Continuous Transaction Monitoring in Crypto: How It Works and Why It Matters

Regulators conducting AML Audits do not assess whether a crypto business has a transaction monitoring system. They assess whether that system would have detected illicit funds flowing through the business during the audit period. The distinction is critical — and it is one that most crypto companies underestimate until an examination or enforcement action makes the consequences concrete.
According to the FATF's 2025 Targeted Update, industry estimates place approximately $51 billion in illicit on-chain activity relating to fraud and scams for 2024 alone. Stablecoins now represent the majority of all illicit transaction volume, and laundering techniques — including cross-chain bridging, mixer usage, and peel chain structures — are increasingly professionalized. A monitoring system that checks a wallet address once at the point of deposit and never revisits it is not monitoring at all. It is a snapshot that becomes obsolete the moment a new sanctions designation is issued, a previously clean address receives funds from a mixer, or a laundering chain reaches one of your customers' wallets through intermediary hops.
This article explains how transaction monitoring works in practice for crypto businesses, from the underlying mechanics of risk scoring and alert generation to the regulatory frameworks that make continuous monitoring a legal obligation, and why the difference between periodic checks and continuous monitoring is the difference between a compliance program that works and one that fails under examination.
What Is Continuous Transaction Monitoring?
In practical terms, the distinction between one-time screening and continuous monitoring is the difference between checking a wallet address against a sanctions list today and re-checking it tomorrow when that list has been updated. A wallet that appears low-risk at the time of an initial deposit may become high-risk the following week if it receives funds from a newly sanctioned address, interacts with a mixer, or is identified as part of a laundering chain by blockchain analytics providers.
The concept is closely related to Know Your Transaction (KYT) — a compliance framework that focuses on monitoring transaction behavior and on-chain risk exposure, as distinct from Know Your Customer (KYC), which focuses on verifying user identity. In a complete AML Compliance Program, both are required: KYC identifies who your customer IS; KYT identifies what they DO. Neither is a substitute for the other.
(Source: FATF Updated Guidance for a Risk-Based Approach to Virtual Assets and Virtual Asset Service Providers, October 2021, requiring VASPs to implement the same preventive measures as financial institutions, including suspicious transaction monitoring and reporting)
How Transaction Monitoring Works in Crypto
Understanding how transaction monitoring works in crypto requires examining four interconnected components: transaction flow tracking, wallet behavior analysis, risk scoring, and alert generation. In a properly implemented system, these components operate continuously and in concert — not as isolated, sequential steps.
Transaction Flow Tracking
The foundational layer of any monitoring system is the ability to track where funds come from and where they go. In the blockchain context, every transaction is publicly recorded and immutable — which means that the raw data for tracking is, in principle, universally available. The challenge is not data access but data interpretation. Transaction flow tracking in a monitoring system involves:
- Inbound Flow Analysis. When a customer deposits funds to the platform, the monitoring system traces the transaction history of the sending address — not just the immediate sender, but the chain of preceding transactions. This reveals whether the funds originated from, or passed through, high-risk sources such as mixers, sanctioned addresses, darknet markets, or known fraud clusters.
- Outbound Flow Analysis. When a customer withdraws funds, the monitoring system evaluates the destination address — identifying whether it belongs to a known service, an unhosted wallet, a sanctioned entity, or an address flagged by blockchain intelligence databases.
- Internal Transfer Patterns. Within the platform itself, monitoring systems track patterns of internal movement — such as rapid cycling between accounts, unusual consolidation of funds from multiple users, or transfers that mirror known layering structures.
In practical terms, effective transaction flow tracking requires multi-chain coverage. A monitoring system that covers Ethereum but not TRON, or that tracks ERC-20 tokens but not native chain transactions, will miss a significant portion of the transaction flows that carry AML risk — particularly given the concentration of illicit stablecoin activity on the TRON Network.
Wallet Behavior Analysis
Beyond individual transactions, monitoring systems analyze the broader behavioral profile of wallet addresses that interact with the platform. This is where pattern recognition becomes critical.
