How to Avoid Crypto Scams in 2026: Warning Signs and Prevention Checklist
Crypto scam losses reached an estimated $12 billion in 2024, and in 2025 that number climbed past $14 billion on-chain. The trend heading into 2026 is clear: crypto fraud is growing faster than the crypto market itself.
While scammers often tailor their approach to older adults and people with limited technical experience, anyone can be a victim – even high-end finance professionals. Evidently, in 2023, Shan Hanes, CEO of Heartland Tri-State Bank in Kansas and a former board member of the American Bankers Association, embezzled $47.1 million from his own bank after falling for a pig butchering scam. The patterns repeat, the mechanics evolve, and the sophistication of scams keeps rising, especially with the rise of generative AI.
This article breaks down the most common crypto scam types in 2026, the warning signs that cut across all of them, and a concrete checklist you can use before sending any funds.
Why Crypto Scams Are Increasing in 2026
Several structural factors are making 2026 a particularly dangerous year for crypto fraud.
Blockchain transactions are irreversible. Once funds leave your wallet, there's no bank to call and ask for chargeback. This makes crypto the ideal payment medium for scammers – the moment a victim sends funds, recovery becomes extremely difficult. The pseudonymous nature of wallet addresses means the person receiving your money may be impossible to identify without specialized blockchain analysis.
Then there's the AI factor. Generative AI tools have made scam operations dramatically more scalable and convincing. Chainalysis reported that AI-enabled scams generated an average of $3.2 million per operation in 2025, roughly 4.5 times the revenue of traditional fraud schemes.
