Cryptocurrency Investigations Explained: From Detection to Resolution

As crypto markets expand and transaction volumes grow, the complexity of identifying suspicious activity within blockchain ecosystems increases. What was once a niche technical exercise has matured into a structured discipline: cryptocurrency investigations now involve coordinated workflows that span analytics, legal documentation, and cross-institutional coordination.
It is important to distinguish between three related but distinct activities. Continuous transaction monitoring flags potentially suspicious behavior in real time. Crypto Forensics and Asset Tracing provide the evidentiary methodology needed to support formal proceedings.
A full cryptocurrency investigation, however, is something broader. It is a structured response workflow that integrates analytics output, attribution analysis, forensic documentation, and multi-party coordination from a triggering event through to a defined resolution.
This article explains the cryptocurrency investigation process as a workflow – what triggers it, what each stage involves, who participates, and where the process encounters real-world constraints.
What Is a Cryptocurrency Investigation
A cryptocurrency investigation is a structured process through which analysts, compliance professionals, and relevant stakeholders examine blockchain activity to determine the nature of suspicious or anomalous transactions, identify the entities involved, document findings in an actionable format, and coordinate an appropriate response. This is a significantly broader function than blockchain analytics explained – analytics is a tool set; an investigation is a process that uses those tools within a defined operational framework.
A complete investigation workflow includes escalation decisions, institutional coordination, evidence preparation, and in some cases, regulatory notification or law enforcement referral. None of these elements exists in isolation. Each stage informs the next, and the quality of early-stage work determines the value of the final output. This also means that a cryptocurrency investigation is inherently multi-participant. Depending on the scope and severity of the case, it may involve compliance teams, forensic analysts, exchanges, legal counsel, and regulatory or law enforcement bodies. Еach engaging at different stages and with different responsibilities.
Investigation vs. Monitoring
Transaction Monitoring is a continuous, systemic function. It operates across a defined population of accounts and transactions, flagging patterns that exceed established thresholds or match known risk indicators. It is proactive and largely automated. An investigation, by contrast, is a structured response to a specific event or escalated alert. It has a defined scope, discrete stages, and a target outcome, whether that is compliance closure, regulatory reporting, or referral to external authorities. In practice, monitoring and investigation are sequential: a monitoring system generates the alert; an investigation determines what the alert means and what should be done about it.
It is worth noting that not every monitoring alert escalates into a full investigation. Many flagged transactions are resolved through enhanced due diligence or a brief internal review. An investigation is initiated when the alert cannot be resolved at the monitoring level, when the activity is sufficiently complex, high-risk, or consequential to warrant a structured, documented response with defined accountability.
Investigation vs. Forensic Analysis
Forensic Analysis is a discipline within the investigation process, not the process itself. It specifically refers to the methodology used to structure, preserve, and present evidence, applying standards that withstand scrutiny in compliance reviews or formal proceedings. A full cryptocurrency investigation incorporates forensic analysis at the documentation stage, but it also includes alert validation, transaction reconstruction, attribution, coordination, and escalation, all of which extend well beyond the evidentiary focus of forensics alone.
A useful way to frame the distinction: forensic analysis answers the question of how findings are documented and preserved; the investigation as a whole answers the question of what happened, who was involved, and what should happen next. Forensics is essential to the process, particularly when findings may be used in regulatory submissions or legal proceedings, but it is one stage within a broader operational workflow, not a synonym for the investigation itself.
What Triggers a Cryptocurrency Investigation
Investigations do not begin spontaneously. They are initiated in response to a defined triggering condition, an event or alert that crosses an institutional or regulatory threshold and warrants structured examination. The nature of the trigger shapes the scope and urgency of the investigation that follows. It also determines who is responsible for initiating it: a compliance officer responding to an internal AML flag operates in a different capacity than a legal team responding to a reported theft, even if both ultimately engage the same investigative workflow.
Compliance-Driven Triggers
Many investigations originate within an organization's compliance function. A transaction monitoring system may generate a suspicious activity alert based on volume anomalies, unusual counterparty patterns, or behavioral deviations from an established baseline. Sanctions exposure is a particularly significant compliance trigger: if a transaction involves a wallet address or entity subject to sanctions administered by OFAC, the EU, or equivalent authorities, this typically requires immediate escalation and formal documentation under applicable regulatory frameworks.
The Financial Crimes Enforcement Network (FinCEN) has noted in guidance documents that virtual asset service providers (VASPs) are expected to maintain effective AML programs capable of identifying and reporting suspicious activity. In its 2019 guidance on convertible virtual currencies, FinCEN confirmed that 'the obligation to identify and report suspicious transactions applies regardless of the medium of exchange.' This means that a compliance-driven flag in a crypto environment carries the same investigative weight as one arising in traditional financial services.
AML flags may also arise from the application of the FATF Travel Rule, which requires VASPs to collect and transmit originator and beneficiary information for virtual asset transfers above applicable thresholds. Where that information is missing, incomplete, or inconsistent with other transaction data, the discrepancy itself constitutes a compliance trigger that may warrant further examination.
