Wallet and Entity Identification in Blockchain Analytics

INTRO
A blockchain ledger records every transaction, but it never tells you who is behind an address. It shows that 0x7a3f… sent 14.2 ETH to 0xb8c1…, yet reveals nothing about whether those strings belong to an individual, an exchange, or a sanctioned mixer. Multiply this by the billion-plus addresses across major networks, and the problem becomes clear: raw transaction data without interpretation is just noise.
This is where wallet and entity identification comes in — the process of grouping related addresses into clusters and attributing them to known services or risk categories. Without this layer, blockchain analytics can map fund flows but cannot explain who participates or what risk they carry.
Why Wallets Do Not Equal Entities
A common misconception in blockchain analysis is treating a single address as a single user. The relationship between addresses and the services that control them is far more complex.
Consider Binance, which serves over 250 million registered users. Each user receives at least one unique deposit address per blockchain. Add hot wallets, cold storage, and internal transfer addresses, and a single exchange may control hundreds of millions of addresses. On-chain clustering research identified a major U.S. exchange's Bitcoin cluster at roughly 22+ million addresses — the largest single entity on the network.
On the other end, one person might use multiple wallets across different blockchains or generate fresh addresses for each transaction. The address is a technical artifact. The entity is what gives it meaning.
Address vs. Controlled Infrastructure
Think of how a major exchange operates on-chain. When you deposit Bitcoin, you send funds to a unique address generated for you. But that address is not "yours" — it belongs to the exchange's infrastructure. The exchange sweeps deposits into consolidated hot wallets, which feed cold storage. Withdrawals flow from a different set of wallets entirely.
📘 Hot Wallet — an online wallet used for day-to-day operations like withdrawals. Cold Wallet — offline storage securing the majority of funds.
This pattern — address rotation, deposit sweeping, internal consolidation — is standard across custodial services. The visible addresses change constantly, but the controlling entity remains the same.
Why This Matters for Analysis
Without entity context, a blockchain investigator sees only a web of addresses exchanging value:
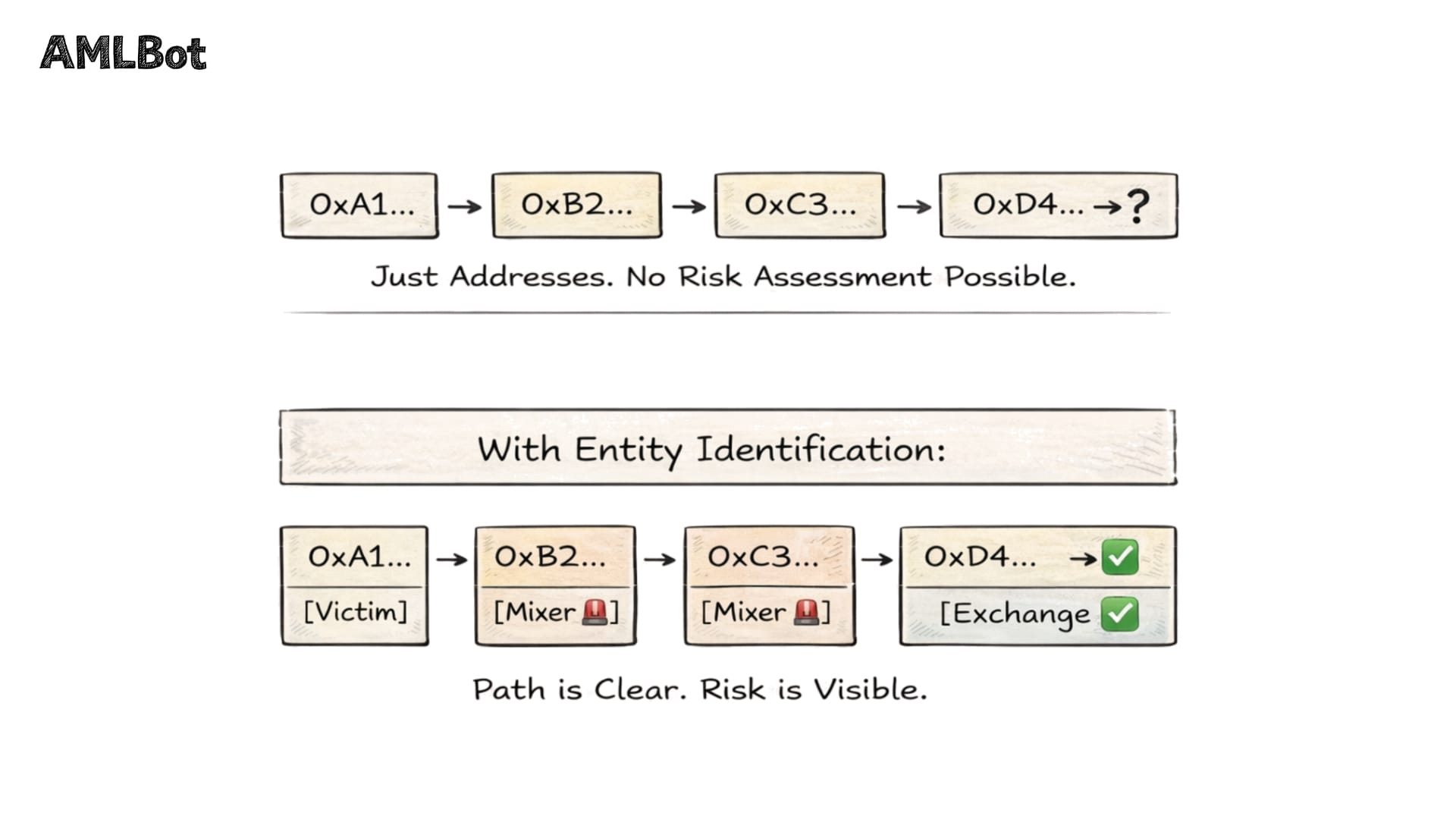
So, wallet and entity identification is the foundation that makes tracing actionable and compliance meaningful.