- Transaction Frequency and Volume Patterns. Wallets that exhibit unusually high transaction frequency, rapid deposits followed by immediate withdrawals, or volumes that are inconsistent with the customer's declared profile may indicate structuring, layering, or mule account activity.
- Counterparty Network Analysis. Mapping the wallets that a given address transacts with — and assessing the risk profiles of those counterparties — reveals network-level exposure that individual transaction checks cannot detect. A wallet that transacts exclusively with other wallets linked to a known fraud cluster carries risk even if no single transaction exceeds a monitoring threshold.
- Dormancy and Reactivation. Wallets that remain inactive for extended periods and then suddenly process large-value transactions are a known indicator of accounts that have been compromised, purchased, or are being used as intermediary points in a laundering chain.
- Cross-Chain Movement. Wallets that receive assets on one chain and rapidly bridge them to another — particularly when the bridging breaks the deterministic traceability of the funds — exhibit behavior consistent with chain-hopping laundering techniques.
Risk Scoring
Risk Scoring translates raw transaction data and behavioral observations into quantified, actionable compliance decisions. Every wallet address and transaction that interacts with the platform is assigned a risk score based on a combination of factors — and that score is updated continuously as new data becomes available. The key inputs to a risk scoring system include:
- Direct Exposure. Whether the address has directly interacted with a known illicit entity — a sanctioned address, a mixer contract, a darknet market deposit address, or a wallet attributed to ransomware, fraud, or theft.
- Indirect Exposure. Whether the address has received funds that originated from — or passed through — a high-risk source within a defined number of transaction hops. Indirect exposure represents the majority of real-world illicit fund exposure and requires deep chain tracing to detect — a single-hop check is insufficient.
- Behavioral Risk Indicators. Whether the address exhibits transaction patterns consistent with known laundering typologies — structuring, peel chains, rapid consolidation-and-dispersal, or interaction with freshly created wallets that have no transaction history.
- Jurisdictional and Entity Risk. Whether the address or its counterparties are associated with high-risk jurisdictions identified by the FATF, sanctioned countries, or entities on watchlists maintained by OFAC, the EU, or the UN Security Council.
The critical property of an effective risk scoring system is that scores are dynamic, not static. A wallet that scores low-risk today may score high-risk tomorrow if a newly identified sanctions designation, a mixer interaction, or a fraud attribution changes the risk landscape. Continuous monitoring means continuous re-scoring — not periodic batch updates.
Alerts and Thresholds
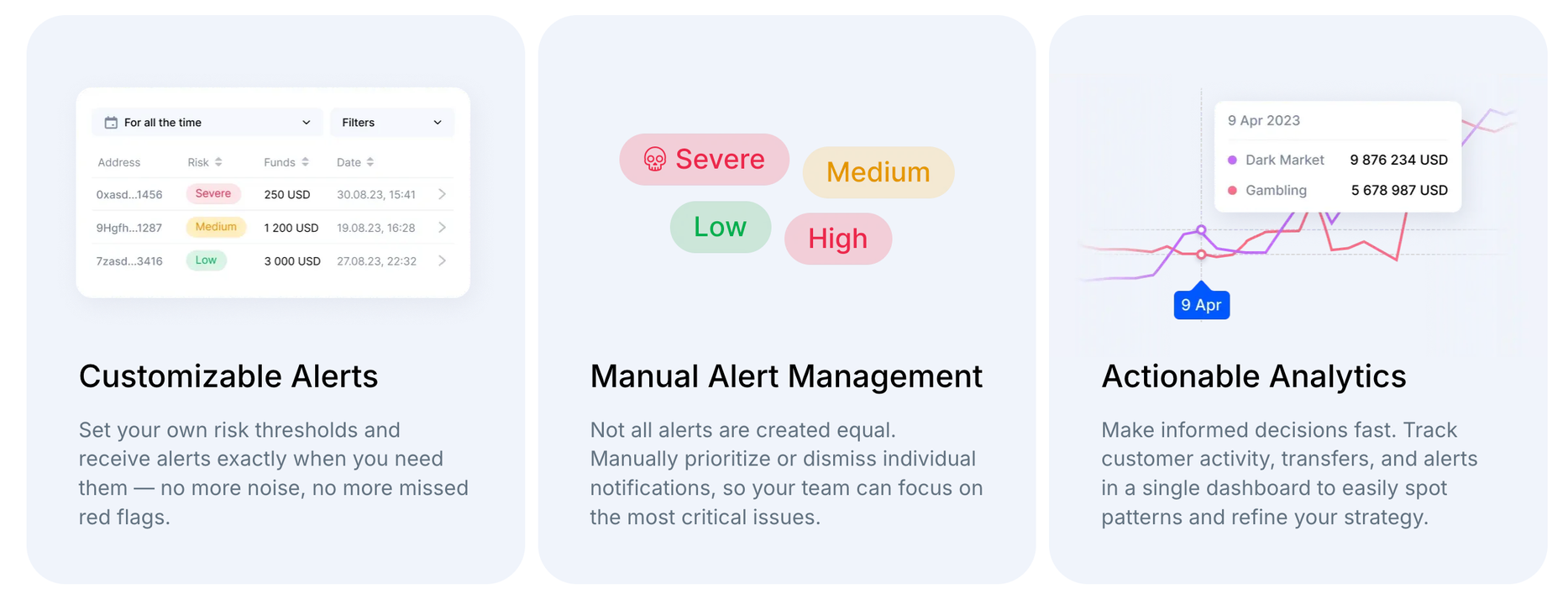