Incident-Driven Triggers
Investigations may also be initiated in response to a reported incident, a theft, a fraud claim, or an internal irregularity identified through audit or operational review. In these cases, the trigger is an observed harm or anomaly rather than a systemic flag. Internal irregularities deserve particular attention here: discrepancies between transaction records and internal accounts, unauthorized wallet activity, or patterns of unusual access to custody infrastructure can all initiate an investigation without any external complaint or regulatory prompt. These cases are often more complex to scope precisely because the boundaries of the incident are not immediately clear. The investigation must establish what occurred, reconstruct the relevant transaction activity, and determine whether further escalation to law enforcement, regulators, or external parties is warranted.
In theft-related cases, documenting the incident and preserving transaction details is a critical early step before a formal investigation begins.
📂 See guidance on initial steps after losing crypto assets for a structured overview of that initial phase.
Stage 1 – Detection and Initial Review
The first stage of the investigation workflow is alert validation and preliminary scoping. Before any substantive analytical work begins, the flagged activity must be confirmed as genuine, not a false positive generated by systemic noise. Analysts using a tool such as AMLBot Tracer Blockchain Analytics Tool, can begin this process by cross-referencing the flagged transaction against known risk indicators, counterparty data, and relevant contextual information.
Scope definition is a critical output of this stage that is often underweighted. Before the investigation advances, analysts must establish which transactions, addresses, time periods, and entities fall within its boundaries. An investigation without a defined scope risks either missing relevant activity or consuming disproportionate resources on tangential data. The scope established here is not fixed. It may be revised as new information emerges, but it provides the operational framework for subsequent stages.
Alert Validation
Alert validation involves reviewing the flagged transaction or account to determine whether the anomaly is substantive. This includes confirming the transaction data against on-chain records, assessing whether the activity matches the alert typology that triggered it, and determining whether the counterparties involved are known, unknown, or associated with existing risk categories. Many alerts will be resolved at this stage, either dismissed as low-risk or escalated for further examination. The validation step also serves a documentation function: recording the basis for dismissing an alert is as important as recording the basis for escalating it. Regulators reviewing an organization's AML program will assess not only how suspicious activity was identified, but how and why alerts were closed without further action.
Preliminary Risk Assessment
For alerts that survive initial validation, a preliminary risk assessment establishes the activity's baseline risk profile. This includes evaluating counterparty exposure, whether the relevant wallets or entities have prior associations with sanctioned addresses, dark web services, or known illicit actors, and assigning an initial risk score. The output of this stage defines the scope and resource allocation for the investigation stages that follow. A high-risk preliminary finding will typically trigger a more comprehensive workflow than a borderline case.
At this stage, the risk assessment is necessarily preliminary. It is based on available data rather than a complete analytical picture. Its purpose is not to reach conclusions but to calibrate the investigation: determining whether the case warrants a full multi-stage workflow, a targeted review, or enhanced monitoring without immediate escalation. That calibration decision, documented at the end of Stage 1, becomes the formal basis for allocating resources going forward.
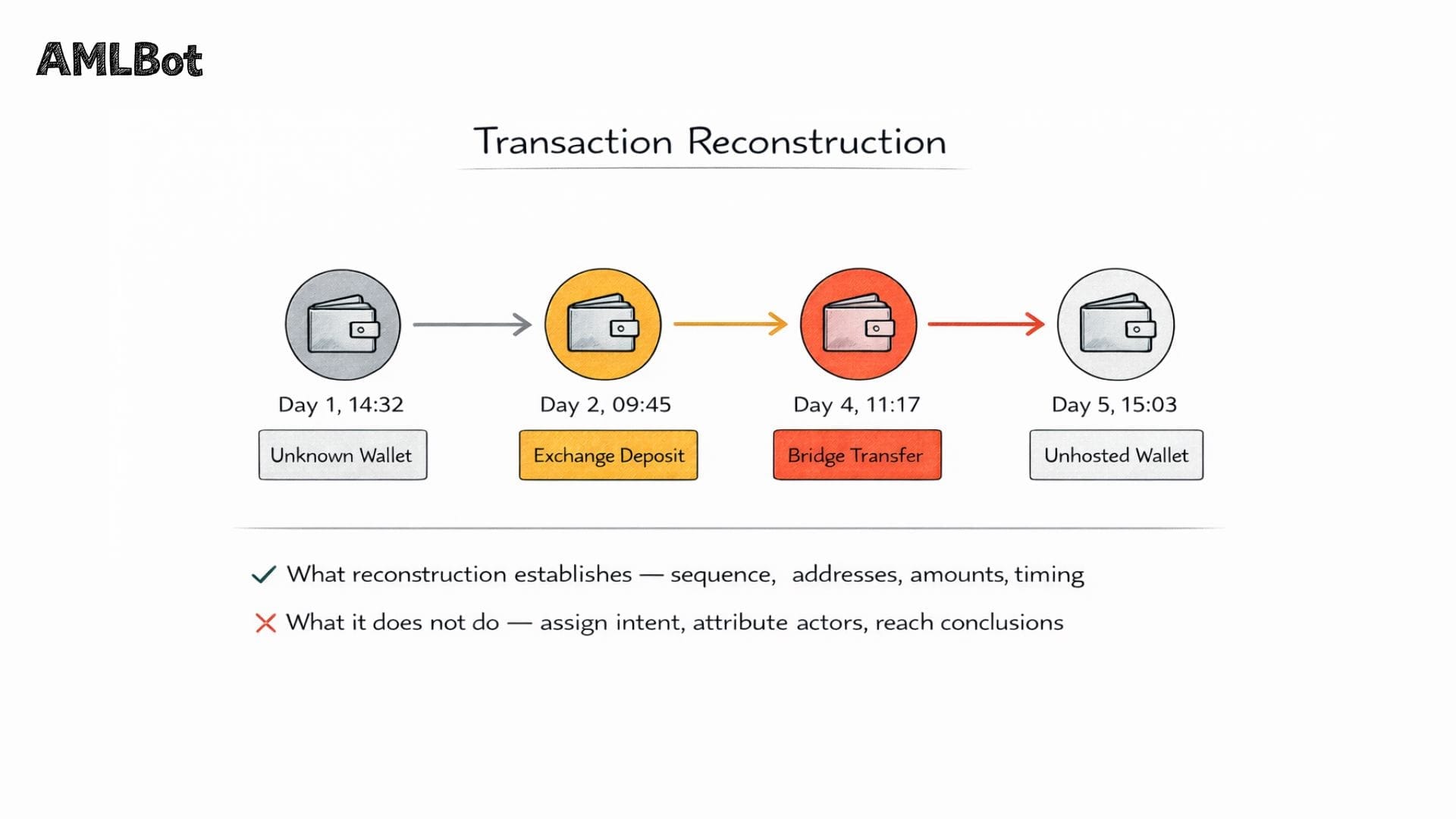
Stage 2 – Transaction Reconstruction
Transaction reconstruction establishes the factual basis of the investigation. This stage builds a chronological account of asset movement, not a granular technical mapping of every hop, but a structured representation of key events, major transfer points, and the overall flow of funds.
