Crypto Transaction Tracing: Fund Flow Analysis Explained
When you look up a wallet on a block explorer, you can see individual transactions — amounts, addresses, timestamps. But that's not the same as understanding where money actually came from or where it ended up. Transaction tracing goes further. It reconstructs the full movement of funds across multiple addresses and transactions, turning raw blockchain data into a coherent fund flow map. This matters because illicit actors rarely move money directly from point A to point B. They route it through chains of wallets, split it, merge it, and mix it with other funds to obscure its origin.
This article focuses on the mechanics of tracing works — rather than compliance frameworks or legal procedures —the actual process of following crypto from entry to exit.
What Transaction Tracing Actually Means
It's 2013, and a federal agent is staring at a screen full of Bitcoin addresses. He knows Mt. Gox, then the world's largest crypto exchange, is hemorrhaging money. He knows funds are moving. But the blockchain explorer just shows him a wall of hashes — and no story. That gap between seeing transactions and understanding money movement is exactly what transaction tracing was built to close.

Blockchain Analysis isn't one thing. It's a whole spectrum. At the basic end, you've got wallet screening: you take an address, run it through a database, and get back a simple verdict — clean or flagged. One step up is transaction review: you zoom in on a single transfer and ask who sent what to whom, and why that particular transaction looks suspicious. But neither of those tells you the full story. That's where tracing comes in.
When an investigator does a full trace, they're not looking at one address or one transaction. They're rebuilding the entire journey of a sum of money — from the moment it hit the blockchain, through every wallet it passed through, to the point where someone finally tried to cash out.
The old financial crime principle — Follow the Money — translates almost perfectly to crypto. In fact, in some ways it works even better here. Unlike a wire transfer that can be buried in banking records, every on-chain transaction is public, permanent, and timestamped. The difference between screening and tracing comes down to one word: scope. Screening gives you a snapshot of one address. Tracing gives you the full "movie" — entry point, every scene in between, and the exit.
The Core Mechanics of Transaction Tracing
Identifying the Starting Point
Every trace has to start somewhere. In practice, that starting point is almost always a specific wallet address connected to a known event — a fraud report, a ransomware payment, a sanctions list hit, or an alert from a monitoring system that flagged something unusual. The quality of that anchor matters more than people realize. A clearly identified suspicious address gives investigators a solid foundation. A vague or unverified starting point can send an entire investigation sideways from step one. What usually ends up as the entry anchor? Addresses caught directly in a theft or scam. Wallets that received funds from a sanctioned entity. Addresses that suddenly lit up with large deposits from multiple unrelated sources. Wallets that victims reported after losing money to a Phishing Attack or Fake Exchange.
Following Transaction Chains
Here's where the actual detective work begins. From the anchor address, an analyst traces every wallet that received funds from it — then every wallet that received funds from those wallets — and so on. The result is a transaction graph: a map where wallets are nodes and transactions are the edges connecting them.
Each transaction in that graph carries four pieces of information: the sending address, the receiving address, the amount, and the timestamp. That last one matters more than you'd think. Time-based sequencing — understanding not just where money went but how fast and in what order — is often what reveals intent.
The catch is that funds almost never travel in a straight line. Multi-hop transfers are the norm. Illicit actors route money through intermediary wallets — sometimes dozens, sometimes hundreds — specifically to exhaust investigators who are following manually. Automated tools handle this by recursively mapping every outgoing transfer from every newly discovered address, building out the graph until the funds either reach a known entity (like an exchange) or simply go cold.
Detecting Consolidation and Layering Patterns
Analysts learn to recognize structural patterns that indicate deliberate obfuscation. Consolidation happens when funds from many different addresses flow into a single wallet, often a sign that an actor is aggregating proceeds before a final cash-out. Peeling Chains work in the opposite direction: a large sum moves through a long sequence of wallets, with a small amount "peeled off" at each step to a different address, gradually shrinking the main balance. Rapid Splitting divides a single balance into multiple smaller amounts and sends them simultaneously to dozens of addresses, thereby fragmenting the trail. Layering Behavior refers to the broader strategy of adding unnecessary complexity to fund movements—multiple hops, frequent denomination changes, and unnecessary intermediate wallets, specifically to obscure the funds' origin.
