KYC vs KYT Explained: Key Differences for Crypto Compliance

Independent research conducted across 2024–2025 found that more than 50% of wallets ultimately flagged as high-risk were initially assessed as safe at the time of onboarding. A wallet that passes every identity check on day one can become a conduit for laundered funds on day thirty — and if the only compliance layer in place is customer verification, that transition happens invisibly.
This is the fundamental gap that most crypto businesses fail to close. KYC — Know Your Customer — answers the question of who a user is. But it says nothing about what that user does after being verified. A customer who provides a valid passport and proof of address at onboarding can, within hours, receive funds from a mixer, transact with a sanctioned address, or participate in a layering scheme that moves illicit funds across multiple chains. KYC alone cannot detect any of this.
KYT — Know Your Transaction — exists to fill that gap. It monitors transaction behavior continuously, assessing risk not at a single point in time but throughout the entire lifecycle of the business relationship. Together, KYC and KYT form two layers of a single compliance system. Neither is a substitute for the other, and operating with only one creates a blind spot that regulators, auditors, and banking partners are increasingly unwilling to accept.
This article explains the difference between KYC and KYT, how each functions in the context of crypto AML compliance, and why the businesses that treat them as complementary layers (rather than alternatives) are the ones that pass audits, maintain banking relationships, and detect illicit activity before it becomes an enforcement problem.
What Is KYC in Crypto?
KYC — Know Your Customer — is the process of verifying the identity of a user before establishing a business relationship. In the crypto context, this means collecting and verifying identifying information at the point of account creation or onboarding, assessing the customer's risk profile, and determining whether the business relationship should proceed, be subject to enhanced scrutiny, or be declined. In practical terms, KYC for a crypto business involves 3 core steps:
- Identity Verification. Collecting government-issued identification (passport, national ID, driver's license), verifying its authenticity, and confirming that the person presenting the document is the person it identifies. For legal entity customers, this extends to verifying corporate registration, identifying beneficial owners, and confirming the entity's legal standing.
- Risk Assessment at Onboarding. Assigning a risk score to the customer based on factors such as country of residence, nationality, source of funds, PEP (Politically Exposed Person) status, and the intended purpose of the business relationship. This initial risk assessment determines the level of due diligence applied — standard CDD for lower-risk customers, enhanced due diligence (EDD) for higher-risk ones.
- Screening Against Watchlists. Checking the customer against sanctions lists (OFAC, EU, UN), PEP databases, and adverse media sources to identify individuals or entities that the business is legally prohibited from serving or that require elevated scrutiny.
KYC is a point-in-time process. It captures a snapshot of who a customer is at the moment they join the platform. It does not, and is not designed to, track what that customer does afterward. This is its structural limitation, and it is the reason that KYC alone, no matter how thorough, cannot constitute a complete AML compliance program.
What Is KYT in Crypto?
KYT — Know Your Transaction — is the process of continuously monitoring the transaction behavior of users and the risk characteristics of wallet addresses that interact with the platform. Where KYC asks "Who is this person?", KYT asks "What are they doing with their funds — and does it look suspicious?". In the crypto context, KYT operates on blockchain data. It analyzes:
- Transaction Flows. Where funds come from and where they go — tracing the on-chain history of deposits, withdrawals, and internal movements to identify exposure to high-risk sources such as mixers, sanctioned addresses, darknet markets, or fraud-linked wallets.
- Wallet Risk Profiles. The risk score of every wallet address that interacts with the platform, based on its transaction history, counterparty exposure, behavioral patterns, and any attributions from blockchain intelligence databases.
- Behavioral Patterns. Whether a user's on-chain activity is consistent with their declared profile — or whether it exhibits patterns associated with money laundering typologies, such as structuring, peel chains, rapid cross-chain movement, or dormant wallet reactivation.
- Ongoing Risk Changes. Whether a previously low-risk wallet has become high-risk due to new sanctions designations, newly identified illicit fund flows, or changes in the risk landscape that affect addresses already in the platform's ecosystem.
The defining characteristic of KYT is that it is continuous. Unlike KYC, which captures identity at a fixed point in time, KYT monitors behavior throughout the entire duration of the business relationship — re-evaluating risk as new data becomes available.