The DeFi ecosystem adds another layer of risk. Smart contracts interact with user wallets in ways that most people don't fully understand. A single malicious token approval can grant a contract permission to drain an entire wallet. The speed of these transactions, often completed in minutes or even seconds, gives victims no window to react.
Social engineering ties all of these together. Modern crypto scams rely less on technical exploits and more on manipulating human decision-making – creating urgency, faking authority, and building trust over weeks or months before directing victims to fraudulent platforms.
Most Common Types of Crypto Scams
Understanding how different scam structures work makes them easier to recognize early. Most crypto fraud falls into a handful of repeating categories, each targeting a different point in the decision-making process.
Phishing and Wallet Drainer Attacks
Phishing in crypto works differently from traditional email phishing. The goal isn't usually to steal a password – it's to get you to sign a malicious transaction. Wallet drainer attacks typically appear as fake airdrop claims, NFT minting pages, or DeFi protocol interfaces. The user connects their wallet, approves what looks like a routine transaction, and unknowingly grants the contract permission to transfer all tokens of a given type.
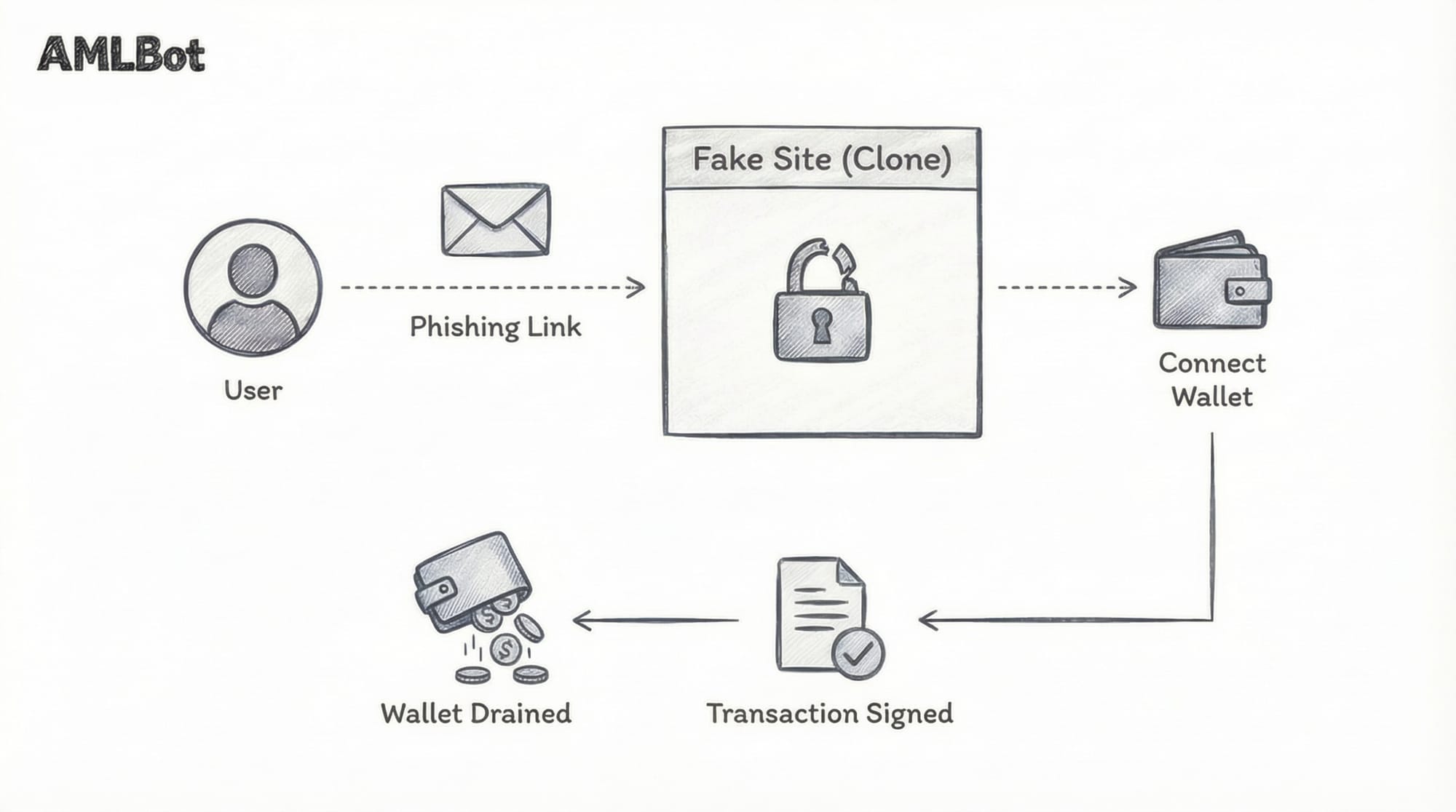
CertiK's 2024 security report recorded over $1.05 billion in losses from phishing attacks across 296 on-chain incidents – a 331.03% increase from 2023. While wallet drainer losses dropped 83% in 2025 (to around $84 million, down from $494 million in 2024), the drainer ecosystem remains active and the attack pattern is still common.
Address poisoning is a related threat. Scammers send tiny transactions from addresses that look almost exactly like ones the victim has previously interacted with, counting on the victim to copy-paste the wrong address when making future transfers. One trader lost $50 million in USDT to this technique in a single incident in December 2025.