📂 Detailed methodology for this process is covered in the article on Transaction Tracing in Crypto. At the investigation level, reconstruction serves to establish context rather than provide technical depth.
It is equally important to note what reconstruction does not do at this stage: it does not assign intent, attribute wallets to specific actors, or reach conclusions about the nature of the activity. Those functions belong to the attribution stage. Reconstruction is concerned with establishing an accurate, verifiable factual record of what moved, when, and through which addresses, on which the rest of the investigation depends.
Establishing a Timeline
Sequencing transactions in chronological order allows analysts to identify when funds moved, how quickly, and whether the pattern reflects deliberate structuring or a normal operational pattern. A timeline anchors the investigation in verifiable on-chain data and provides the structural backbone for subsequent attribution and documentation work. Key movement points, large transfers, conversions, and interactions with high-risk entities are flagged within the timeline for closer examination. The pace and pattern of movement can itself be analytically significant: funds that move rapidly through multiple addresses within a short window present a different risk profile than assets that remain stationary over an extended period. These timing patterns do not constitute conclusions, but they inform the prioritization of subsequent attribution work and may be referenced in the forensic documentation that follows.
Identifying Relevant Counterparties
Not all counterparties in a transaction chain carry the same investigative significance. The reconstruction stage identifies which wallets, exchanges, and service addresses are materially relevant to the case, those that received, forwarded, or interacted with the funds in question. Exchanges are particularly important counterparties because they hold KYC data that may be accessible through formal coordination. Service wallets associated with high-risk platforms and addresses linked to known illicit activity are also prioritized for further analysis in the attribution stage.
Relevance is determined by proximity and materiality, not merely by contact. An address that received a small incidental transfer may be noted but deprioritized; an address that received the bulk of the funds, interacted with them repeatedly, or served as a conversion point warrants closer examination. This triage function, distinguishing material counterparties from incidental ones, is essential to keeping the investigation focused and proportionate to its defined scope.
Stage 3 – Attribution and Contextual Analysis
Attribution is the process of associating blockchain addresses with real-world entities or risk categories. It is one of the most consequential stages of the investigation workflow because it determines who is implicated, to what degree, and through what mechanisms. A detailed treatment of the underlying methodology is available in the article on wallet and entity identification; here, the focus is on attribution's role within the broader investigation process.
Attribution also performs a counterparty classification function: each address identified in the reconstruction stage is assigned a category, regulated service, unhosted wallet, high-risk entity, sanctioned address, or unknown, which determines how it is treated in the documentation and escalation stages. This classification is not binary; it operates on a risk spectrum, and the investigative significance of a given counterparty is determined by both its category and its proximity to the core activity under examination.
Entity Identification
Entity identification draws on wallet clustering techniques, grouping addresses likely controlled by the same party based on behavioral and structural on-chain signals, as well as direct attribution data linking specific addresses to identified services, exchanges, or entities. The goal at this stage is not to determine the identity of individuals, but to establish the institutional or risk context of the relevant addresses: is this wallet associated with a regulated exchange, a sanctioned entity, a known mixer, or an unidentified private actor? Service attribution, linking addresses to known platforms through on-chain behavioral data and reference databases, is particularly valuable where direct KYC access is not available, as it allows the investigation to establish institutional context without requiring exchange cooperation at this stage.