For a deeper explanation of how chain hopping, mixers, DeFi activity, and wallet fragmentation combine into full laundering sequences, see Layering in Crypto AML: How It Works and How to Detect It.
Identifying Exit Points
The goal of tracing is to determine where funds left the blockchain ecosystem or reached a point at which identity verification is possible. These are called exit points.
The most significant are centralized exchanges, where users complete identity verification. When a trace leads to an exchange deposit address, investigators know the funds were converted by an identified account holder. Other common exit points include crypto ATMs, OTC Trading Desks, P2P Marketplaces, and merchant payment services.
One increasingly important route involves cross-chain movement—moving funds via bridges or decentralized exchanges that connect different blockchains. This adds significant complexity because the fund flow crosses technical boundaries between entirely different systems. The mechanics of this are explored in cross-chain transaction analysis.
Common Laundering Patterns Observed in Transaction Tracing
There are many ways illicit fund flows try to break a clean trace — some create real distance, others create noise, and some simply overwhelm the graph until the signal gets buried. Below, we’ll take a closer look at a few of the most common patterns analysts encounter in transaction tracing, and unpack why each one makes fund flow reconstruction harder even when everything remains visible on-chain.
Chain Hopping
So, imagine you're tracing a wallet on Ethereum. You've followed the funds through a dozen intermediary addresses, and the trail is clear. Then the money hits a bridge contract and vanishes. On the other side of that bridge, on a completely different blockchain, new funds appear. Same value, different network, different address format, no shared transaction ID connecting the two. To understand why chain hopping works so well, you first need to understand a basic fact about how blockchains are built: they don't talk to each other natively. Ethereum doesn't know what's happening on BNB Chain. BNB Chain doesn't know what's happening on TRON. Each network maintains its own ledger, its own address format, its own transaction structure. There is no shared database that connects them. This means that when funds move from one chain to another, nothing on either blockchain records that movement as a single event. What gets recorded instead are two separate, unrelated-looking transactions — a deposit on the source chain, and a withdrawal on the destination chain. Linking them requires either specialized cross-chain analytics tools or the internal records of the bridge protocol itself, which is a private database nobody can subpoena without knowing who runs it.
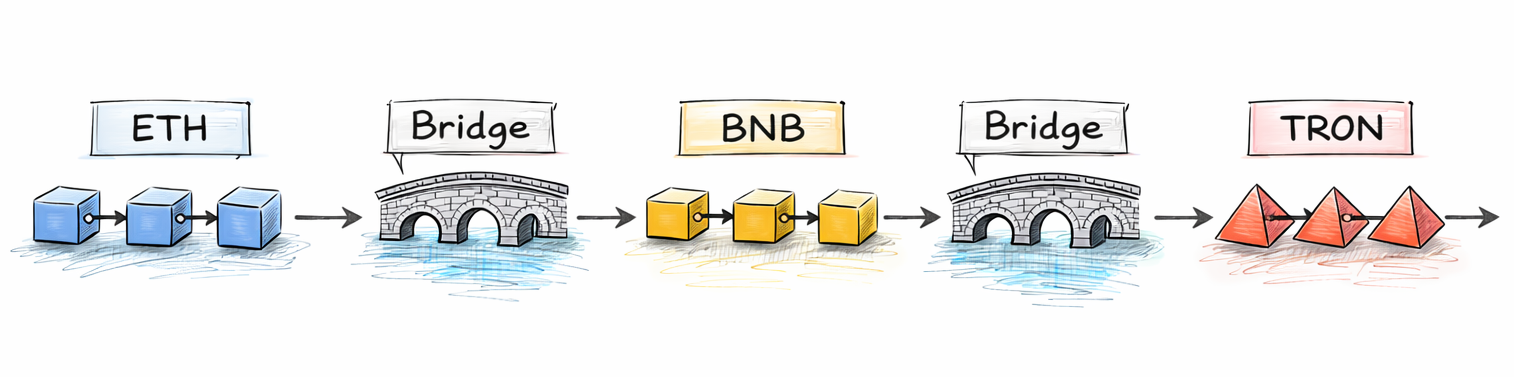
A bridge is a smart contract, or a set of smart contracts, that coordinates asset movement between two blockchains. The mechanics vary by protocol, but the general flow looks like this. A user sends funds to the bridge contract on the source chain. The contract locks those funds — they sit there, held by the protocol. The bridge then monitors both chains simultaneously, detects the incoming deposit, and triggers a corresponding action on the destination chain: either minting new wrapped tokens, releasing pre-held reserves, or creating an equivalent balance. The user receives funds on the destination chain from what appears to be the bridge's own wallet, not from the original sender. That last part is key. On the destination chain, the transaction shows the bridge's address as the sender. The original source wallet is nowhere in the picture. Unless you know to look for the corresponding bridge deposit on the source chain, and you have a tool capable of matching them, the connection is invisible.