Fake Investment Platforms and High-yield Schemes
These scams promise fixed or guaranteed returns on crypto deposits. The platforms often look polished – professional dashboards, live trading charts, even working chat support. Some even allow small withdrawals to build confidence before locking out users once they deposit larger amounts.
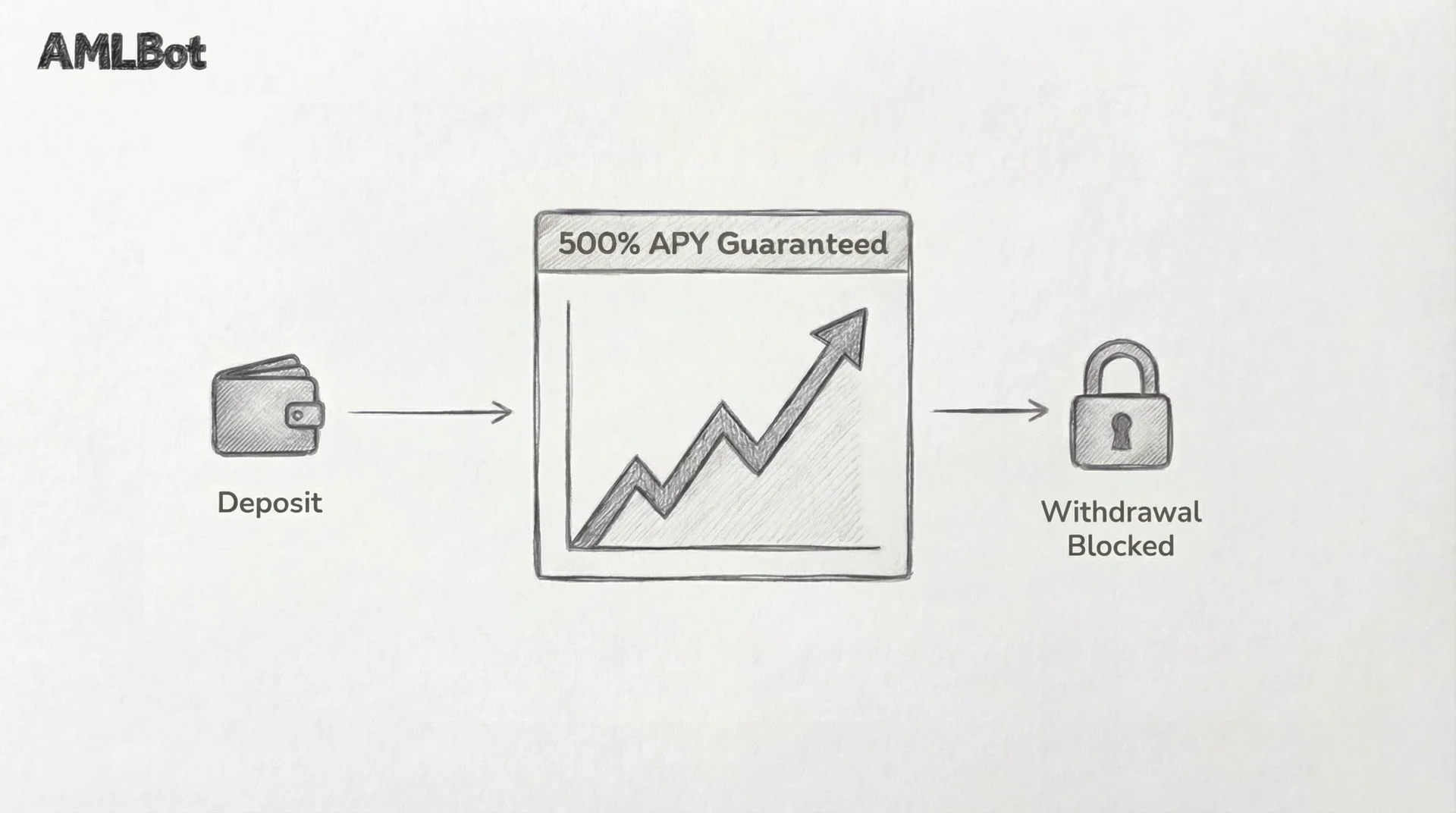
The FBI reported $5.8 billion in crypto investment fraud losses in 2024, making it the largest category of cybercrime by dollar amount. High-yield investment programs remain among the top scam categories by revenue globally. The core mechanics are always the same: promise unrealistic returns that no legitimate investment can deliver, show fabricated gains in a fake dashboard, and make it progressively harder to withdraw.
The mistake users most commonly make here is treating the platform's own interface as proof of performance. A dashboard showing 200% returns means nothing if the platform controls what the dashboard displays.
Romance and Social Engineering Scams
"Pig butchering" scams are the most financially devastating category in crypto fraud. The name comes from the practice of "fattening the pig" – scammers invest weeks or months building a personal relationship with the victim before steering the conversation toward crypto investments. Revenue from these schemes grew 40% year-over-year in 2024.
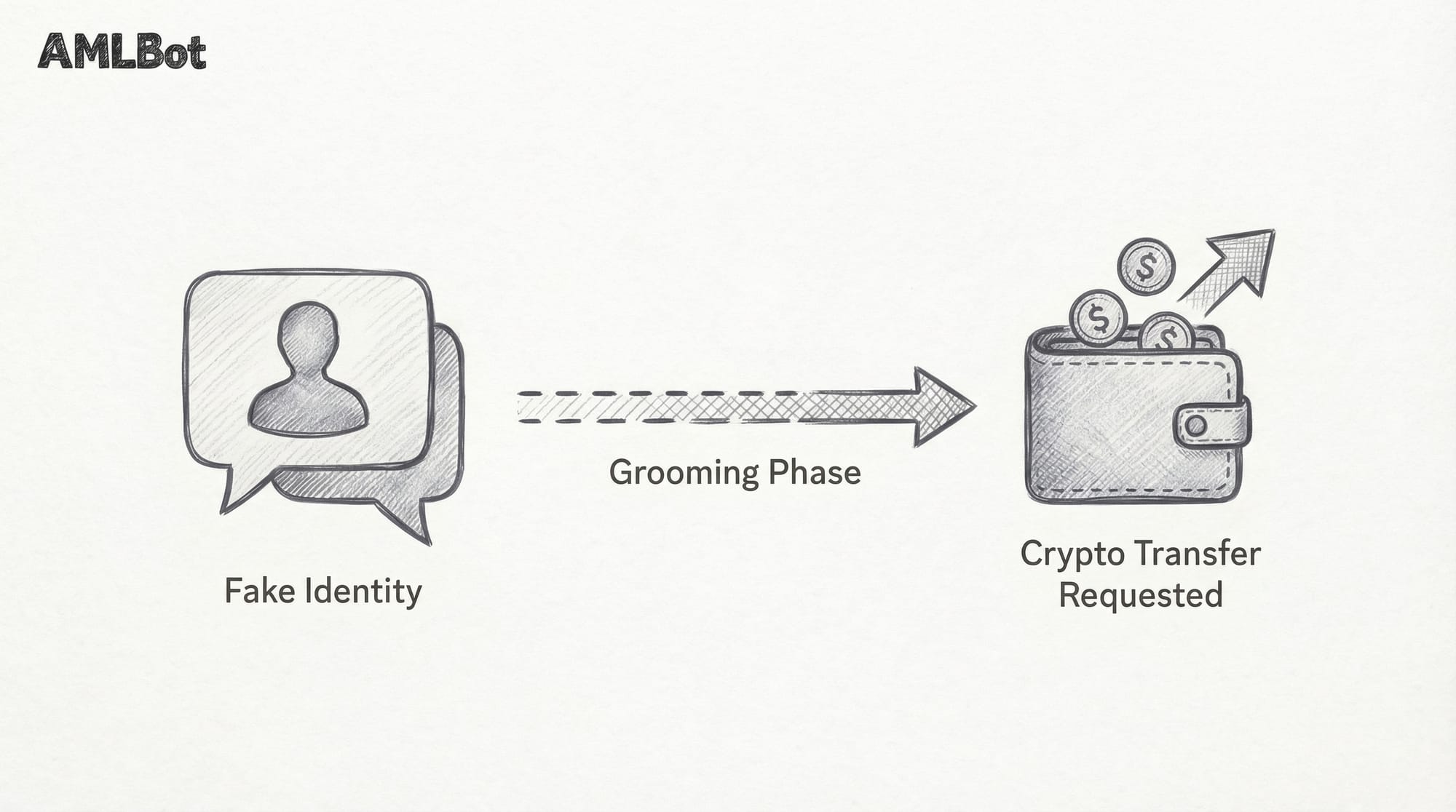
The human cost goes beyond financial loss. A University of Texas study traced over $75 billion flowing from victims to crypto exchanges through pig butchering between 2020 and early 2024. The UN estimates over 200,000 people are held in forced-labor scam compounds across Southeast Asia, running these operations at industrial scale.