What Is Wallet Clustering?
Wallet Clustering groups multiple blockchain addresses likely controlled by the same user or service into a single analytical unit, transforming the flat address-level view into an entity map.
The concept is straightforward: if you can determine that address A, address B, and address C are all controlled by the same party, you treat them as one entity. The challenge lies in making that determination reliably across billions of addresses.
Conceptual Clustering Logic
Clustering relies on observable patterns in how addresses interact on-chain. The foundational insight — first noted in the 2008 Bitcoin Whitepaper and formalized by Meiklejohn et al. in 2013 — is that transaction structure reveals control relationships.
In Bitcoin's UTXO Model, when multiple input addresses appear in the same transaction, it typically means a single entity controls all of them, because constructing that transaction required access to every input's private key. This behavioral signal, the common-input-ownership heuristic, remains the backbone of Bitcoin clustering.
Beyond input analysis, clustering uses change address detection, wallet software fingerprinting, and temporal behavior analysis. For Ethereum's account-based model, heuristics differ: analysts look at deposit address reuse, airdrop claim behavior, and token approval sequences.
Importantly, clustering does not reveal real-world identity. It identifies relationships between addresses and groups them into logical units. Attribution — connecting a cluster to a service or risk category — is a separate step.
Clustering in the Context of Transaction Tracing
Clustering and tracing are complementary layers. Transaction Tracing follows fund movement from one address to another. Clustering structures the participants along that path.
Imagine tracing 50 BTC from a ransomware payment. Without clustering, you see funds split across dozens of addresses. With clustering, you recognize that 30 of those addresses belong to the same mixing service — and the final destination is a cluster tagged as a known exchange.
From Wallet Clusters to Entity Identification
Once addresses are grouped into clusters, the next step is entity tagging — assigning a label indicating what type of service the cluster represents. A cluster is a set of related addresses; an entity is a cluster with attribution.
Entity categories include centralized exchanges, custodians, DeFi protocols, mixers, darknet marketplaces, sanctioned services, and known threat actors.