Let's make this concrete with the classic Chain-Hopping. (Picture 1)
- ETH to BNB Chain. The actor sends ETH to a bridge contract on Ethereum. The bridge locks the ETH and releases an equivalent amount on BNB Chain, either as wrapped ETH or converted to BNB through an automated swap. Both Ethereum and BNB Chain use the same address format (they're both EVM-compatible, starting with
0x), which looks deceptively similar, but they are entirely separate ledgers. The transaction hash on Ethereum and the transaction hash on BNB Chain share no common identifier whatsoever. At this point, a standard Ethereum tracing tool loses the thread completely. It can see the funds hitting the bridge contract. It cannot see what happened next, because "next" happened on a different blockchain the tool doesn't monitor. - BNB to TRON. Now on BNB Chain, the actor uses another bridge, or a cross-chain DEX aggregator, to move funds to TRON. Here the address format changes completely. TRON addresses start with a capital
Tand use a different encoding standard (Base58Check) compared to EVM's hexadecimal format. A BNB Chain analytics tool tracking0x7f4e...has no way to automatically know thatTQn9Y...on TRON is the next step in the same fund flow. The technical identifiers are structurally incompatible. - TRON to Bitcoin. This is where the format change becomes most dramatic. Bitcoin uses a completely different cryptographic model, UTXO-based, compared to the account-based model of EVM chains and TRON. Bitcoin addresses look nothing like EVM or TRON addresses. There is no smart contract layer to interact with. A cross-chain protocol like THORChain handles this conversion by running nodes on both chains simultaneously, matching deposits and payouts through its own internal liquidity pools. The result on the Bitcoin side is a transaction originating from THORChain's own Bitcoin wallet, with no traceable link to the TRON address that initiated the swap.
After three hops, the money has crossed three entirely different technical environments, changed address formats twice, and passed through at least three different bridge or swap protocols, each of which records only its own piece of the puzzle. So, to reconstruct the full path, an investigator needs data from all three source chains simultaneously, knowledge of which bridge protocols were used and at roughly what time, and a tool capable of matching deposits and withdrawals across chains using amount, timing, and behavioral correlation rather than shared transaction IDs.
Most Blockchain Analytics platforms were built chain by chain. Ethereum support came first, then Bitcoin, then BNB Chain, and so on. Each chain got its own database, its own address clustering, its own risk scoring. The interfaces often reflect this architecture — you open a separate view for each network, run separate searches, and manually compare what you find. For single-chain investigations this is fine. For chain hopping, it's a blind spot. Every bridge crossing requires the analyst to manually switch contexts, identify the corresponding transaction on the destination chain, and carry the thread forward — a process that can take hours per hop, and that becomes practically impossible at scale when a single laundering operation crosses five or six chains before reaching an exit. Modern cross-chain analytics tools address this by maintaining a unified graph across all monitored blockchains, using automated bridge-matching algorithms that correlate deposits and withdrawals by amount, timing, and protocol behavior. Instead of separate silos, they treat the entire multi-chain ecosystem as one connected network — which is exactly how the funds are actually moving.
Address Poisoning
Address Poisoning (Picture 2) creates confusion rather than distance, as attackers generate addresses whose first and last characters match addresses their victims use regularly, then send dust transactions to poison the history.