The investment pitch never comes first. The relationship does. By the time money enters the conversation, the victim is emotionally invested and less likely to verify independently.
Impersonation and Deepfake Scams
AI-generated deepfakes have transformed impersonation fraud. Scammers produce realistic video and audio of public figures endorsing crypto investment platforms. An 82-year-old retiree named Steve Beauchamp drained his entire retirement account – over $690,000 – after watching a deepfake video of Elon Musk endorsing a fraudulent investment platform. The scammers used AI to replace Musk's voice and lip movements in a genuine interview.
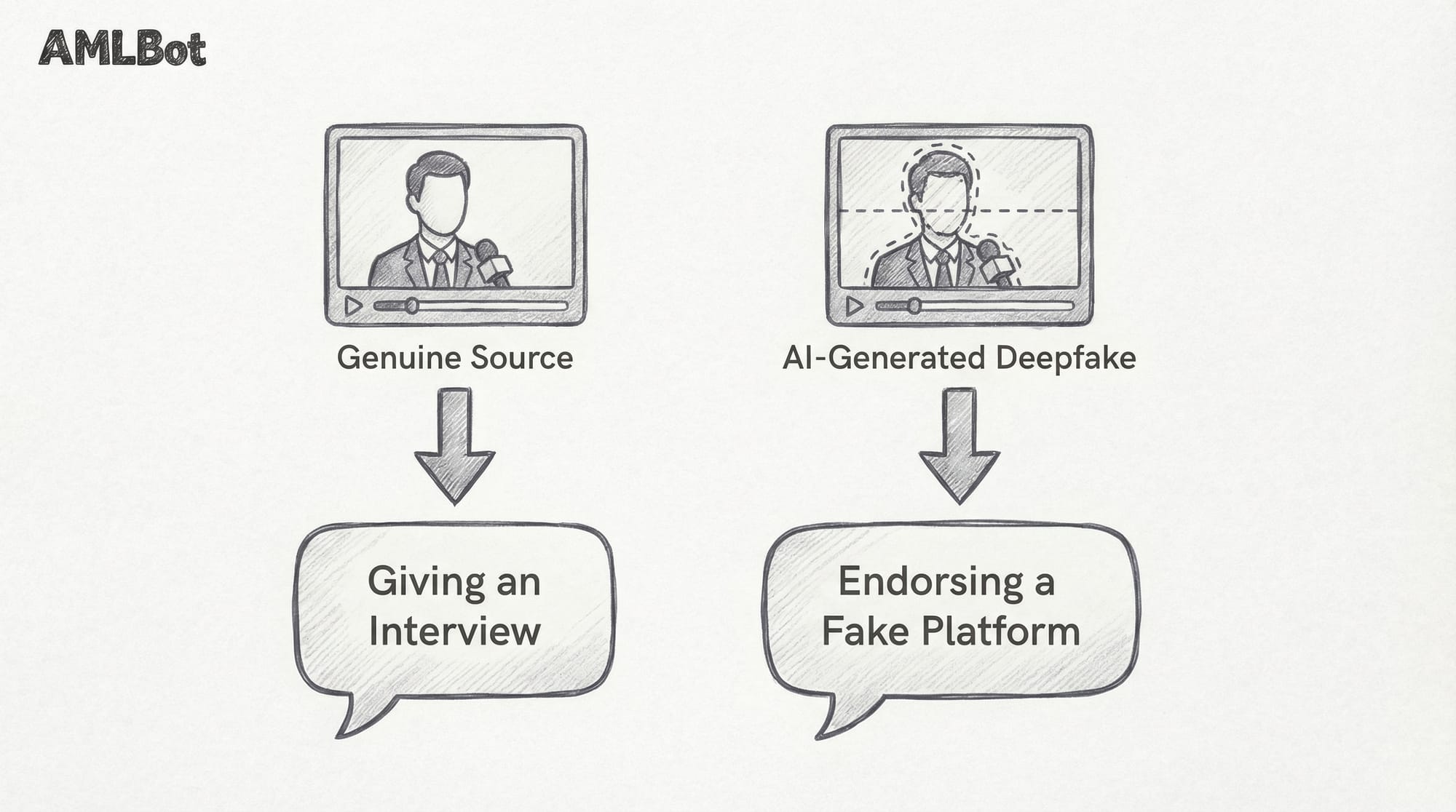
The threat extends beyond celebrity impersonation. Scammers clone the voices and likenesses of company executives, customer support agents, and even personal contacts.
A 2025 iProov study found that only 0.1% of participants correctly identified all fake media presented to them, which is why you shouldn’t trust what you see and hear without confirming identity through a separate channel. If someone on a video call asks you to send crypto, call them on a number you already have – not the one they provide. If you see a famous public figure endorsing an investment platform, check if the advertiser or the publication channel is legit.
Fake Exchanges and Withdrawal Freezing Schemes
Some fraudulent platforms don't steal funds immediately. Instead, they operate as seemingly functional exchanges until the user tries to withdraw a meaningful amount. At that point, the platform introduces new "requirements" – tax deposits, verification fees, insurance charges, anti-money-laundering compliance fees. Each payment unlocks a new demand. The funds were never in the user's control to begin with.
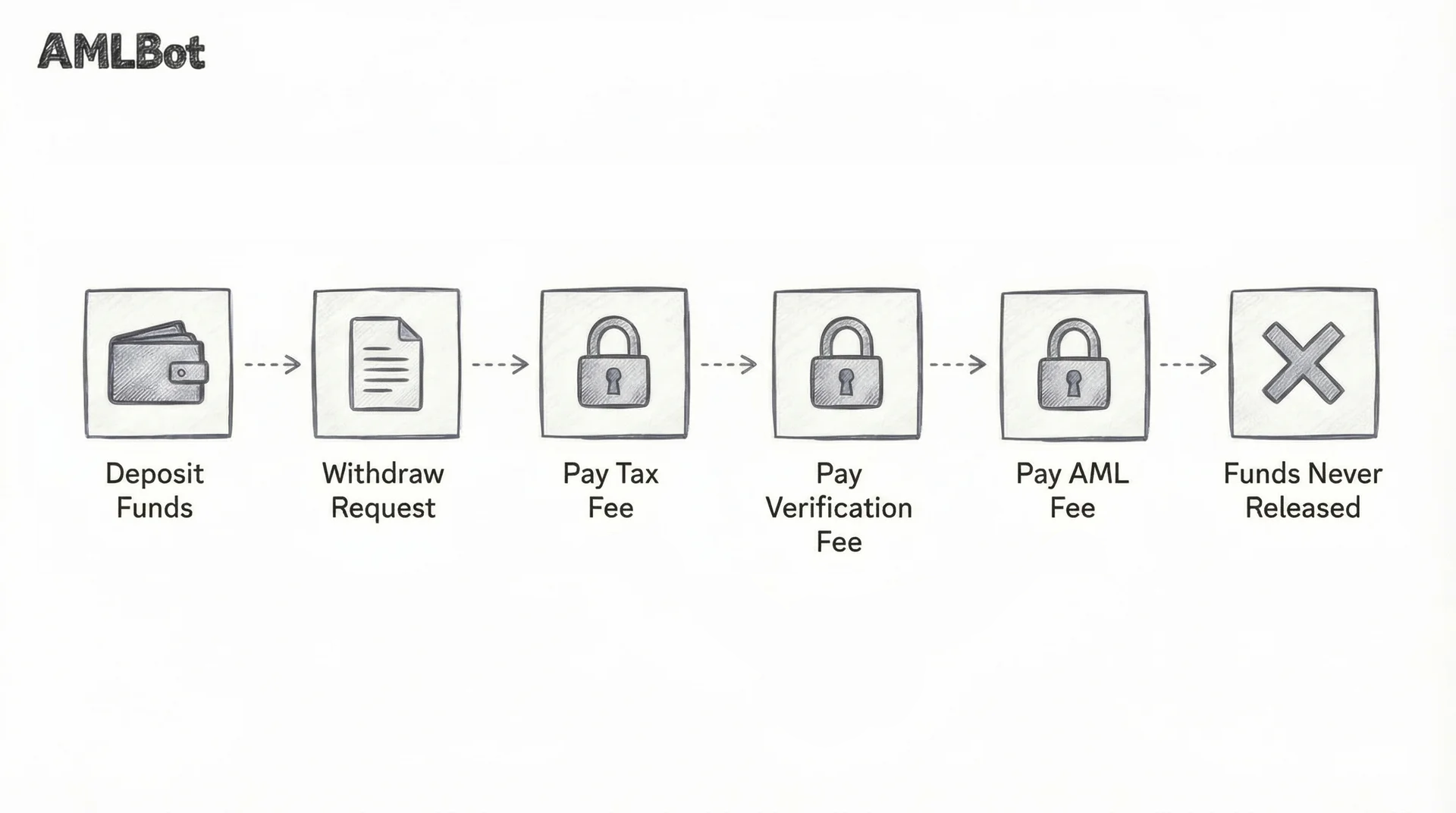
The warning sign is any platform that requires additional payments to process a withdrawal. Legitimate exchanges deduct fees from the withdrawal itself – they don't ask you to give them more money to access your own funds.