Risk Context Interpretation
Attribution findings are interpreted against a risk framework. Sanctions exposure is assessed by checking relevant addresses against OFAC's Specially Designated Nationals (SDN) list and equivalent databases maintained by EU, UK, and UN authorities. High-risk interaction is evaluated based on the nature and proximity of connections to flagged entities. The output of this stage feeds directly into the forensic documentation and escalation decisions that follow. An investigation that surfaces sanctions exposure, for example, will typically require more urgent and formal handling than one involving only elevated-risk counterparties.
Risk context interpretation also determines the urgency and format of what follows. A finding of direct sanctions exposure typically triggers an immediate compliance response, including SAR filing obligations and potential account action, that operates on a different timeline than a finding of indirect high-risk interaction. Documenting the basis for these risk determinations with specificity, including the databases consulted and the date of the check, is essential: sanctions lists are updated frequently, and the evidentiary value of a sanctions finding depends on its being tied to a verified, timestamped source.
Stage 4 – Forensic Documentation
Forensic documentation transforms the outputs of the preceding stages, the reconstructed timeline, the attribution findings, and the risk assessments into a structured evidentiary record. As discussed in the article on crypto forensics methodology, the standard for this documentation is determined by its intended use: an internal compliance review, a regulatory submission, or a formal legal proceeding.
The documentation stage is also where the investigation becomes transferable. Prior stages produce analytical outputs understood primarily by those who conducted them; forensic documentation translates those outputs into a format that can be reviewed, challenged, and acted upon by compliance officers, legal counsel, regulators, or law enforcement, none of whom were necessarily present during the analytical work. The discipline required at this stage is therefore not only technical but also communicative: findings must be presented with sufficient specificity to be verifiable and sufficient clarity to be actionable.
Structuring Findings
The investigation findings are organized into a coherent narrative structured around the timeline established in Stage 2. This chronological narrative references specific transactions, identified by hash, address, timestamp, and amount, and integrates the attribution findings that give those transactions their risk context. The structured format allows reviewers with varying levels of technical expertise to follow the chain of events and understand the basis for the investigation's conclusions. Referencing verified on-chain data throughout the document is essential to its evidentiary value. Evidence preparation at this stage also involves preserving the source data in a form that supports independent verification. Transaction hashes, block heights, and address references should be recorded in a way that allows a reviewer to confirm each finding against the public blockchain record without relying solely on the investigator's representation.
Preparing Reports
The final documentation package typically includes a compliance summary for internal use, a more detailed technical appendix for forensic or legal review, and an escalation memorandum if the findings warrant notification to regulators or law enforcement. Each component is calibrated to its audience. Compliance documentation focuses on risk classification, SAR/STR filing obligations, and institutional exposure. An escalation package for law enforcement includes transaction references, attribution evidence, and a clear factual summary of the alleged activity, without legal conclusions, which remain outside the investigator's proper scope.
The distinction between a compliance summary and an escalation package is not merely stylistic. It reflects different legal and operational contexts. A SAR or STR submission, for example, is governed by specific statutory requirements in the relevant jurisdiction, including prescribed formats, mandatory fields, and filing deadlines. An escalation package prepared for law enforcement referral operates under different standards and serves a different purpose. Preparing both from the same underlying investigative record, without conflating their respective requirements, is a core discipline of the documentation stage.