Alerts are the operational output of the monitoring system — the mechanism by which risk is surfaced to compliance teams for review and action. An alert is generated when a transaction, wallet, or behavioral pattern exceeds a defined risk threshold.
- Threshold Configuration. Effective monitoring systems allow businesses to configure alert thresholds based on their own risk appetite — distinguishing between low, medium, high, and critical risk levels. Thresholds should be calibrated to the specific risks the business faces, not set to generic industry defaults.
- Real-Time Generation. Alerts must be generated as close to real time as operationally possible. On-chain transactions settle in minutes; a monitoring system that generates alerts in daily or weekly batch processes will consistently flag activity after funds have already moved beyond the platform's control.
- Contextual Information. An alert that states "high-risk transaction detected" without explaining what triggered it is not actionable. Effective alerts include the specific risk signal — the sanctioned address interaction, the mixer exposure, the behavioral pattern — that caused the threshold to be exceeded, enabling compliance analysts to make informed investigation and escalation decisions.
- Audit Trail. Every alert — including its trigger, the investigation conducted, the disposition decision, and the reasoning — must be logged in a tamper-resistant audit trail. Regulators and auditors evaluate not just whether alerts are generated, but whether they are reviewed, investigated, and resolved in a documented, consistent manner.
Why Transaction Monitoring Is Critical for Crypto Businesses
Transaction Monitoring is not an optional compliance enhancement. Under every major AML framework applicable to crypto businesses, ongoing monitoring of customer transactions is a mandatory obligation — and it is one of the areas most frequently examined during supervisory reviews and compliance audits.
- FATF Requirements. The FATF Recommendations require VASPs to conduct ongoing monitoring of customer transactions as part of their AML/CFT compliance programs. Recommendation 20 requires reporting of suspicious transactions; Recommendations 10–12 require ongoing customer due diligence, which includes monitoring transactions to ensure they are consistent with the institution's knowledge of the customer and their risk profile.
- MiCA and EU Framework. Under MiCA, CASPs authorized in the EU are subject to AML/CFT obligations under the EU's Anti-Money Laundering Regulation (AMLR), which requires obliged entities to apply ongoing monitoring of business relationships — including scrutiny of transactions to ensure they are consistent with the entity's knowledge of the customer. The EU's Transfer of Funds Regulation (TFR) adds specific data transmission requirements for crypto transfers.
- United States (BSA/FinCEN). Under the Bank Secrecy Act, MSBs — including crypto money transmitters — must maintain AML programs that include systems for identifying and reporting suspicious activity. The FFIEC BSA/AML Examination Manual explicitly evaluates whether monitoring systems are commensurate with the institution's risk profile and whether they would have detected suspicious activity during the examination period.