Rug Pulls and Token Exit Scams
Rug pulls happen when a project's developers drain liquidity or dump their token holdings after building up a community and attracting investment. The frequency of rug pulls dropped 66% in early 2025 compared to the same period in 2024, but the financial impact per incident has grown enormously. Take the Mantra OM token collapse in April 2025, for example. The token fell from $6.35 to $0.37 after 17 wallets moved 43.6 million tokens to exchanges, and that collapse alone accounted for roughly 92% of all rug pull losses in Q1 2025.

Before investing in any token, check whether the smart contract is verified and whether liquidity is locked. If the project team can withdraw all liquidity at any time, they probably will.
Key Warning Signs of a Crypto Scam
Scam structures vary, but the red flags are remarkably consistent. These are the signals worth watching for across every type of crypto fraud:
- Guaranteed returns: No legitimate crypto investment can guarantee profits. Any platform or person promising fixed, risk-free returns is either lying or running a Ponzi structure. This is the single most reliable indicator of fraud.
- Urgency and pressure: Scammers manufacture time pressure because it prevents independent verification. Phrases like "limited spots," "offer expires tonight," or "act now before the price jumps" are psychological triggers, not investment advice. Legitimate opportunities don't disappear because you took a day to think about them.
- Requests for private keys or seed phrases: Legitimate services, exchanges, or support agents will never ask for your seed phrase or private key. Anyone who does is attempting to steal your funds. Full stop. This applies to customer support chats, social media DMs, and even people claiming to be from your wallet provider.
