Pig Butchering Crypto Scam: Real Case, Red Flags, and Recovery Steps

In November 2025, the U.S. Department of Justice established a dedicated Scam Center Strike Force — an interagency task force specifically targeting Southeast Asian scam operations. By the time of its announcement, the Strike Force had already seized over $401 million in cryptocurrency and was pursuing an additional $80 million in forfeiture proceedings. According to U.S. government estimates, Americans alone lost at least $10 billion to these operations in 2024 (a 66% increase over the prior year) with Pig Butchering schemes accounting for the dominant share of losses.
A Pig Butchering scam is not what most people picture when they think of crypto fraud. There is no phishing email, no malicious link in a stranger's message, no urgent demand for payment. Instead, the scheme begins with a relationship — weeks or months of genuine-feeling conversation, emotional connection, and gradually building trust. The investment "opportunity" comes later, introduced naturally by someone the victim already trusts. The fake platform looks professional. The first withdrawal succeeds. By the time the victim realizes what has happened, the losses are substantial.
This article examines how a pig butchering crypto scam unfolds in practice, based on a real case investigated by AMLBot, what red flags were missed, what the investigation revealed, and what steps matter after funds have been sent to a fraudulent platform.
What Is a Pig Butchering Scam?
A Pig Butchering scam (named after the Chinese phrase "shā zhū pán," meaning to fatten a pig before slaughter) is a type of long-form investment fraud in which scammers build a personal relationship with a victim before directing them to a fake crypto investment platform. The "fattening" phase involves weeks or months of trust-building. The "slaughter" occurs when the victim has deposited a significant amount and discovers that withdrawals are blocked, new fees are demanded, and the platform — and the person who introduced it — disappears.
What distinguishes Pig Butchering from other crypto scams is the combination of social engineering and financial fraud. It is not a pure romance scam — the emotional relationship exists to enable the financial extraction, not as the primary mechanism. And it is not a simple investment scam — the personal relationship is what makes the fraudulent platform credible. The trust the victim places in the other person transfers directly to the platform they recommend.
In practical terms, Pig Butchering schemes typically involve cloned or fabricated investment platforms that mimic legitimate exchanges, staged withdrawals designed to build confidence, escalating deposit requests, and — when the victim attempts a large withdrawal — sudden demands for "taxes," "credit score improvements," "security deposits," or other fabricated fees. Each new fee creates the illusion that the victim is one payment away from accessing their funds. In reality, every additional payment goes directly to the scam operators.
On-chain security research identified over 200,000Ppig Butchering-related cases on the Ethereum network alone in 2024, with estimated losses exceeding $5.5 billion. The FBI's Internet Crime Complaint Center reported $9.3 billion in total investment scam losses in the same year, with Pig Butchering as the dominant subcategory.
AMLBot's own Crypto Crime Report 2025–2026, based on the analysis of 2,500+ real post-incident investigations, confirmed the same pattern at the case level: investment scams accounted for 25% of all investigated cases — the single largest category by volume — with Pig Butchering identified as the most financially damaging subset, characterized by prolonged trust-building phases that delay victim recognition and reduce the likelihood of timely intervention.
How This Scam Worked in Practice
The following is not an abstract scenario. It is the sequence of events from a real case investigated by AMLBot — representative of the pattern that recurs across hundreds of similar cases. Each step appeared reasonable to the victim at the time it occurred. That is what makes this scheme effective.
Trust-Building Through Personal Contact
The case began with an online connection that developed into a regular, personal relationship over several weeks. The two communicated daily — through messaging, voice calls, and video calls. The conversations were not transactional. They covered personal topics, daily life, plans, and interests. The scammer invested significant time in building a relationship that felt genuine, reciprocal, and trustworthy.
This phase is the scam's most important component. The psychological foundation laid during trust-building is what makes every subsequent step possible. When a recommendation to invest comes from someone you have spoken with daily for two months, it does not feel like a pitch from a stranger. It feels like advice from someone who cares about your financial well-being.
The Fake Investment Platform
After the relationship was established, the other person casually mentioned an investment opportunity — a crypto trading platform where they had been "making consistent returns." The platform had a professional-looking interface, displayed real-time price charts, and included features that mimicked legitimate exchanges. The scammer offered to walk the victim through the process, provided guidance on how to deposit, and shared their own "portfolio performance" as evidence.
In this case, the platform was a clone — visually similar to a known, reputable exchange, but operating on a separate domain controlled entirely by the scam network. The victim had no reason to doubt the platform's legitimacy because the recommendation came from someone they trusted, and the interface appeared identical to a real service.