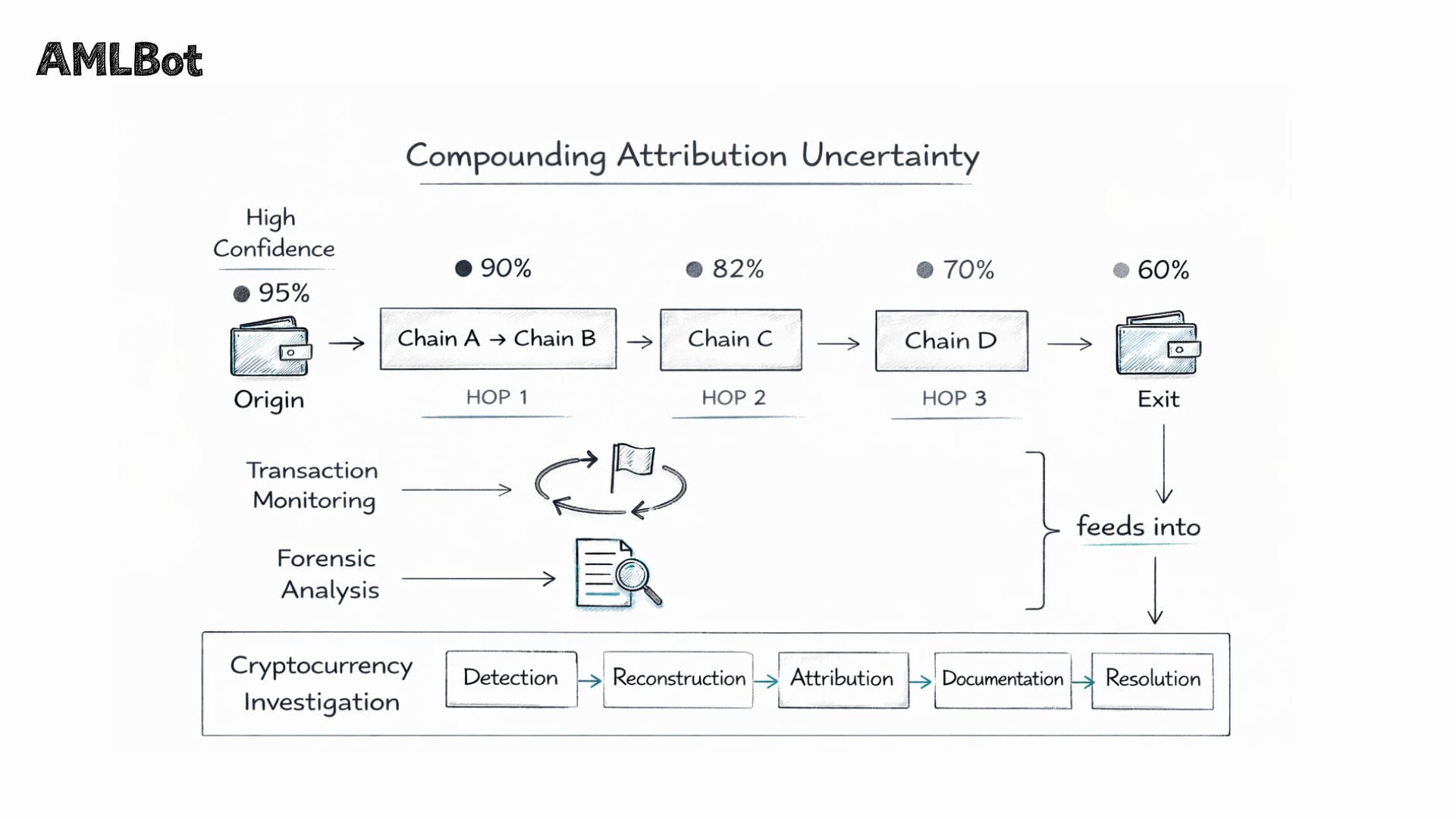
Stage 5 – Cross-Chain and Infrastructure Complexity
Modern blockchain activity rarely stays within a single network. The fifth stage of the investigation workflow addresses the added complexity introduced when assets move across multiple chains, via bridges, or through service infrastructure that spans jurisdictions. A detailed technical treatment of this challenge is available in the article on cross-chain analysis; here, the focus is on its investigative implications.
Multi-Network Movement
When assets cross from one blockchain to another, whether through decentralized bridges, wrapped asset mechanisms, or centralized exchange transfers, the transaction history is fragmented. Each network maintains its own ledger, and correlating activity across those ledgers requires additional analytical work to establish continuity. Cross-chain transfers may also involve asset switching, converting one token for another in the process, which adds a further layer of reconstruction complexity to the investigation.
From an investigative standpoint, each chain boundary represents a potential discontinuity in the evidentiary record. Where a bridge transaction can be correlated across both networks, by matching amounts, timing, and address patterns, continuity can be maintained. Where that correlation is uncertain or incomplete, the investigation must document the gap explicitly rather than assume continuity. Asset switching compounds this further: when funds enter a bridge as one token and exit as another, the value trail may be preserved while the asset identity changes, requiring additional contextual analysis to confirm that the funds in question are the same funds.
Infrastructure Coordination
Exchanges and other service providers often serve as infrastructure nodes in cross-chain activity, receiving funds on one network and facilitating their onward movement on another. Coordinating with these entities requires identifying the relevant service, determining applicable jurisdiction, and submitting a formal request for information or cooperation. The response timeline for these requests varies significantly and can affect whether the investigation achieves its objectives within a practically useful timeframe. Service response is shaped by several factors: the exchange's jurisdictional obligations, whether a formal legal process is required to compel disclosure, the quality and specificity of the information request, and the service provider's internal prioritization policies. Requests that are vague, incomplete, or submitted without adequate supporting documentation are frequently deprioritized or declined. Effective infrastructure coordination, therefore, requires not only identifying the right counterparty but also presenting a sufficiently substantiated request to warrant a timely response.
Coordination and Escalation
An investigation that produces only an internal report has a limited operational impact. The coordination and escalation stage translates the findings into external action, communicating through exchanges, submitting compliance reports, notifying regulatory authorities, or involving law enforcement.
📂 An illustrative example of how coordination can produce outcomes is explored in the Address Poisoning Case Study.
Exchange coordination typically involves submitting a formal information request, identifying the relevant transaction hashes and deposit addresses, and requesting KYC data or account freezing, where jurisdictionally permissible. The legal basis for such requests depends on the receiving exchange's jurisdiction and its applicable regulatory framework. Exchanges operating under AML-regulated regimes in the EU, UK, or US may have formal obligations to respond to such requests from authorized parties.
Compliance reporting runs in parallel to exchange coordination rather than sequentially. Where SAR or STR obligations are triggered by the investigation findings, those submissions must be prepared and filed within the timeframes prescribed by applicable law. In the US, FinCEN regulations generally require SAR filing within 30 days of detecting a reportable transaction, with a 60-day extension available in certain circumstances. The investigation documentation produced in Stage 4 forms the factual basis of these submissions, which is one reason why the quality of forensic documentation directly affects the organization's ability to meet its regulatory obligations in a timely and substantiated way.