Tagging draws on multiple intelligence sources: direct interaction with services, open-source intelligence, law enforcement data sharing, and pattern matching. Leading providers maintain databases mapping over a billion addresses to tens of thousands of real-world entities.
How Entity Tagging Supports Risk Assessment
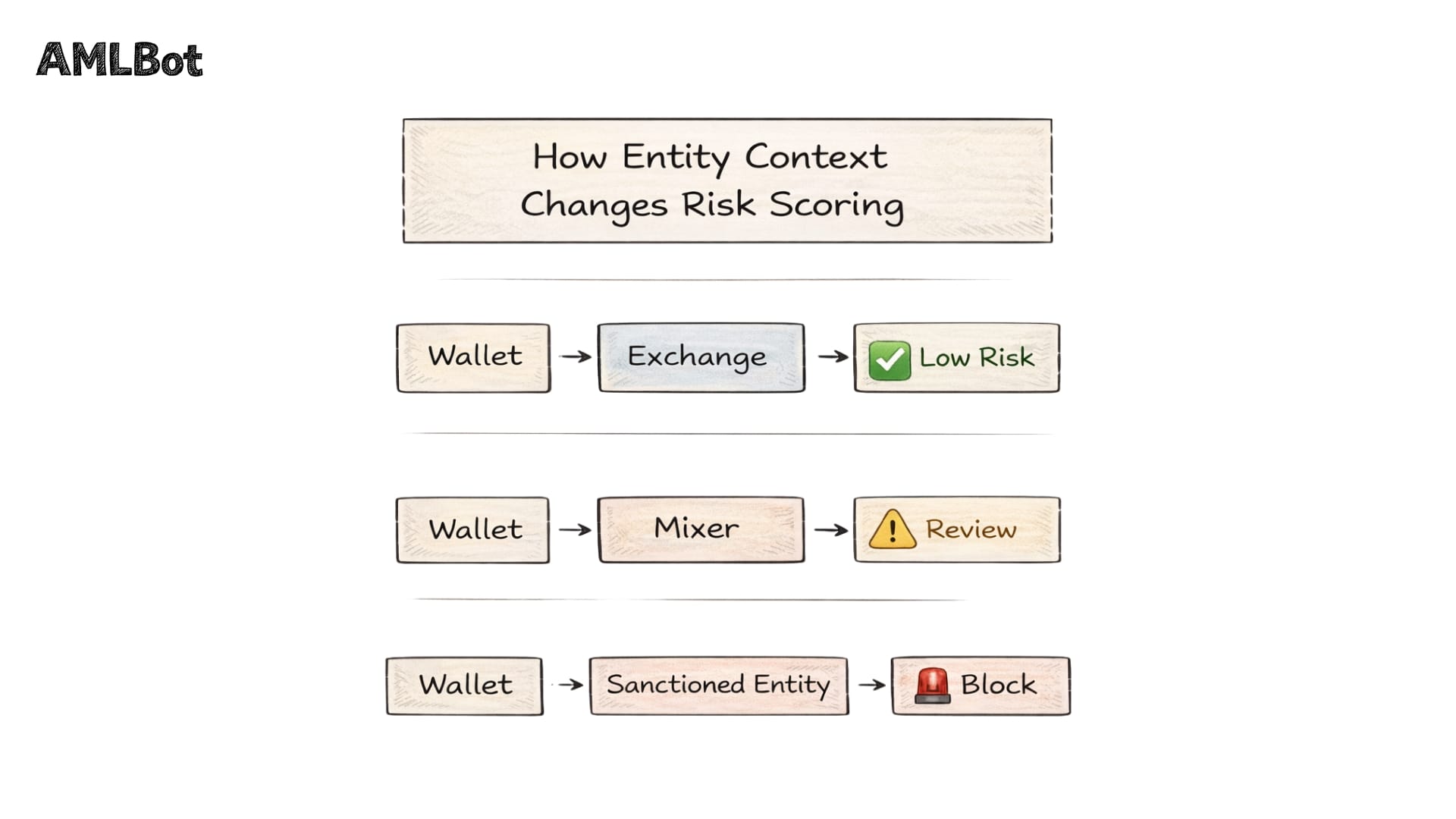
Entity identification transforms raw blockchain data into actionable risk intelligence. Counterparty risk depends on entity context: a transaction with a regulated exchange carries different risk than one with a ransomware-linked mixer.