A Small Withdrawal That Built Trust
After the victim made an initial deposit and the platform displayed apparent profits, they requested a withdrawal. The withdrawal was processed successfully — the funds arrived in the victim's wallet within hours.
This staged withdrawal is one of the most effective elements of the scheme. It eliminates the victim's primary concern ("Is this real?") by providing tangible evidence that the platform works. After a successful withdrawal, the victim's confidence increases dramatically — and so does the next deposit. In the case investigated by AMLBot, the victim's deposits escalated from thousands to tens of thousands of dollars after this confirmation step.
Fake Taxes, Credit Score Boosts, and Withdrawal Barriers
When the victim's balance on the platform had grown substantially — through a combination of additional deposits and fabricated "returns" — they attempted a larger withdrawal. This time, the withdrawal was not processed. Instead, the platform displayed a notification requiring a "tax payment" before funds could be released.
After the tax was paid, a second requirement appeared: a "credit score improvement fee." Then a third: a "security verification deposit." Each new demand created the illusion that the process was legitimate — that the victim was navigating bureaucratic steps, not being defrauded. The scammer reinforced this narrative through personal messages, offering reassurance ("I had to do the same thing," "this is standard procedure," "I'll help you through it").
In practical terms, every "fee" the victim paid went directly to the scam network. The platform never held any real assets. The displayed balance was a number on a screen controlled by the operators. The withdrawal barriers were designed to extract the maximum amount before the victim recognized the fraud.
What AMLBot's Investigation Found
When the victim contacted AMLBot, the case transitioned from a personal loss to a structured investigation. What the analysis revealed was not an isolated incident — it was a node in a larger, operationally sophisticated fraud infrastructure.
Links to a Broader Scam Network
Blockchain analysis of the wallet addresses involved in this case revealed connections to addresses associated with other known fraud operations. The wallets receiving the victim's funds shared transactional patterns — timing, amounts, and routing structures — with wallets identified in separate pig butchering investigations. This is consistent with the operational model of professionalized scam syndicates, which operate multiple concurrent schemes using shared infrastructure, shared laundering pipelines, and — in many cases — shared victim acquisition channels.
The investigation also identified links to wallet clusters previously flagged by blockchain intelligence providers as associated with forced-labor scam compounds in Southeast Asia — a pattern that aligns with the broader intelligence picture documented by law enforcement agencies and the OFAC designations issued in 2025 against scam compound operators.
How the Funds Moved After the Transfer
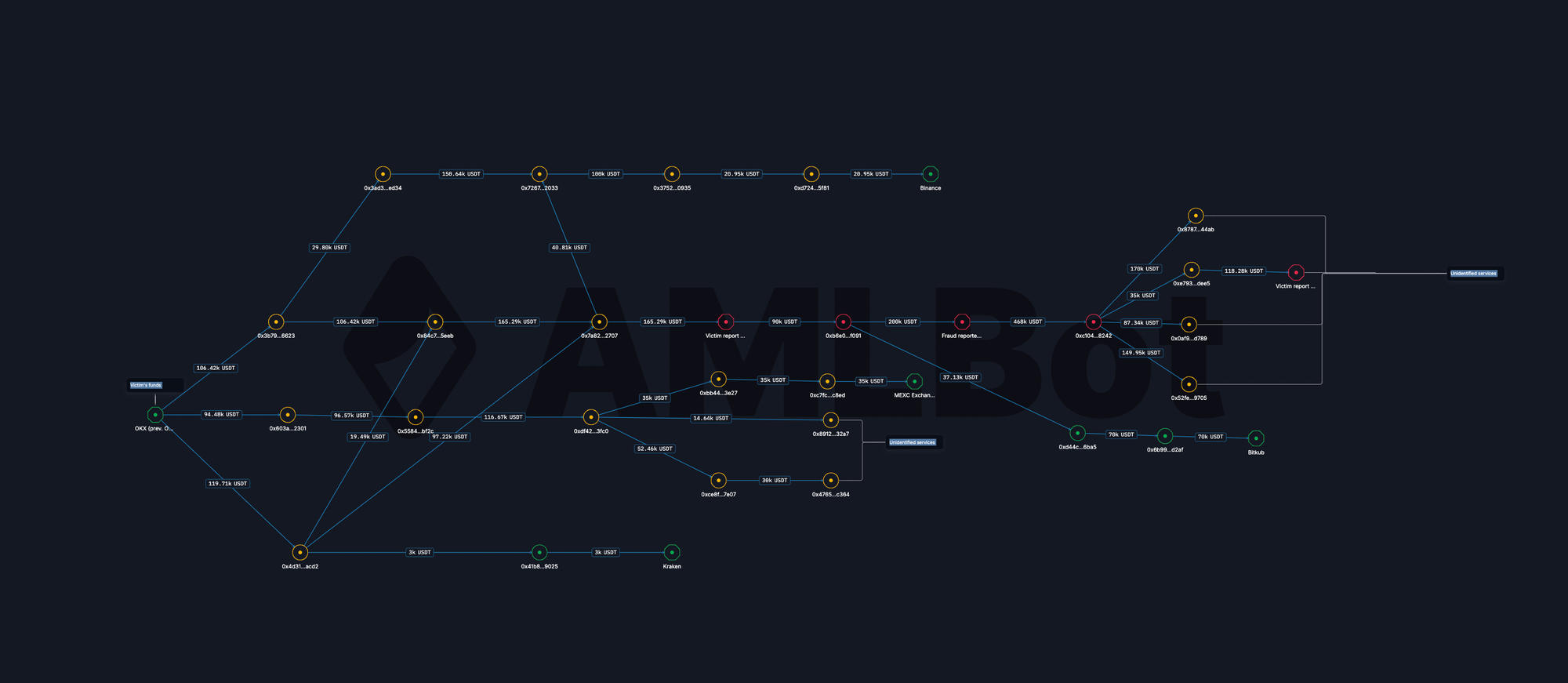
Once the victim's deposits reached the scam-controlled wallets, the funds were rapidly fragmented and moved through a chain of intermediary addresses. The movement pattern showed:
- Immediate Fragmentation. Within hours of receipt, the funds were split across multiple wallets — breaking the single deposit into smaller amounts distributed across a network of addresses.