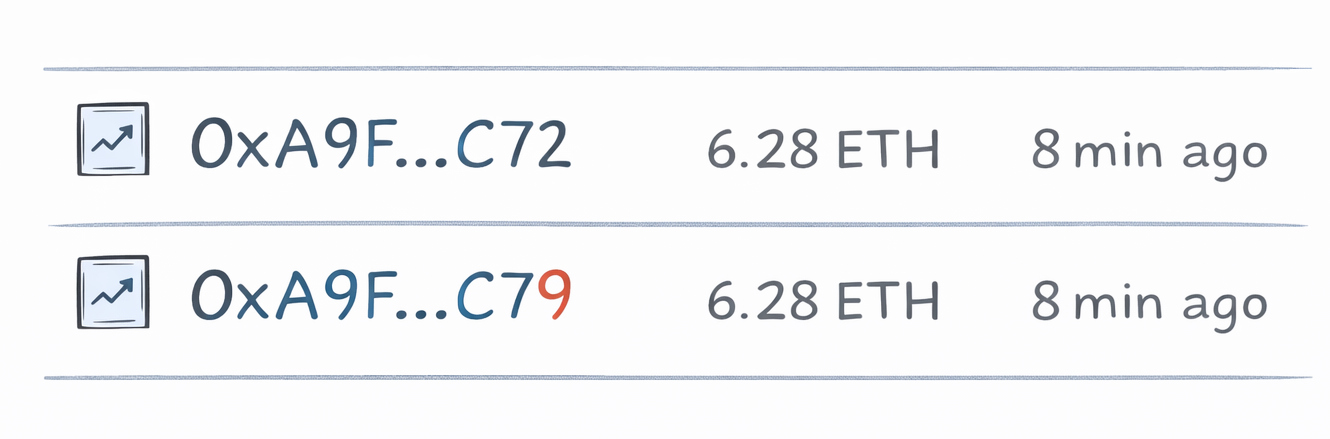
If the victim copies an address from their transaction list, they might paste the attacker's lookalike instead, sending funds somewhere unexpected and causing the trail to fork in a direction nobody anticipated—an effect we discussed in detail in our case study on how a poisoning scheme netted over $50K and was traced and recovered in our Honey Trap article.
Asset Fragmentation
Asset Fragmentation (Picture 3)— large sums broken into hundreds of pieces distributed simultaneously. The graph explodes in size and manual tracing becomes impossible.
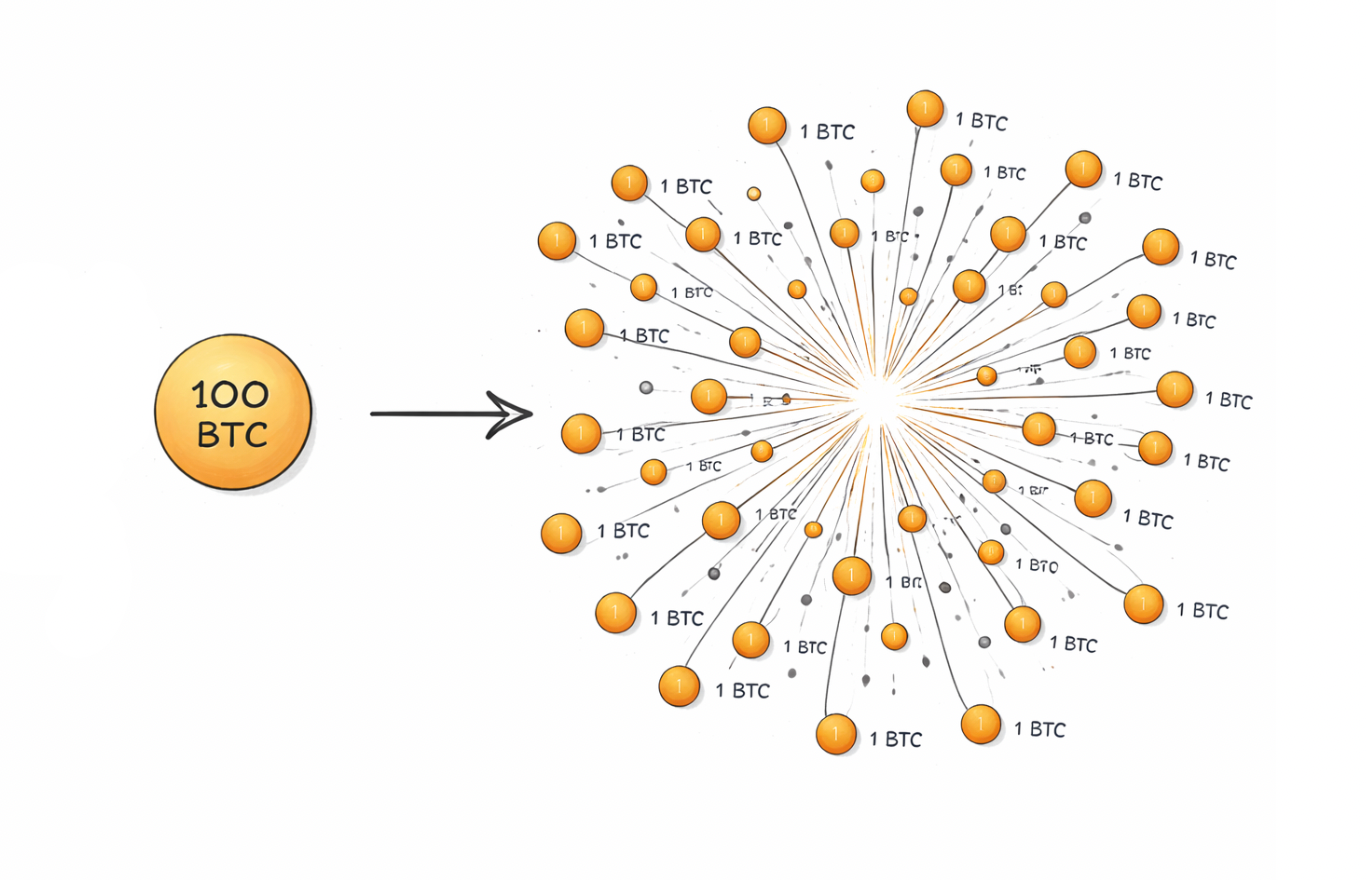
For example, imagine you’re tracing a suspicious wallet and the story looks manageable: one sender, one receiver, a few hops, a clear path. Then, in a single block everything changes. The funds don’t move forward as one stream anymore. They split into dozens or hundreds of tiny outbound transfers, fired off almost simultaneously to fresh addresses that have no history. If you’re looking at a transaction graph, this is the moment the graph stops being a line and turns into a burst.
To understand why fragmentation works, you need one basic idea about blockchain tracing: most fund flow analysis depends on continuity. Even when funds hop across multiple wallets, there’s usually a readable chain — A → B → C → D — where each hop can be linked by time, amount, and relationship to the previous step. Fragmentation breaks that continuity on purpose. Instead of one “next step,” there are suddenly a hundred “next steps,” and each one looks plausible in isolation but overwhelming as a set. The trail doesn’t disappear, it multiplies.