Sanctions exposure requires knowing whether any entity in a transaction chain appears on OFAC, EU, or UN lists. The U.S. Treasury's sanctioning of Tornado Cash in 2022 — which had processed over $7 billion, including funds laundered by the Lazarus Group — showed how entity attribution drives regulatory action.
Cross-Chain Attribution Challenges
Entity tagging grows more complex when assets move across blockchains. A user might swap ETH for BTC through a cross-chain bridge, creating a new address on a different network. The entity remains the same, but the on-chain trail breaks.
📘 Cross-Chain Bridge — a protocol enabling asset transfers between different blockchains by locking tokens on one chain and issuing equivalent tokens on another.
Over $7 billion in illicit cryptocurrency has been laundered via cross-chain methods. Major analytics providers have invested heavily — attributing hundreds of millions of cross-chain swaps and tracking dozens of bridges — but cross-chain analysis remains one of the hardest problems in blockchain forensics.
Entity Identification in Scam Investigations
In fraud investigations, entity identification often makes the difference between a dead-end address list and an actionable case. Scam operations rarely use a single wallet — they build infrastructure: collection addresses, consolidation wallets, layering addresses, and off-ramp wallets interacting with exchanges.
For a focused explanation of how these layered wallet structures support obfuscation in practice — through chain hopping, mixers, DeFi routing, and fragmentation — see Layering in Crypto AML: How It Works and How to Detect It.
The Ronin Bridge hack of March 2022 illustrates this. After $620 million was stolen, blockchain intelligence firms traced funds through dozens of intermediary addresses. Entity tagging revealed that laundering patterns matched behavioral signatures previously attributed to the Lazarus Group — leading to OFAC sanctioning the attacker's wallet and the first-ever seizure of DPRK-stolen cryptocurrency.
Identifying Infrastructure Behind Fraud
If multiple fraud campaigns share deposit addresses at the same exchange cluster or use the same mixer for laundering, the investigation shifts from tracking incidents to mapping an operation. This is where wallet and entity identification intersects with Crypto Scam Fund Tracing.
For investigators tracing stolen assets, AMLBot Tracer provides entity attribution across multiple blockchains — mapping fund flows from theft to off-ramp destination.
Entity Identification and AML Monitoring
For compliance teams at exchanges and financial institutions, entity identification is not a one-time exercise — it is continuous monitoring embedded into every transaction workflow.
Every incoming and outgoing transaction is screened against an entity database. If a deposit originates from a cluster tagged as a high-risk mixer, an alert triggers. If a withdrawal destination is linked to a sanctioned entity, the transaction is blocked.