- Conversion to Stablecoins. A significant portion of the fragmented funds was converted to USDT — consistent with industry-wide data showing that stablecoins account for the dominant share of illicit transaction volume due to their liquidity and dollar-pegged stability.
- Movement Toward Exchange Touchpoints. Some portions of the funds ultimately reached deposit addresses associated with centralized, regulated exchanges — creating potential intervention points where freeze requests could be directed.
- Cross-Chain Bridging. Other portions were moved from Ethereum to TRON through bridge protocols, breaking on-chain traceability and complicating further tracking.
This post-transfer movement pattern is not unique to this case. It is the standard laundering workflow for professionalized scam operations — designed to move value away from the initial collection point as quickly as possible, fragment it to complicate tracing, and route portions through regulated intermediaries where conversion to fiat can occur.
Where Freezing Opportunities Appeared
Recovery opportunities in crypto fraud cases are not unlimited — they depend on where the funds go and how quickly action is taken. In this case, the investigation identified specific touchpoints where funds had reached regulated exchanges — custodial platforms that are legally capable of freezing assets in response to law enforcement requests, court orders, or compliance-driven interventions.
These touchpoints represent the window where action can materially affect outcomes. Once funds reach a regulated intermediary, the intermediary can freeze the associated account, preserve the assets, and cooperate with law enforcement or legal proceedings. Before that point — while funds are moving through non-custodial wallets — there is no entity with the authority or ability to intervene.
In practical terms, this means that tracing alone does not equal recovery. Tracing identifies where funds went. Recovery depends on whether funds reached an entity that can act — and whether the request to act arrives before the funds move again.
Why Speed Mattered in This Case
The time between the victim's last deposit and the moment AMLBot began tracing was a critical variable. Scam operators move funds quickly — typically within hours to days of receipt. Every day of delay narrows the window of opportunity, because funds that sat at a regulated exchange yesterday may have been withdrawn and fragmented today.
In this case, relatively prompt reporting meant that portions of the funds were still identifiable at exchange touchpoints when the investigation began. A delay of even several additional days could have closed that window entirely. This is consistent with the pattern across AMLBot's broader case portfolio: the cases with the most actionable outcomes are those where the victim engaged professional support quickly — not because speed guarantees recovery, but because it maximizes the range of available options.
Pig Butchering Red Flags Victims Often Miss
The following are not generic fraud indicators. They are specific to the Pig Butchering scam pattern. Signals that, in retrospect, appeared in this case and in the majority of similar cases AMLBot has investigated.
- Relationship First, Investment Second. The investment "opportunity" is always introduced after a personal connection is established — never at first contact. If someone you met online begins discussing crypto investments after building rapport over weeks, the sequence itself is a signal.