- Banking Partner Expectations. Banks that maintain relationships with crypto businesses conduct their own assessments of transaction monitoring capabilities. A crypto company that cannot demonstrate continuous, automated monitoring will face increasing difficulty obtaining or maintaining banking access — regardless of the regulatory jurisdiction.
(Source: FATF Recommendations 10–12, 20; MiCA, Regulation (EU) 2023/1114; EU AMLR, Regulation (EU) 2024/1624; 31 USC §5318(h); FFIEC BSA/AML Examination Manual)
What Happens Without Transaction Monitoring
The consequences of operating without adequate transaction monitoring — or with monitoring that exists on paper but does not function effectively in practice — are direct and measurable.
- Frozen Funds and Account Restrictions. When a counterparty exchange or banking partner identifies that your platform has processed transactions involving high-risk or sanctioned addresses, they may freeze associated funds or restrict your account pending investigation. Without monitoring, these interactions go undetected until the counterparty's own systems flag them — by which point the reputational and operational damage is already done.
- Regulatory Fines and Enforcement Actions. In 2024, U.S. federal regulators announced more than three dozen enforcement actions against financial institutions for BSA/AML compliance failures. Transaction monitoring deficiencies — including systems that were not configured to detect suspicious activity, alert backlogs that were not reviewed, and monitoring that was not commensurate with the institution's risk profile — were among the most commonly cited findings.
- Loss of Banking Access. Banks terminate relationships with crypto clients when they determine that monitoring controls are inadequate. For a crypto business, loss of banking access means loss of fiat on-ramp and off-ramp capability — effectively an inability to operate.
- Missed Suspicious Activity Reports. Without effective monitoring, suspicious transactions are not identified, alerts are not generated, and SARs are not filed. Failure to file a SAR when required is itself a regulatory violation — and if the missed activity is later connected to a law enforcement investigation, the consequences compound.
- Reputational Damage. Public enforcement actions, counterparty freezes, and association with illicit fund flows undermine trust with customers, institutional partners, and the broader market. In a competitive industry, reputational harm from compliance failures can be more damaging than the financial penalties themselves.
Key Features of an Effective Transaction Monitoring System
While the specific implementation varies by platform, any transaction monitoring system that meets regulatory expectations and operational requirements for crypto businesses must include the following capabilities:
- Continuous Re-Evaluation. The system must re-assess previously screened wallets and transactions as new risk intelligence becomes available — not just screen them once at the point of interaction. This is the defining characteristic that distinguishes continuous monitoring from one-time checks.
- Multi-Chain Coverage. Illicit fund flows do not stay on a single blockchain. Effective monitoring must span the chains where the business operates and where its customers' funds originate — including Ethereum, TRON, Bitcoin, Solana, and relevant Layer 2 networks.
- Dynamic Risk Scoring. Risk scores must update automatically as new sanctions designations, entity attributions, or behavioral patterns are identified. A static score assigned at the time of a deposit and never revised provides no ongoing compliance value.
- Configurable Alerts with Contextual Detail. Alerts must be configurable to the business's risk appetite and must include sufficient context — the specific trigger, the risk signal, the exposure pathway — to enable efficient investigation and documented disposition.
- Behavioral Pattern Detection. Beyond individual transaction screening, the system must detect multi-transaction patterns — structuring, peel chains, rapid consolidation-and-dispersal, dormant wallet reactivation, and cross-chain bridging sequences — that indicate laundering or fraud activity.
- Audit-Ready Documentation. Every screening result, alert, investigation, and disposition must be logged with timestamps and analyst attribution in a format that satisfies regulatory examination requirements. Undocumented monitoring is treated as no monitoring during an audit.
- API Integration Capability. For businesses processing high transaction volumes, manual dashboard-based monitoring is insufficient. The system must support programmatic integration via API, enabling automated risk assessment at the point of transaction without introducing processing delays.