Regulatory notification may be required under applicable law. In jurisdictions that mandate Suspicious Activity Reports (SARs) or Suspicious Transaction Reports (STRs), the investigation findings inform the content and timing of those submissions. Law enforcement involvement is typically reserved for cases involving significant criminal activity, where documented findings can serve as the basis for a formal referral. The threshold for referral varies by jurisdiction and the nature of the identified activity. Some regulatory frameworks impose affirmative obligations to report certain categories of crime, while others leave the decision to refer to the organization's discretion. In either case, the referral package should be factual, specific, and limited to what the investigation has substantiated: overstating findings or including speculative conclusions can undermine the credibility of the submission and complicate any subsequent formal process. Law enforcement agencies with dedicated financial crime or cybercrime units, such as the FBI's Internet Crime Complaint Center (IC3) in the US or equivalent bodies in other jurisdictions, are the appropriate recipients for crypto-related criminal referrals.
How Cryptocurrency Investigations Differ from Scam-Specific Cases
Scam-specific investigations, covered in detail in the article on Crypto Scam Fund Tracing, represent one subset of the broader investigation discipline. They share the same fundamental workflow but differ in the specific nature of the triggering event and the victim-oriented context in which they operate. In scam-specific cases, the investigation is typically initiated by or on behalf of an identifiable victim, the harm is concrete and quantified, and the primary objective is to trace and document the movement of specific funds. These features shape the scope, urgency, and framing of the investigation in ways that do not apply to compliance-driven cases, where the triggering condition may be a statistical anomaly rather than a reported harm, and where the output is directed at regulators rather than recovery.
A full cryptocurrency investigation framework is equally applicable to institutional compliance scenarios, sanctions screening reviews, SAR preparation, internal audit responses, and individual fraud or theft cases. In compliance contexts, the investigation may not involve a victim at all; its purpose is to assess organizational risk exposure and ensure compliance with reporting obligations. In regulatory contexts, the investigation may be conducted proactively as part of a periodic review, rather than in response to a specific incident. Understanding this breadth is important because it shapes how resources are allocated and how the output is framed.
The distinction also has implications for how participants are involved. Scam-specific investigations frequently engage private investigators or victim-side legal counsel alongside compliance professionals. Compliance-driven investigations, by contrast, are typically conducted entirely within institutional frameworks, by internal compliance teams, external forensic consultants, or regulated service providers operating under defined legal mandates. Recognizing which type of investigation is underway at the outset is essential to structuring the workflow correctly and setting appropriate expectations for all parties involved.
Resolution Scenarios
Every investigation moves toward a defined resolution, a point at which the workflow reaches a conclusion appropriate to the findings and the context. Resolution is shaped by three variables: what the investigation found, the mechanisms available given the jurisdiction and the parties involved, and the obligations that apply to the organization conducting or commissioning the investigation. These variables mean that two investigations involving similar fact patterns may resolve very differently depending on the institutional context.
Resolution is not always a final outcome; it may be a threshold event that initiates a further process:
- Compliance Closure: The investigation findings are documented, risk classification is updated, and SAR/STR obligations are assessed. If no escalation is warranted, the case is closed with a formal compliance record. Closure does not mean the findings are discarded. They are retained as part of the organization's AML record and may inform future monitoring rules or risk assessments for the same counterparties.
- Asset Freezing: Where exchange coordination or legal mechanisms are available and timely, account holds, or asset freezes may be sought on the basis of documented investigation findings. The viability of this outcome depends heavily on speed and jurisdiction: assets that have already moved beyond a cooperative exchange's control or into a jurisdiction without applicable legal mechanisms may not be reachable through freezing requests, regardless of the quality of the investigation.
- Legal Escalation: Findings that meet applicable thresholds may be referred to law enforcement or regulatory authorities, with the forensic documentation package serving as the formal submission. Legal escalation initiates a process that operates outside the investigating organization's control. The pace, scope, and outcome of any subsequent formal proceeding are determined by the receiving authority, not by the party making the referral.
- Internal Risk Mitigation: Regardless of external escalations, investigation findings inform internal risk controls, update counterparty risk profiles, refine transaction monitoring rules, and address any identified compliance gaps. This resolution pathway applies in every case, including those where external escalation is not warranted: the investigation always produces intelligence that should be fed back into the organization's risk framework to reduce the likelihood of similar activity going undetected in the future.
📂 In some cases, structured investigations may support broader recovery efforts through exchange communication and compliance coordination. Further details on this aspect are covered in the article on the crypto recovery investigation process.
Limitations of Cryptocurrency Investigations
A professional approach to cryptocurrency investigations requires clear acknowledgment of their inherent limitations. These constraints affect every stage of the workflow and must be factored into the expectations set for any investigation outcome.