- Unverified or newly registered domains: Scam platforms frequently use domains registered within the past few months. Check domain age through a WHOIS lookup. Cross-reference the domain against the project's official social media channels. If the URL is slightly misspelled, treat it as hostile.
- Sudden platform restrictions on withdrawals: As described in the fake exchange section above, any platform that requires additional deposits to process withdrawals is almost certainly fraudulent. Legitimate exchanges charge withdrawal fees, but they deduct those fees from the transaction – they don't require fresh deposits.
- Untraceable or anonymous team members: Look for real names, verifiable professional histories, and LinkedIn profiles that predate the project by years. AI-generated headshots, pseudonymous founders with no prior track record, and teams with no public presence are all red flags.
If you suspect you've already been affected, see AMLBot’s guide on how to recover stolen cryptocurrency.
Crypto Scam Prevention Checklist
Before investing or sending crypto, ask yourself:
- Have I verified the domain and company registration? Check domain age, business registration records, and whether the URL matches official sources.
- Is the project promising unrealistic returns? If it sounds too good to be true for a volatile asset class, it probably is.
- Have I checked independent reviews? Look beyond the project's own channels. Search for the project name combined with "scam," "complaint," or "withdrawal problems."
- Am I being pressured to act immediately? If someone is creating urgency around a financial decision, slow down. That urgency is the manipulation.
- Has anyone asked for my seed phrase or private key? If yes, stop communication. Immediately.
- Did I independently confirm the person's identity? For any contact recommending an investment, verify their identity through a separate channel.