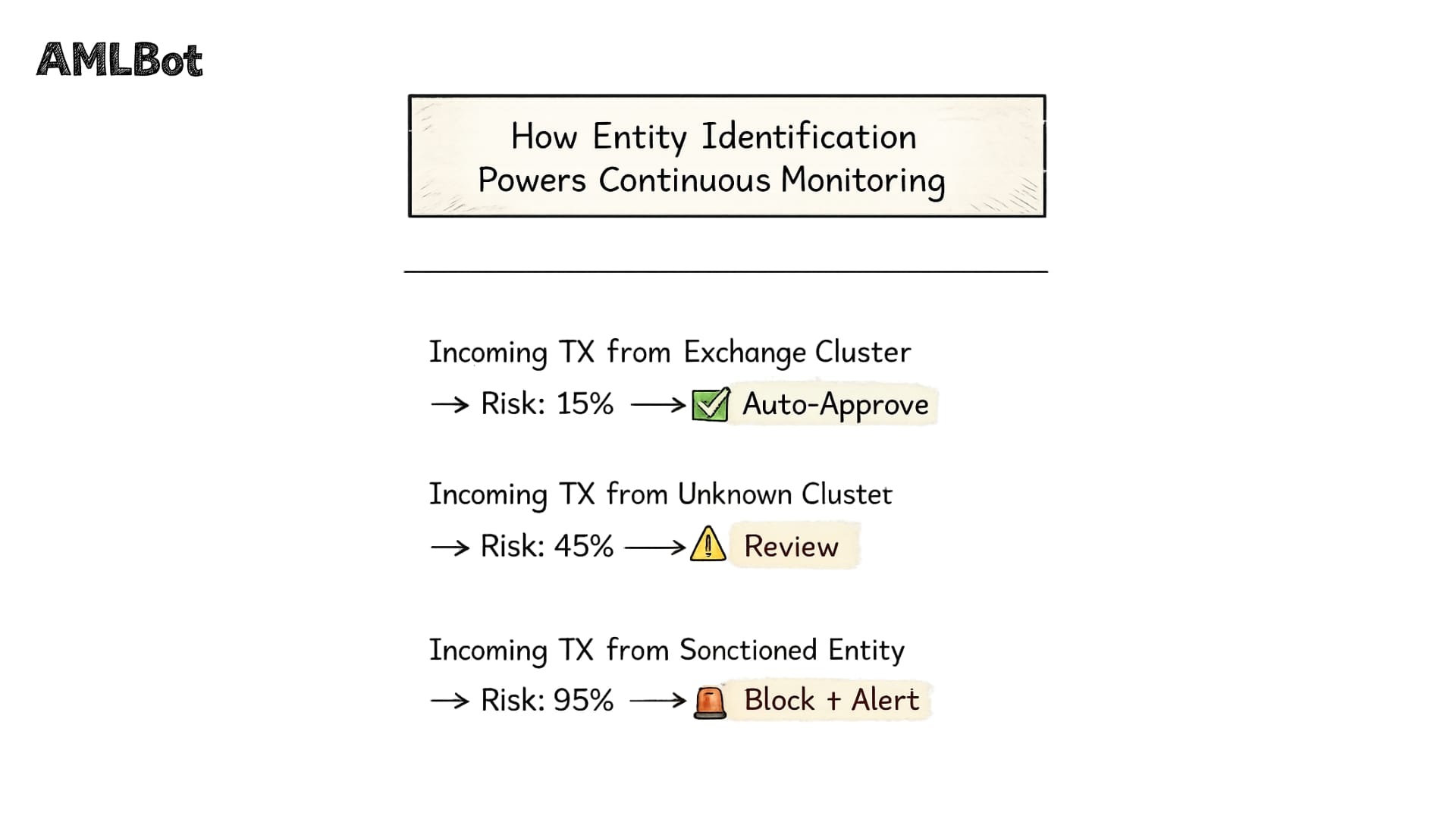
The FATF's Guidance on Virtual Assets and VASPs (2021) requires service providers to identify counterparties and apply enhanced due diligence for high-risk entities. The FATF itself acknowledges that no proven method exists to identify counterparty VASPs from wallet addresses alone — which is why entity databases play a critical role.
Limitations of Entity Identification
No attribution system is perfect. The "Ghost Clusters" Study (USENIX Security 2025) tested a major provider's data against ground-truth records from seized illicit services. Accuracy ranged from 25% for a mixer to 95% for a darknet marketplace. False positive rates were below 0.5% — analytics rarely misattribute an address, but frequently miss addresses that belong to an entity.
False positives, while rare, carry real consequences. A legitimate user incorrectly clustered with a high-risk entity may find their accounts frozen.
Rapid wallet rotation poses an ongoing challenge. Sophisticated actors generate new addresses for every transaction. Privacy-enhancing technologies — CoinJoin (where multiple users combine transactions), Taproot, and zero-knowledge proofs — add further complexity.
