger relationships. Cross-chain analysis reconstructs relationships across systems that do not natively reference one another. Each additional network boundary introduces correlation risk, and confidence levels must be assessed accordingly rather than assumed to be ledger-native.
Limitations and Analytical Challenges
Cross-chain tracing operates under structural constraints that no methodology fully eliminates. Investigators must understand not only what can be established, but also where conclusions become probabilistic rather than definitive. Regulatory guidance reflects this reality.
The Financial Action Task Force (FATF), in its Updated Guidance for a Risk-Based Approach to Virtual Assets and Virtual Asset Service Providers (2023), states that jurisdictions and obliged entities must assess “the technological features that may enable anonymity or obfuscation of virtual asset transfers.” In practical terms, this includes cross-chain routing, bridge usage, and multi-network transfers that fragment transaction records. Compliance programs are therefore expected to evaluate such activity as part of ongoing monitoring, even where technical linkage is inferential rather than deterministic.
Incomplete visibility remains a primary limitation. No analytics platform monitors every active blockchain. While leading systems track dozens of networks, the broader ecosystem includes hundreds of chains, including newer Layer 2 and application-specific environments. Any fund flow that passes through an unmonitored network creates a gap that cannot be reconstructed solely through inference.
Bridge opacity introduces further constraints. Protocols vary widely in the quality of on-chain documentation they provide. Some emit structured and consistent event logs, enabling stronger correlation. Others rely on incomplete documentation, off-chain custodial records, or liquidity-pool mechanisms that do not pair deposits with specific withdrawals. In such cases, reconstruction depends on statistical inference rather than deterministic linkage.
Transaction volume creates additional complexity. High-throughput bridge protocols generate large numbers of potential candidate matches within plausible timing windows. As volume increases, the probability of false correlations rises. Revisions to previously reported illicit volume estimates over the past few years illustrate the difficulty of precise attribution at scale when cross-chain activity is incorporated into analysis.
False correlations represent the central analytical risk. Where linkage is based on timing and value alignment rather than a shared cross-chain identifier, conclusions are inherently probabilistic. Academic research on well-documented EVM-compatible bridges has shown high deposit-matching rates but lower withdrawal rates, demonstrating that, even under favorable conditions, attribution is not exact. Across heterogeneous chains or less transparent bridge architectures, confidence declines further.
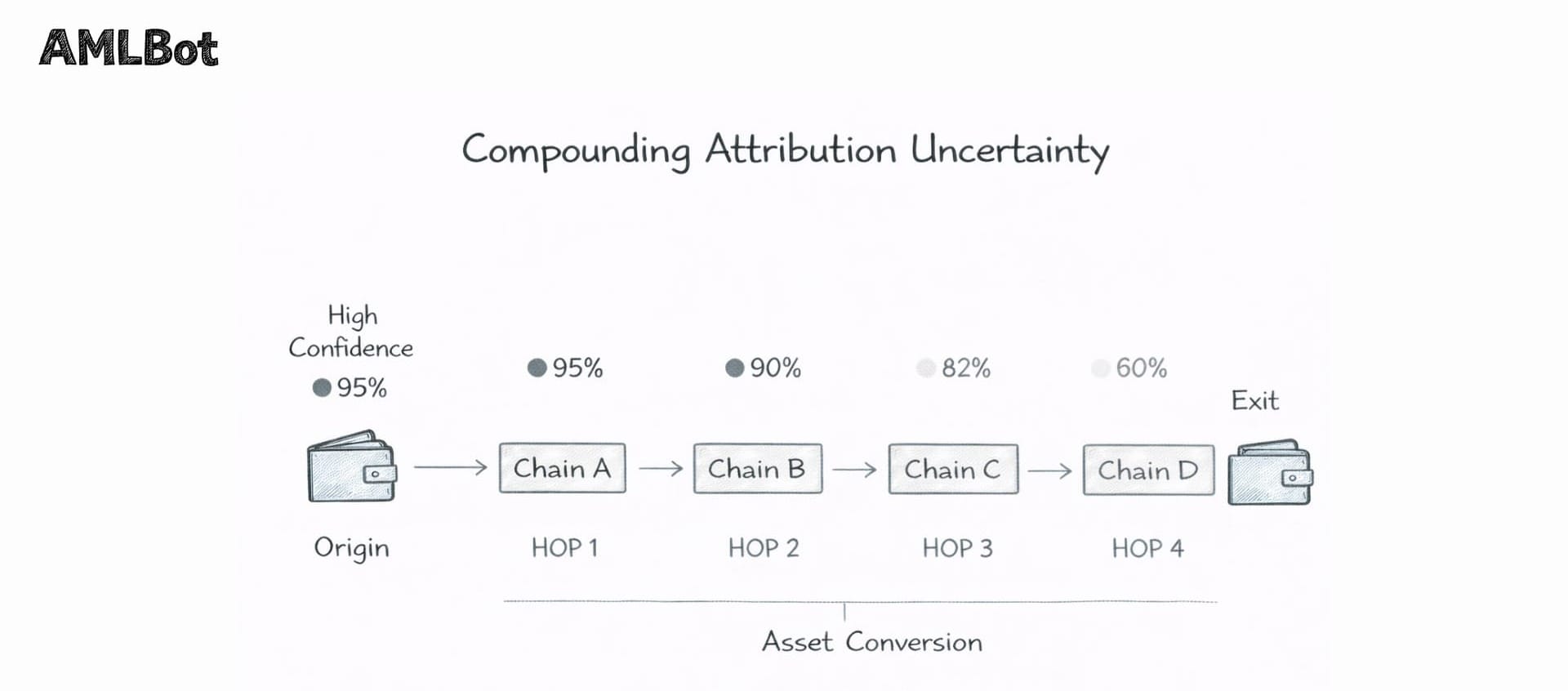
Uncertainty compounds with each additional network boundary. A reconstruction spanning multiple chains aggregates the confidence level of each hop, meaning overall attribution reliability decreases as the path length increases. Cross-chain analysis, therefore, produces evidentiary conclusions that require explicit confidence assessment rather than assumption of ledger-native certainty.
When Cross-Chain Analysis Escalates to Investigation