- Recommendation of a Specific Platform. The person directs you to a particular platform — not a well-known, independently verifiable exchange, but a specific URL they provide. This is the mechanism by which victims are moved from a legitimate market to a controlled environment.
- A Successful Small Withdrawal Before a Larger Deposit. This is the credibility-building step. If a platform allows a small withdrawal but later blocks a larger one — or if the small withdrawal was the moment that convinced you to deposit significantly more — the staged withdrawal was the trap.
- Extra Payments Required to Unlock Withdrawals. Any platform that demands additional payments — "taxes," "verification fees," "credit score deposits," "insurance premiums" — before releasing funds that are already supposedly yours is operating a scam. Legitimate exchanges do not require customers to pay fees to access their own assets.
- "I'm Invested Too" and "I Know Support Personally." The scammer reinforces the platform's credibility by claiming to be invested themselves and by offering to connect the victim with "platform support." This creates an additional layer of false trust — the victim believes they have both a personal advocate and a responsive service team.
- Pressure to Continue Rather Than Independently Verify. When the victim expresses doubt or hesitation, the response is always to continue — never to independently verify the platform through external sources. Legitimate investment advisors welcome independent verification. Scammers discourage it.
What to Do If You Already Sent Funds
If you have already transferred funds to a platform you now suspect is fraudulent, the most important actions are immediate and practical. These steps do not guarantee recovery, but they preserve the evidence and the time window that make professional investigation and potential recovery possible.
- Stop Sending More Money Immediately. If the platform is demanding additional payments to "unlock" withdrawals, every payment is going directly to the scam operators. No amount of additional fees will result in fund release from a fraudulent platform.
- Preserve All Evidence. Save every piece of documentation related to the case: wallet addresses, transaction hashes (TXIDs), timestamps, deposit confirmations, screenshots of the platform interface, and any payment requests received.
- Save All Communications. Chat logs, messaging app conversations, emails, phone numbers, social media profiles, and the domains or URLs of the platform. This information is essential for tracing, attribution, and any subsequent legal action.
- Contact the Exchange or Service Involved. If you sent funds from a centralized exchange, contact that exchange's compliance or support team immediately. They may be able to flag the receiving addresses, alert downstream platforms, or cooperate with law enforcement.
- Submit the Case Quickly. Time is the most critical variable. The sooner a professional investigation begins, the more likely it is that funds are still identifiable at points where intervention is possible. Delays of days or weeks can mean the difference between traceable assets and fully laundered proceeds.
When Recovery Is Possible — and What Affects It
Recovery of funds lost to a pig butchering scam is sometimes possible — but it is not always possible, and the outcome depends on a specific set of variables that are outside the victim's control once funds have been sent.
- Where the Funds Went. Recovery is most realistic when funds reach a regulated exchange or custodial service — an entity that can freeze assets, cooperate with law enforcement, and participate in legal proceedings. If funds moved to non-custodial wallets, mixers, or were dispersed through cross-chain bridges, the ability to intervene drops significantly.
- How Quickly the Case Was Reported. Speed is the most actionable factor. Scam operators move funds rapidly. Every hour that passes reduces the likelihood that funds are still sitting at an intervention point.
- Whether the Counterparty Is Identifiable. If the receiving wallets or downstream exchange accounts can be attributed to identifiable individuals or entities, legal and law enforcement action becomes feasible. If funds disappeared into an unattributed, non-custodial wallet network, the options narrow.
- Jurisdictional Enforceability. Even when funds are traceable and the recipient is identifiable, recovery ultimately depends on whether a court, regulator, or law enforcement agency in the relevant jurisdiction can and will take enforcement action. Some jurisdictions cooperate readily; others do not.
- Tracing Is Not the Same as Recoverability. Blockchain tracing can identify where funds went — but the ability to follow funds on-chain does not mean those funds can be recovered. Recovery requires that traced funds reach an entity that can act, and that legal or compliance mechanisms are available to compel that action.
How Professional Crypto Recovery Works
Professional crypto recovery is not the same as the "recovery services" that scam victims often encounter after the fact — many of which are themselves fraudulent, promising guaranteed returns in exchange for upfront fees. Legitimate recovery work is investigative, evidence-based, and transparent about the uncertainty of outcomes.
A professional investigation typically involves:
- Fund Tracing and Wallet Analysis. Mapping the movement of stolen funds across wallets, chains, and service touchpoints — identifying where funds went, which intermediaries were used, and whether any portion is still accessible.