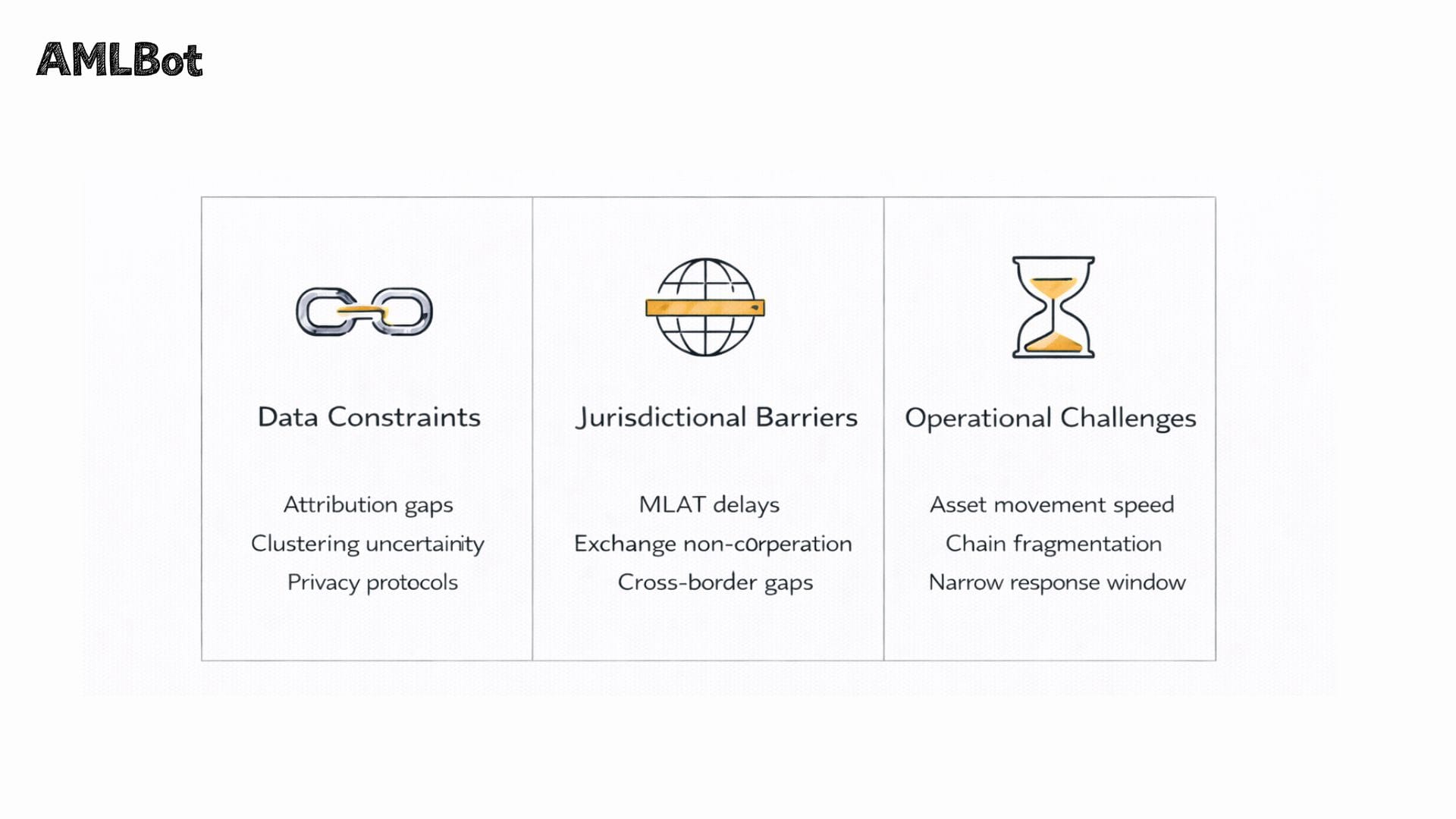
Data Constraints
Attribution analysis depends on the availability and quality of on-chain data combined with off-chain intelligence. Where transactions involve privacy-enhanced protocols, unattributed wallets, or newly created addresses with no prior activity, the investigative record will contain gaps. Wallet clustering relies on probabilistic heuristics, which introduce inherent uncertainty. A cluster may group addresses that are not, in fact, controlled by the same party. These limitations mean that attribution findings must be characterized as analytical assessments rather than definitive conclusions, particularly in contexts where they may influence formal legal or regulatory action.
Jurisdictional Barriers
It is also worth noting that jurisdictional barriers are not limited to uncooperative or unregulated exchanges. Even within well-regulated jurisdictions, the legal process required to compel disclosure, court orders, production notices, or formal MLAT requests takes time that the investigation may not have. Organizations operating across multiple jurisdictions face the additional complexity of determining which legal framework governs a given request and which authority has standing to make it. These procedural realities are not failures of the investigation; they are structural features of the legal environment in which blockchain investigations operate.
The decentralized and cross-border nature of blockchain activity often means that exchanges or service providers holding relevant information are beyond the jurisdictional reach of the investigating party. In the absence of a formal mutual legal assistance treaty (MLAT) process or a regulatory cooperation framework, such as that established under the EU's Markets in Crypto-Assets (MiCA) regulation, which became fully applicable in December 2024, information requests may be declined or go unanswered. Even within cooperative jurisdictions, exchange response times vary considerably, and funds may have moved beyond reach before cooperation is secured.