Cross-chain fragmentation compounds these difficulties. When entities operate across dozens of blockchains, maintaining attribution requires correlating activity across different networks — a problem that remains partially unsolved.
The Role of Entity Identification in Modern Blockchain Analysis
Every layer of blockchain analysis depends on entity identification. Transaction tracing without attribution produces a graph of addresses. With entity identification, that graph becomes a map of participants — each carrying risk context that shapes how the investigation proceeds. Investigations without entity context chase addresses. With it, analysts build cases: linking scam infrastructure to known threat actors, identifying off-ramp points, and providing evidence for asset freezing.
AML Monitoring without counterparty identification is compliance theater. Entity attribution transforms it into a risk management function that distinguishes between benign and suspicious activity in real time. Wallet and entity identification is what turns blockchain data from an opaque ledger into an intelligence layer. It is not the final step in an investigation — but it is the step that makes every other step possible.
Ready to see Entity Identification in Action?
AMLBot Tracer helps investigators map fund flows and identify entities across blockchains. KYT solution gives compliance teams continuous counterparty monitoring with real-time risk scoring. Explore how entity attribution can strengthen your workflow.
-AMLBot Team

FAQ
What is Wallet and Entity Identification in Blockchain Analytics?
Wallet and Entity Identification is the process of grouping related blockchain addresses into clusters and attributing them to known services or risk categories — exchanges, custodians, mixers, or sanctioned entities. It is the analytical layer that connects raw on-chain data to meaningful risk intelligence for compliance, investigations, and counterparty assessment.
What is Wallet Clustering?
Wallet Clustering is an analytical method that groups multiple blockchain addresses into a single unit based on evidence of shared control — such as shared transaction inputs, change address patterns, or wallet software fingerprints. Clustering does not identify individuals; it identifies control relationships between addresses.
Does wallet Clustering Reveal the Identity of a Person?
Wallet Clustering is an analytical method that groups multiple blockchain addresses into a single unit based on evidence of shared control — such as shared transaction inputs, change address patterns, or wallet software fingerprints. Clustering does not identify individuals. It identifies control relationships between addresses.
How are Exchanges Identified on the Blockchain?
Exchanges are identified through observable infrastructure patterns: unique deposit addresses generated for each user, periodic sweep transactions consolidating deposits into hot wallets, distinct withdrawal flows, and publicly known service addresses tagged by blockchain intelligence providers.
What is Entity Tagging?
Entity tagging is the process of assigning a contextual label to a cluster of blockchain addresses — such as "Exchange," "DeFi Protocol," "Mixer," or "Sanctioned Entity" — to indicate the type of service it represents. It transforms anonymous address clusters into attributed entities with defined risk profiles.
Why is Entity Identification Important for Transaction Tracing?
Without Entity Identification, transaction tracing only shows fund movement between anonymous addresses. Entity attribution adds context by identifying the counterparty type at each step transforming raw tracing into an interpretable investigation map.
How does Entity Identification Support AML Monitoring?
Entity identification enables compliance systems to screen transactions against known entity databases, detect high-risk or sanctioned counterparties, calculate risk scores, and generate alerts when thresholds are exceeded. Without entity attribution, monitoring cannot assess counterparty risk.
Can Entity Identification Produce False Positives?
Yes. Independent research (USENIX Security 2025) found false positive rates are generally below 0.5%, but misclassification can occur due to incomplete data or evolving infrastructure. A false positive can result in legitimate users being flagged or restricted.
How does Cross-Chain Activity affect Entity Identification?
Cross-chain movement complicates entity identification: address formats change, transaction models differ (UTXO vs. account-based), and the on-chain trail fragments at bridge points. Maintaining attribution across chains requires specialized correlation and remains one of the most challenging areas in blockchain forensics.
Is Entity Identification the Same as Blockchain Forensics?
No. Entity identification provides contextual labeling of addresses and is one component of blockchain forensics. Forensics is a broader discipline combining entity identification with transaction tracing, evidence collection, timeline reconstruction, and case documentation for investigations and legal proceedings.