Mechanically, fragmentation is simple: a large sum is divided into many smaller outputs that go to many different addresses. On account-based chains, this often appears as a sequence of outbound transfers. On UTXO-based chains like Bitcoin, it can appear as a single transaction that creates a large number of outputs at once. The effect is similar across models: one source becomes many destinations. The analyst no longer has to “follow the money”, they have to follow money everywhere.
- The first challenge is scale. Tracing tools and explorers can show you the list of outgoing transfers, but your brain (and your time) become the bottleneck. If a wallet sends 300 transfers, you now have 300 threads to validate. Which ones are meaningful? Which are decoys? Which lead to an exit point? And which are just churn that never leaves the actor’s control? Even if you sample, you risk missing the one thread that matters — the branch that reaches an exchange deposit, a bridge, or a service that provides liquidity.
- The second challenge is that fragmentation is rarely a “final” step. It is usually the beginning of a second phase: consolidation. After the funds are scattered, many of those small pieces later reconverge — not back into the original wallet, but into aggregation wallets that look unrelated at first glance. That reconvergence can happen gradually or in bursts, and it can happen through intermediary wallets that exist only long enough to forward funds once. In graph terms, the actor intentionally forces the analyst to handle both extremes: first an explosion (one-to-many), then a foggy recombination (many-to-one) — and both are hard to interpret without automation.