Operational Challenges
Blockchain transactions are settled in minutes or seconds, far faster than the institutional processes required to freeze assets or compel cooperation. This creates a structural asymmetry between the speed at which illicit actors can move funds and the pace at which investigators can coordinate a response. Cross-chain complexity compounds this challenge, as each additional network layer adds time, correlation uncertainty, and the potential for permanent attribution loss if assets are converted or moved through privacy mechanisms.
The investigative window, the period during which action can meaningfully affect the outcome, is often narrowest precisely when the investigation is most resource-intensive. Early-stage detection and rapid scope definition, as discussed in Stage 1, are therefore not merely process requirements but operational necessities: the faster an investigation can be scoped and the relevant counterparties identified, the greater the probability that coordination efforts will reach assets before they move beyond practical reach. Where that window closes before coordination is possible, the investigation may still produce a complete and accurate record, but the options available at the resolution stage will be correspondingly limited.
The Role of Investigations in the Modern Crypto Ecosystem
Cryptocurrency investigations serve functions that extend beyond individual cases. At an institutional level, they are a mechanism through which compliance teams translate analytics output into actionable risk intelligence, identifying exposure, closing gaps in counterparty risk profiles, and reducing the probability that similar activity goes undetected in future monitoring cycles. At a regulatory level, they are the operational backbone of SAR/STR reporting regimes that depend on organizations being able to substantiate their suspicious activity determinations with documented findings. At an industry level, the quality and consistency of investigation practices affect the degree of institutional trust that enables regulated market participation.
As the regulatory landscape continues to develop, with frameworks such as MiCA in the EU, the updated FATF Recommendations on virtual assets, and ongoing FinCEN rulemaking in the US, the standards applied to investigation workflows are converging toward greater formality and accountability. Organizations that invest in structured investigation capabilities now are better positioned to meet these evolving requirements and to demonstrate credible compliance practices to counterparties, regulators, and the public.
The investigative process is also the connective tissue that links the technical discipline of blockchain analytics to the legal discipline of forensic evidence. It is where data become documentation and analytical findings become the basis for institutional or regulatory action. Understanding this workflow, not just the tools that support it, but the process through which those tools produce outcomes, is foundational to professional practice in the crypto compliance domain.
-AMLBot Team

Follow AMLBot:
🔗 Website
🔗 Telegram
🔗 Support Team
🔗 LinkedIn
FAQ
What Is a Cryptocurrency Investigation?
A cryptocurrency investigation is a structured process that analyzes blockchain activity to determine the nature of suspicious transactions, attribute relevant entities, document findings, and coordinate appropriate responses. It is a multi-stage workflow, not simply a technical analysis exercise.
What Triggers a Cryptocurrency Investigation?
Investigations may be triggered by suspicious transaction alerts, sanctions exposure identified through screening, Travel Rule compliance discrepancies, internal compliance reviews, reported fraud or theft, or irregular account activity flagged by automated monitoring systems.
How Is a Cryptocurrency Investigation Different from Transaction Tracing?
Transaction tracing reconstructs fund movement at a technical level. A cryptocurrency investigation includes tracing but also encompasses attribution analysis, forensic documentation, coordination with exchanges and regulators, and formal escalation decisions, making it a broader operational workflow.
What Role Does Forensic Analysis Play in Cryptocurrency Investigations?
Forensic analysis supports investigations by structuring findings, preserving evidence, and preparing reports for compliance reviews or formal proceedings. It is a component of the investigation workflow, specifically relevant at the documentation and escalation stages.
Do All Cryptocurrency Investigations Involve Scams?
No. While scam-related cases represent one category of investigation, the workflow is equally applicable to sanctions compliance reviews, internal audits, suspicious transaction reporting, regulatory inquiries, and broader fraud cases that do not involve individual victims.
How Do Cross-Chain Transfers Affect Investigations?
Cross-chain transfers increase complexity by fragmenting transaction history across multiple networks. Each network maintains its own ledger, and correlating activity across those ledgers requires additional analytical work, extending the investigation timeline.
Can Cryptocurrency Investigations Guarantee Asset Recovery?
No. Investigations can provide structured findings and support coordination with exchanges or compliance teams, but recovery outcomes depend on timing, jurisdictional cooperation, the responsiveness of relevant service providers, and the specific legal mechanisms available. No investigation process can guarantee recovery.
Who Participates in a Cryptocurrency Investigation?
Participants may include compliance teams, forensic analysts, blockchain analytics professionals, legal advisors, crypto-asset service providers or exchanges (as information or cooperation counterparties), and, in cases involving significant criminal activity, regulatory or law enforcement authorities.
What Are the Main Limitations of Cryptocurrency Investigations?
Primary limitations include incomplete attribution data, uncertainty in wallet clustering heuristics, jurisdictional barriers to exchange cooperation, the speed differential between asset movement and institutional response, and the added complexity introduced by cross-chain activity and privacy-enhanced protocols.
How Do Cryptocurrency Investigations Support Compliance?
Investigations help organizations understand their risk exposure with respect to specific transactions or counterparties, document suspicious activity in a format that satisfies regulatory reporting requirements, including under frameworks such as MiCA and the EU Transfer of Funds Regulation, respond to regulatory inquiries with substantiated findings, and refine internal controls based on identified risk patterns.