Routine cross-chain monitoring generates risk signals, most of which resolve through standard compliance review. Escalation to formal investigation occurs when the overall structure of multi-chain activity suggests deliberate obfuscation rather than ordinary bridge or DeFi usage.
Indicators that may warrant escalation include rapid movement across multiple networks, bridge withdrawals to newly created addresses followed by immediate onward transfers, fragmentation of funds across chains, routing through high-risk protocols, or interaction with sanctioned or previously flagged entities. No single factor is determinative; escalation decisions should be based on the overall structure of cross-chain fund flows.
Once escalation is initiated, the analytical objective shifts from monitoring to structured reconstruction. The workflow centers on assembling the complete multi-chain path and correlating bridge events, asset transformations, and address clusters across all involved networks. The reconstruction must identify intermediate addresses, asset conversions, and exit points, and document the confidence level for each cross-chain linkage.
The next phase involves counterparty identification. Where funds intersect with exchanges, OTC services, or other virtual asset service providers (VASPs), those entities may become the focus of compliance inquiries or formal legal requests. At this stage, analytics transitions into the broader crypto scam fund tracing process, which integrates technical reconstruction with regulatory reporting and legal coordination.
Because cross-chain linkage is inferential rather than ledger-native, evidentiary preparation is critical. Investigative documentation should record the methodology applied, the analytical basis for each correlation, alternative interpretations considered, and the limitations affecting confidence levels. Courts and regulators increasingly scrutinize how cross-chain attribution conclusions are reached, and overstating certainty introduces material evidentiary risk.
Cross-chain investigation, therefore, requires not only technical reconstruction but disciplined documentation capable of supporting regulatory or judicial review.
Tools Used in Cross-Chain Analysis
Effective cross-chain analysis depends on infrastructure capable of ingesting heterogeneous blockchain data, correlating activity across independent ledgers, and monitoring bridge activity in real time. Three core capabilities define this tooling environment: multi-chain data aggregation, cross-network graph correlation, and bridge monitoring systems.
Multi-chain data aggregation forms the foundational layer. Transaction data from each supported network must be collected, decoded, and normalized into a unified schema before correlation can occur. While EVM-compatible chains share structural similarities, non-EVM networks require separate ingestion and normalization pipelines. The output is a consolidated multi-chain dataset that enables cross-network queries without manual reconciliation across separate explorers.
Cross-network graph correlation builds on this aggregated data. Address graphs are constructed across all monitored chains, allowing bridge deposits and corresponding withdrawals to be linked within a unified analytical environment. Once stitched together, fund flows can be traversed across network boundaries as a single reconstructed path. Entity attribution layers, including labeled exchanges, sanctioned wallets, and high-risk services, are incorporated into the graph to identify counterparty risk when fund flows reach known entities.