- Have I tested with a small transaction first? Before committing significant funds to any new platform, send a minimal amount and confirm you can withdraw it without friction or additional fees.
- Is the smart contract verified? On-chain verification through a block explorer is a minimum requirement. Unverified contracts can contain hidden functions that drain funds.
- Do I understand where my funds are going? If you can’t explain the path your crypto takes after you send it, you probably shouldn't be sending it.
- Would I still invest if I removed emotional pressure? Strip away the relationship, the urgency, and the social proof. If the investment doesn't stand on its own fundamentals, walk away.
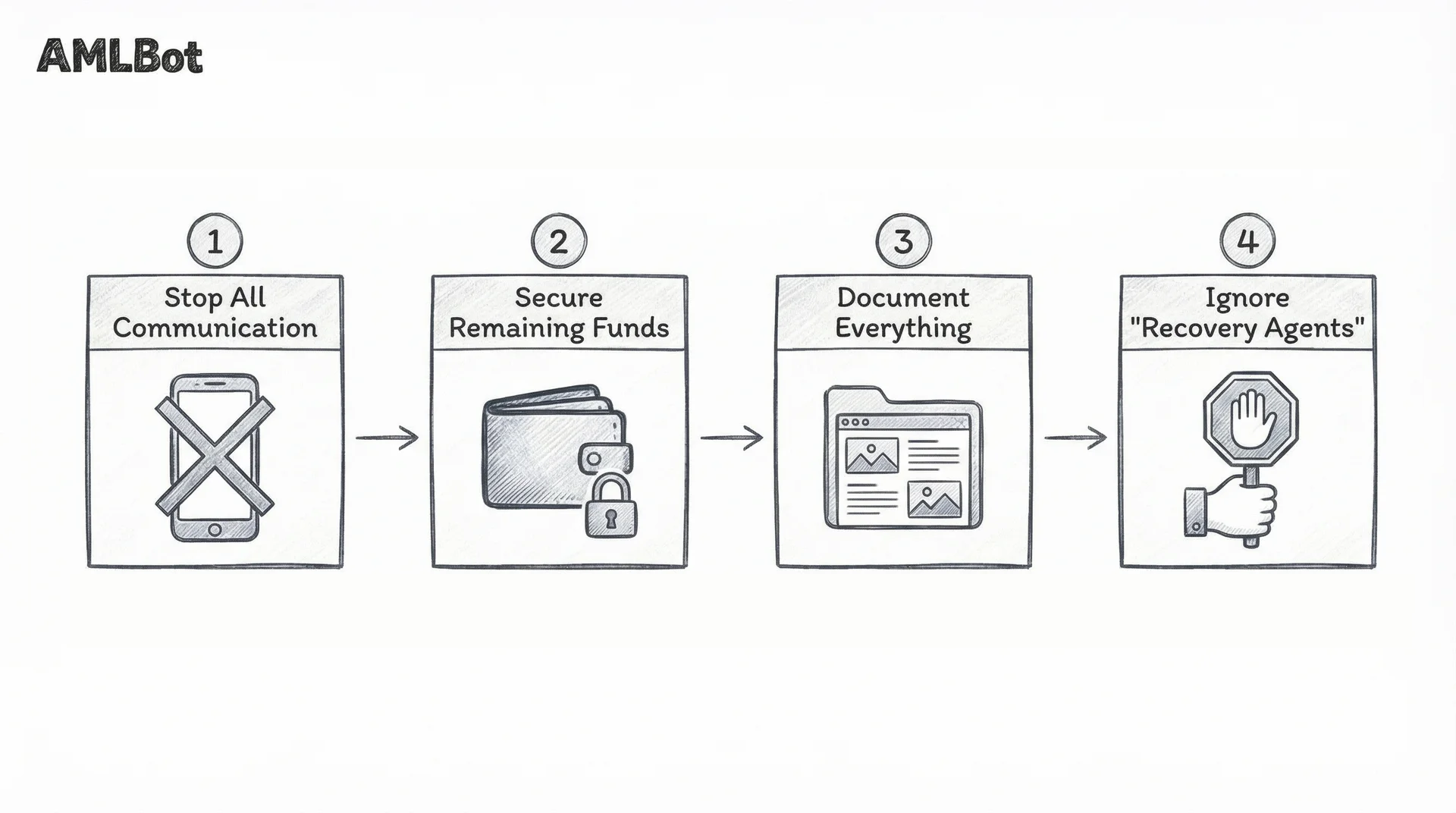
What to Do If You Realize It's a Scam
If you suspect you're dealing with a fraudulent platform or person, act quickly. The faster you respond, the more options remain available.
- Stop all communication. Do not respond to further messages from the suspected scammer. Don't explain why you're stopping, and don't engage with any "recovery" offers that come from the same source.