How AMLBot Helps with Transaction Monitoring
AMLBot's Transaction Monitoring platform is built around the operational requirements outlined in this article — continuous re-evaluation, multi-chain coverage, dynamic risk scoring, real-time alerts, and audit-ready documentation.
- Continuous Monitoring with Re-Screening. AMLBot's KYT platform continuously re-screens active wallets and transactions against an up-to-date risk database. As soon as a condition is met — a wallet's risk score crosses a configured threshold, or it receives funds from a newly flagged address — the system generates an alert in real time.
- Multi-Chain and Multi-Asset Coverage. The platform supports monitoring across major blockchains — including Ethereum, TRON, Bitcoin, Solana, and Layer 2 Networks — covering native assets, stablecoins, and token transfers.
- Configurable Alert Rules. Compliance teams can tailor alert rules to their specific risk appetite — monitoring transaction patterns, counterparties, volumes, routing, and exposure depth. All alerts are logged with details and timestamps, producing an audit trail suitable for regulatory examination.
- Behavioral Alerts. Beyond transaction-level screening, AMLBot's Behavioral Alert System detects multi-transaction patterns — identifying structuring, rapid fund cycling, dormant wallet reactivation, and other behavioral indicators that single-transaction checks cannot surface.
- API Integration. For high-volume platforms, AMLBot provides KYT API integration that enables automated, programmatic risk assessment at the point of each transaction — without manual dashboard intervention and without introducing processing latency.
Conclusion
Understanding how transaction monitoring works in crypto is the foundation of a compliance program that can withstand regulatory examination, maintain banking relationships, and detect the illicit fund flows that increasingly target the virtual asset ecosystem. The difference between a monitoring system that checks once and one that monitors continuously is the difference between a compliance program that looks adequate on paper and one that functions in practice.
The regulatory expectation is clear: VASPs must implement systems capable of identifying suspicious activity in real time, re-evaluating risk as new intelligence becomes available, and documenting every compliance decision in an audit-ready format. The businesses that meet this standard are the ones that survive supervisory examinations, maintain institutional partnerships, and operate with confidence in an environment where on-chain risk changes faster than any periodic review can capture.
-AMLBot Team

FAQ
What Is Transaction Monitoring in Crypto?
Transaction Monitoring in crypto is the process of continuously analyzing blockchain transactions to detect suspicious activity, assess risk, and ensure compliance with AML Regulations.
What Is Continuous Transaction Monitoring?
Continuous Transaction Monitoring means that transactions are not checked just once but are re-evaluated over time as new risk data and intelligence become available.
How Does Transaction Monitoring Work in Crypto?
Transaction Monitoring works by analyzing wallet activity, tracking transaction flows, assigning risk scores, and generating alerts when suspicious patterns or high-risk entities are detected.
What Is KYT (Know Your Transaction)?
KYT is a compliance process that focuses on monitoring transaction behavior rather than user identity, helping businesses detect illicit activity such as fraud, money laundering, or sanctions exposure.
What Is the Difference Between KYC and KYT?
KYC verifies the identity of a user, while KYT analyzes transaction activity. KYC and KYT are required for a complete AML Compliance Framework.
Is Transaction Monitoring Required for Crypto Businesses?
Yes, transaction monitoring is required or strongly expected under global AML regulations, including FATF Recommendations and frameworks like MiCA in the EU.
What Risks Does Transaction Monitoring Help Prevent?
It helps prevent money laundering, fraud, sanctions violations, exposure to illicit funds, and regulatory penalties.
How Do Crypto Exchanges Monitor Transactions?
Crypto exchanges use blockchain analytics tools and KYT systems to track transactions in real time, flag suspicious activity, and manage risk across user accounts.
What Features Should a Transaction Monitoring System Include?
Key features include real-time monitoring, risk scoring, automated alerts, wallet analysis, transaction tracing, and integration via API.
What Happens If a Crypto Business Does Not Use Transaction Monitoring?
Without monitoring, businesses risk regulatory fines, frozen accounts, loss of banking access, reputational damage, and exposure to financial crime.