Platforms implementing this capability vary in coverage depth and supported networks. Commercial systems integrate multi-chain ingestion, correlation engines, and attribution databases into a single environment. Tools such as the AMLBot Tracer provide cross-network visualization of fund flows and case mapping across major blockchain ecosystems.
Bridge monitoring systems complement correlation engines by indexing lock, mint, burn, and release events as they occur. Real-time surveillance of bridge contracts enables risk scoring at the point of transfer rather than after funds have moved further downstream. These systems maintain protocol-level intelligence, including event schemas and fee structures, which support more accurate cross-chain matching.
Open-source tools and academic frameworks also contribute to the ecosystem, offering transparent methodologies for clustering and bidirectional tracing where independent verification is required.
Conclusion
The multi-chain ecosystem is no longer transitional. It is the operating structure of modern crypto markets. Assets move routinely across independent networks through bridges, decentralized exchanges, and wrapped asset protocols. Tracing that activity now requires navigating a fragmented, cross-ledger environment as a matter of course.
Cross-chain analysis has therefore become a core component of modern blockchain analytics. Monitoring a single network in isolation produces an incomplete reconstruction whenever assets cross chain boundaries. In a landscape where multi-chain routing is routine, single-chain visibility is insufficient.
Cross-chain analysis does not eliminate uncertainty, but it restores continuity. It provides a structured method for correlating activity across networks that do not natively reference one another. Without it, tracing may stop at the first bridge boundary. With it, investigators can reconstruct fund flows across the full multi-chain path and assess risk exposure across the environments where value actually moves.
In a multi-chain ecosystem, cross-chain capability is necessary for tracing that seeks to reconstruct fund flows across network boundaries.
-AMLBot Team

FAQ
What Is Cross-Chain Analysis in Crypto?
Cross-chain analysis traces crypto transactions across multiple blockchains. It reconstructs fund flows when assets move between networks via bridges, wrapped tokens, or decentralized exchanges.
Why Does Cross-Chain Movement Complicate Transaction Tracing?
Each time assets move to a new blockchain, transaction continuity breaks. Funds fragment across separate ledgers, assets change form at bridge points, and attribution does not automatically transfer between networks. Analysts must correlate events manually rather than rely on native ledger links.
How Do Blockchain Bridges Affect Fund Flow Analysis?
Bridges transfer assets using models such as lock-and-mint or burn-and-mint, creating related transactions across different chains. Because no native cross-chain identifier exists, analysts must correlate timestamps, amounts, and bridge event logs to reconstruct the movement.
What Are Wrapped Tokens in Cross-Chain Analysis?
Wrapped tokens represent assets from one blockchain on another network (e.g., WBTC on Ethereum). The wrapped token and the original asset are separate on-chain objects, linked only through custodian or bridge records, which complicates attribution.
What Is Chain Hopping?
Chain hopping is the practice of moving assets across multiple blockchains in sequence. Each hop creates a new address and transaction history. It can occur linearly (sequential hopping) or through fund splitting across several chains before recombination (parallel hopping).
Can Cross-Chain Analysis Identify Wallet Owners?
Cross-chain analysis does not directly reveal identities. However, it can correlate activity across networks and attribute wallets to known entities such as exchanges or services based on transaction behavior.
What Are the Main Challenges of Cross-Chain Tracing?
Cross-chain tracing faces fragmented ledgers, limited bridge transparency, high transaction volumes, attribution gaps on new networks, and compounding uncertainty across multiple hops. Even under favorable conditions, tracing accuracy is not absolute.
How Do Decentralized Exchanges Impact Cross-Chain Analysis?
DEXs change asset types through liquidity pools without identity verification. Multi-step routing and bridge-to-DEX patterns break both network and asset continuity, requiring independent correlation of swap and bridge events.
When Does Cross-Chain Analysis Become Part of an Investigation?
It becomes necessary when transaction patterns suggest deliberate obfuscation, such as rapid movement across multiple networks, bridge withdrawals to fresh addresses, or known laundering typologies. At that point, full multi-chain reconstruction is required.
Why Is Cross-Chain Analysis Important for Crypto Businesses?
As laundering increasingly occurs across multiple blockchains, monitoring a single network leaves compliance blind spots. Cross-chain analysis enables businesses to assess risk exposure across ecosystems and meet evolving regulatory expectations.