- The third challenge is attribution noise. When you see hundreds of fresh addresses receiving tiny pieces, you’re not just dealing with more nodes — you’re dealing with weaker signals. Individual transfers may be too small to trigger risk thresholds, too common to look special, and too numerous to review manually. The pattern itself is the signal, but only if you can see it as a pattern. This is where transaction graph analysis becomes essential: you’re not trying to understand one transfer, you’re trying to understand the structure of the flow — branching degree, timing clusters, repeated re-use of intermediaries, and the “shape” of how funds disperse and later reassemble.
In practice, fragmentation turns a straightforward tracing task into a prioritization problem. Analysts have to identify which branches matter by looking for markers like: repeated destination behaviors, interactions with known services, clustering hints that suggest common control, or the emergence of entry and exit points among the chaos. Without that filtering, manual tracing becomes less “investigation” and more “endless clicking.” You can spend hours mapping branches that lead nowhere while the meaningful thread exits the system in the background.
That’s why fragmentation is so effective operationally. It doesn’t rely on hiding transactions — everything is visible on-chain. Instead, it weaponizes transparency by creating too much of it. The ledger is open, the data is there, and the trail exists — but it exists in a form that overwhelms human review. The outcome is not a dead end, but a maze: the funds are still traceable in theory, yet in practice the investigation stalls unless you can reconstruct the fund flow at scale, apply clustering logic, and reduce the explosion into a manageable set of candidate paths.
By 2026, these patterns have become more varied and more combinable — the same operation may chain-hop, fragment, and then consolidate again before reaching an exit. The clearest way to understand how they work in practice is through real-world case studies, and new variants continue to appear as the ecosystem evolves; for deeper breakdowns, you can explore our Investigations & Case Studies section.
Transaction Tracing vs Blockchain Forensics
These two terms are often used interchangeably, but they describe different scopes of work.
Transaction Tracing is the technical layer. It produces a fund flow map: a documented reconstruction of how assets moved from address to address. It finds the suspicious patterns, identifies the entry and exit points, and establishes connections between wallets. This is the core analytical work — the part that answers what happened.
Blockchain Forensics wraps around that with everything needed to use those findings in court. Rigorous methodology documentation. Chain of custody for evidence. Findings packaged to meet legal admissibility standards. Expert testimony, if it gets that far.
Put simply: tracing tells you the story. Forensics gets that story in front of a judge.
Most cases start as internal compliance reviews. An alert comes in, an analyst runs a trace, and either the risk is resolved or it isn't. When the trace reveals real exposure — sanctions hits, confirmed fraud proceeds, ransomware payments — it escalates into something more formal. That's when you're in cryptocurrency investigations territory, with tighter procedures and higher stakes.
Practical Limitations of Transaction Tracing
It would be misleading to talk about how powerful tracing is without being honest about where it breaks down.
- (a) Mixers and Privacy Tools are the obvious problem. Services like Tornado Cash, which facilitated over $7 billion in anonymized flows before OFAC sanctions, use Zero-Knowledge Proofs so users can deposit and withdraw with no on-chain link between the two. Coin mixing services fragment deposits, pool them with other users' funds, and redistribute with time delays. When funds go through a well-used mixer, the trail doesn't go cold. It gets replaced with noise.
- (b) Privacy Coins are a more fundamental obstacle. Monero hides the sender, recipient, and amount in every transaction by design. You can see that a transaction occurred — nothing more. As a general tool, standard analytics hit a near-complete blind spot here.
- (c) Cross-Chain Fragmentation creates gaps at every bridge crossing. Chain hopping has become a default step in sophisticated laundering precisely because bridge transfers break most standard tracing tools.
- (d) Attribution Gaps are the last-mile problem. Even a perfect trace only gets you to a blockchain address. Getting to a real-world identity requires off-chain data — exchange KYC records, IP logs, device identifiers — obtainable only through legal channels or voluntary cooperation.
- (e) False Positives round out the list. Clustering heuristics are probabilistic, not certain. CoinJoin transactions deliberately break the most common one, and shared custodial wallets or exchange hot wallets can create incorrect groupings. In high-stakes cases, attribution errors have serious consequences.
These are the most common structural limitations encountered in modern blockchain investigations. In practice, tracing complexity can increase further depending on jurisdictional opacity, off-chain settlement mechanisms, custodial layering, and the availability of legal cooperation.