- Secure your remaining funds. If you've shared wallet credentials or signed suspicious transactions, move your remaining assets to a new wallet immediately. Revoke any token approvals you don't recognize using a tool like revoke.cash.
- Document everything. Screenshot all conversations, transaction hashes, wallet addresses, platform URLs, and email exchanges. This information is critical if you pursue blockchain investigation or file a law enforcement report.
- Do not pay "recovery agents." The recovery scam is a second-stage fraud that targets people who've already lost money. Anyone contacting you unsolicited about recovering stolen crypto is likely running another scam. Legitimate blockchain investigation firms don't cold-message victims on social media.
When Professional Blockchain Investigation May Help
In some cases, stolen or scammed funds can be traced on the blockchain. Cryptocurrency transactions are recorded permanently, and depending on the laundering path, it's sometimes possible to follow funds to a regulated exchange where law enforcement can issue a freeze request. In practice, fund tracing and flagging is only the first step in crypto recovery, followed by other measures.
Timing matters. The faster an investigation starts, the less time scammers have to move funds through mixing services, cross-chain bridges, or non-KYC exchanges. Multi-chain laundering schemes are increasingly common – stablecoins now comprise 84% of illicit transaction volume, up from 63% in 2024, and criminals routinely chain-hop to obscure fund flows.
Not all cases are recoverable, and any professional blockchain investigation service will tell you that upfront. Complex schemes involving mixers, privacy coins, or immediate conversion through non-KYC exchanges significantly reduce recovery prospects.
When Crypto Recovery May Not Be Possible
It's worth being honest about the limits. Some situations make fund recovery extremely unlikely:
- If funds have been routed through crypto mixers or privacy-focused protocols, the on-chain trail may be broken beyond what current analysis tools can reconstruct.
- If funds were immediately converted through a non-KYC exchange, there's no identity information for law enforcement to subpoena.
- If significant time has passed, funds have typically been moved through multiple layers of wallets, swapped across chains, and converted to fiat. Each step reduces the probability of successful tracing and recovery.
Most crypto scams in 2026 are not technically sophisticated. They are psychologically sophisticated. They exploit urgency, trust, authority, and fear of missing out – the same emotional triggers that have powered confidence games for centuries, now amplified by AI-generated voices, faces, and personalities.
The patterns repeat. Guaranteed returns, pressure to act fast, requests for private keys, platforms that take deposits easily but make withdrawals impossible. Recognizing these patterns is the single most effective defense available to any crypto user.
Prevention is always cheaper than recovery.
-AMLBot Team
FAQ
How can I Tell if a Crypto Project is a Scam?
Warning signs include guaranteed returns, anonymous team members, pressure to invest quickly, and requests for private keys or seed phrases. Legitimate crypto projects do not promise risk-free profits or demand sensitive wallet credentials.
What are the Most Common Crypto Scams in 2026?
The most common scams include fake investment platforms, phishing attacks, wallet drainer links, impersonation schemes, romance scams involving crypto payments, and rug pulls. Most follow similar psychological pressure patterns rather than technical complexity.
Are Guaranteed Crypto Returns Always a Red Flag?
Yes. No legitimate crypto investment can guarantee profits. Cryptocurrency markets are volatile, and any platform promising fixed or risk-free returns should be treated with extreme caution.
How do Scammers Create Fake Legitimacy?
Fraudsters often use cloned websites, fake social media profiles, paid testimonials, fabricated licenses, and manipulated reviews to appear credible. Some even use AI-generated videos or impersonate well-known brands.
Why do Crypto Scammers Create Urgency?
Urgency is a psychological tactic. Scammers pressure victims to act quickly so they do not have time to verify information independently. Phrases like “limited offer” or “act now” are common manipulation tools.
Is it Safe to Share my Wallet Address with Someone?
A public wallet address alone is generally safe to share. However, you should never share your private key, seed phrase, or sign unknown transactions, as these provide full control over your funds.
How can I Verify if a Crypto Website is Legitimate?
Check the domain history, verify company registration details, look for independent reviews, confirm social media authenticity, and ensure the platform does not request sensitive credentials. Testing small transactions can also reduce risk.
What is a Wallet Drainer Attack?
A wallet drainer attack occurs when a user signs a malicious smart contract that grants permission to transfer tokens. These attacks often appear as legitimate airdrops or NFT minting pages.
How Can I protect Myself before Sending Cryptocurrency?
Use two-factor authentication, verify recipient addresses carefully, test with small amounts first, avoid emotional decision-making, and independently confirm any investment opportunity.
Why are Experienced Investors Still Vulnerable to Crypto Scams?
Scams often rely on emotional manipulation rather than technical ignorance. Even experienced users can fall victim to urgency, authority impersonation, or sophisticated social engineering tactics.