- Wallet Flagging and Monitoring. Flagging identified scam-controlled wallets in blockchain intelligence databases so that exchanges and compliance systems can detect and act on future interactions with those addresses.
- Exchange Outreach and Escalation. Contacting regulated exchanges where funds have been identified, providing evidence packages, and requesting account freezes or cooperation with law enforcement.
- Law Enforcement Coordination. Preparing investigative reports, evidence documentation, and technical analysis in formats that law enforcement agencies and prosecutors can use — supporting criminal investigations, asset forfeiture proceedings, or civil recovery actions.
- Honest Case Assessment. Evaluating whether recovery is realistically feasible in a given case — based on where funds went, how much time has passed, and what legal mechanisms are available — rather than promising outcomes that cannot be guaranteed.
Need Help with a Pig Butchering Scam Case?
If you have sent funds to a platform you now believe is fraudulent, early action materially improves the chances of preserving evidence and identifying recovery opportunities. The sooner tracing begins and exchange escalation is initiated, the wider the window for potential intervention.
AMLBot's Reclaim Crypto service provides structured investigation support for fraud victims — including fund tracing, wallet analysis, exchange outreach, evidence documentation, and law enforcement coordination. There are no upfront promises of guaranteed recovery. There is a realistic case assessment, a clear investigative process, and actionable steps based on what the evidence shows.
If you need help, start a crypto scam investigation.
Conclusion
Pig Butchering works because it does not look like a scam. It looks like a relationship, a shared interest, and a credible investment opportunity recommended by someone you trust. The damage accumulates not because victims are careless, but because the scheme is designed to feel personal, reasonable, and safe at every step — until it is not.
The most consequential decision a victim can make after recognizing the fraud is to stop sending additional funds. Every "fee" demanded to unlock a withdrawal is an extension of the scam, not a step toward resolution. The second most consequential decision is to act quickly — preserving evidence, documenting everything, and engaging professional support before the window for tracing and intervention narrows further.
What Is a Pig Butchering Scam in Crypto?
A Pig Butchering scam is a type of crypto fraud where scammers first build trust through friendly or romantic communication and then introduce a fake investment opportunity. The goal is to convince the victim to keep sending more money until withdrawals are blocked and new fake fees appear.
How Does a Pig Butchering Scam Usually Work?
The scam usually starts with regular conversations that feel personal and harmless. After trust is established, the victim is directed to a fake investment platform, allowed to withdraw a small amount at first, and then pressured to deposit more until the platform demands extra payments and stops releasing funds.
Why Are Pig Butchering Scams So Effective?
These scams work because they combine emotional manipulation with a believable investment story. The victim often feels they are acting on advice from someone they trust rather than responding to an obvious scam.
What Are the Main Warning Signs of a Pig Butchering Scam?
Common warning signs include someone you met online pushing a specific investment platform, promises of easy profits, a successful small withdrawal used to build confidence, and later demands for taxes, unlocking fees, or account upgrades before you can access your money.
What Should I Do If I Already Sent Crypto to a Fake Platform?
Stop sending more money immediately and preserve all evidence. Save wallet addresses, transaction hashes, screenshots, chat logs, platform URLs, and payment requests, then contact the exchange or service involved and submit the case as quickly as possible.
Can Stolen Crypto from a Pig Butchering Scam Be Recovered?
Recovery is sometimes possible, but it depends on how quickly the case is reported, where the funds moved, and whether they reached a regulated exchange or identifiable service. Tracing the funds does not automatically mean recovery is guaranteed.
What Affects the Chances of Recovering Stolen Crypto?
The main factors are speed, the availability of transaction evidence, whether the funds reached a custodial platform, and how heavily the scammers tried to hide the trail through multiple wallets, cross-chain transfers, or other obfuscation methods.
How Can a Crypto Investigation Help After a Pig Butchering Scam?
A professional investigation can trace fund flows, identify wallet connections, detect exchange touchpoints, document evidence, and support escalation to exchanges or law enforcement. This helps the victim understand what happened and whether there are realistic recovery options.
How Does AMLBot Help in Pig Butchering Scam Cases?
AMLBot helps by tracing stolen funds, analyzing wallet activity, identifying links to broader scam networks, monitoring movements, and supporting evidence collection for exchanges and legal follow-up. The goal is to create a clear investigative picture and improve the chances of timely action.
When Should Someone Contact a Crypto Recovery or Investigation Service?
They should do it as soon as they suspect fraud or realize they cannot withdraw funds. In pig butchering cases, delays often make recovery harder because scammers move assets quickly across wallets and platforms.