When Transaction Tracing Becomes an Investigation
The transition from monitoring to investigation follows a predictable escalation logic.
A transaction monitoring system generates an alert — perhaps a deposit from a wallet with direct exposure to a sanctioned address, or a pattern matching a known layering typology. That alert goes to a compliance analyst for review. When the review deepens concern rather than resolving it — when the fund flow analysis reveals real connections to illicit activity — the case escalates.
The evidence is compiled into documentation. Depending on the findings, the case may trigger a Suspicious Activity Report filing or be referred to law enforcement with supporting analysis. The on-chain evidence forms the factual backbone of that escalation. If asset recovery is a goal, the process begins here, too, with tracing documentation support in crypto asset recovery and investigation.
Technologies Behind Modern Transaction Tracing
The techniques described above would be impossible to apply at scale without purpose-built infrastructure.
(а) Graph Databases are the foundation. Blockchain data is inherently a graph — addresses connected by transactions — and these databases are optimized for exactly the kind of path-finding and pattern-detection queries that tracing requires.
(b) Clustering Heuristics consolidate billions of individual addresses into manageable entity representations. The most fundamental is the common-input-ownership heuristic: when multiple addresses appear together as inputs in a single Bitcoin transaction, they almost certainly belong to the same entity. Change address detection, deposit forwarding patterns, and behavioral fingerprinting add additional grouping layers.
(c) Risk Scoring Models automate the initial assessment by applying hundreds of rules simultaneously—evaluating counterparty history, fund-flow origins, service-type exposure, and transaction behavior—to generate ratings that prioritize which cases require human review.
(d) Entity Attribution Systems link blockchain addresses to known real-world actors: exchanges, mixing services, darknet markets, and sanctioned organizations. The larger and more accurate the attribution database, the faster a trace can reach a meaningful conclusion.
For example, Tracer Tool applies these layers — graph analysis, clustering, risk scoring, and entity attribution — in an integrated environment designed for both compliance teams and investigators.

FAQ
What Is Transaction Tracing In Crypto?
Transaction tracing in crypto is the process of reconstructing the movement of digital assets across multiple blockchain transactions. It involves analyzing transaction paths, identifying connected wallets, and mapping how funds move from entry to exit points.
How Does Crypto Transaction Tracing Work?
Crypto transaction tracing works by analyzing transaction inputs and outputs, building transaction graphs, detecting wallet clustering patterns, and reconstructing fund flows across multiple addresses and transactions.
Is Transaction Tracing The Same As Blockchain Forensics?
No. Transaction tracing focuses on reconstructing fund flows and identifying suspicious patterns. Blockchain forensics goes further by preparing evidence, documenting findings, and supporting legal or regulatory investigations.
Can Transaction Tracing Identify Wallet Owners?
Transaction tracing does not directly reveal personal identities. However, it can attribute wallets to known entities such as exchanges, services, or sanctioned organizations based on behavioral patterns and publicly available data.
Why Is Transaction Tracing Important For Crypto Businesses?
Transaction tracing helps crypto businesses detect suspicious transaction patterns, monitor risk exposure, identify sanctioned interactions, and reduce compliance-related risks associated with illicit fund flows.
What Are Multi-Hop Transactions In Tracing?
Multi-hop transactions refer to funds moving through multiple intermediary wallets before reaching a final destination. Tracing tools analyze these hops to reconstruct the full path of asset movement.
How Does Cross-Chain Movement Affect Transaction Tracing?
Cross-chain movement complicates tracing because funds are transferred between blockchains via bridges or decentralized exchanges. Advanced analysis is required to reconstruct fund flows across networks.
What Is Wallet Clustering In Transaction Tracing?
Wallet clustering is the process of identifying multiple blockchain addresses that are likely controlled by the same entity, based on transaction behavior, interaction patterns, and fund-flow analysis.
Can Transaction Tracing Detect Laundering Patterns?
Transaction tracing can identify common laundering behaviors such as layering, consolidation, rapid splitting of funds, and interaction with high-risk services, but it does not guarantee full visibility in every case.
When Does Transaction Tracing Become An Investigation?
Transaction tracing becomes an investigation when suspicious activity requires deeper analysis, evidence preparation, and formal reporting to compliance teams or authorities.