KYT vs KYC: Key Differences
The following table summarizes the core differences between KYC and KYT in the context of crypto AML Compliance:
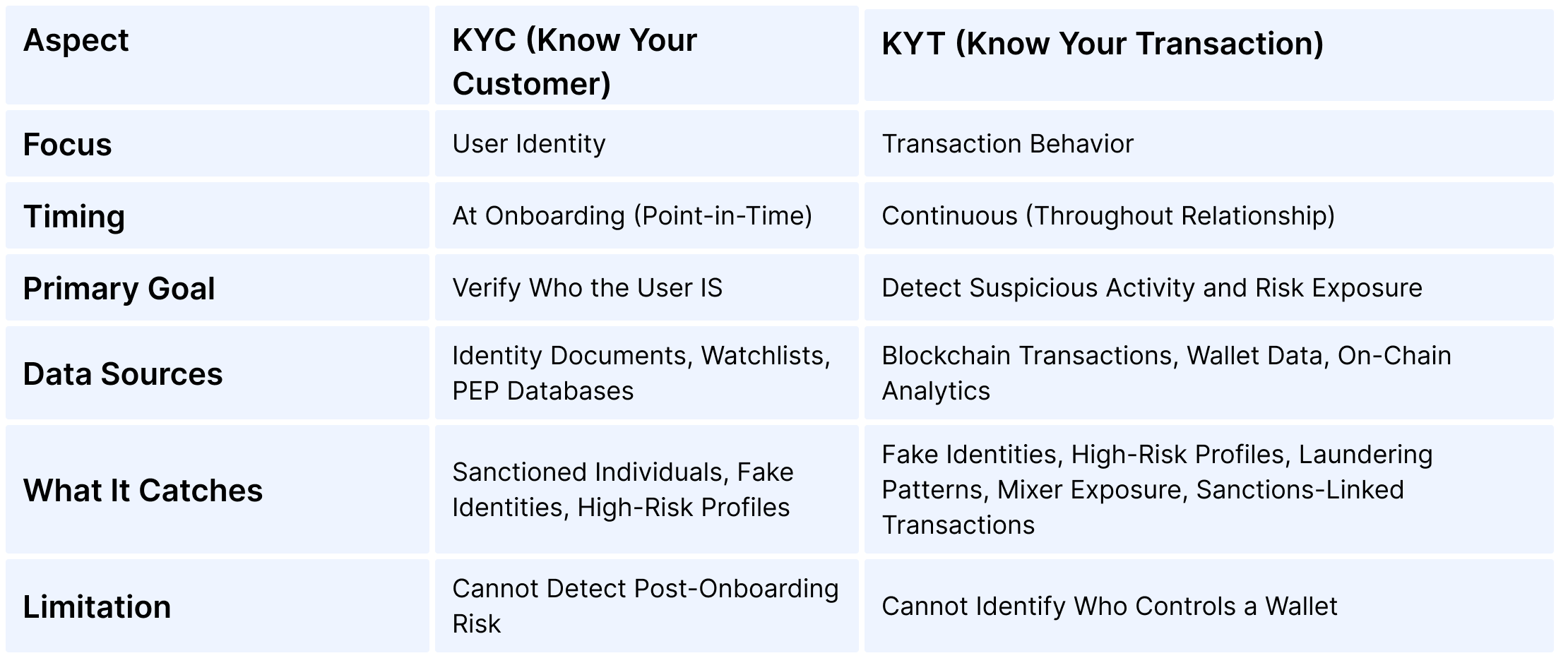
In practical terms, the distinction comes down to timing and data type. KYC operates on identity data at a fixed moment — the beginning of the relationship. KYT operates on behavioral data across the entire relationship. KYC tells you that a customer is who they claim to be. KYT tells you whether what they are doing with their funds is consistent with legitimate activity — or whether it matches patterns that indicate money laundering, fraud, or sanctions evasion. Neither layer alone provides sufficient visibility. A verified identity attached to unmonitored transactions is a compliance gap. Monitored transactions attached to an unverified identity are equally problematic — the business knows that something suspicious is happening but cannot determine who is responsible.
Why Crypto Businesses Need Both KYC and KYT
The regulatory frameworks that govern crypto businesses do not treat identity verification and transaction monitoring as alternatives. They treat them as distinct, mandatory components of a single AML/CFT compliance program. The FATF Recommendations make this structure explicit: Recommendations 10–12 establish CDD and ongoing due diligence obligations (the KYC layer), while Recommendations 16 and 20 establish transaction monitoring and suspicious activity reporting obligations (the KYT layer). In practical terms, each layer addresses a different category of risk — and the risks that one layer misses are precisely the risks that the other is designed to catch.
- KYC Without KYT: No Visibility After Onboarding. A customer passes identity verification with valid documents and a clean sanctions screening result. Two months later, they begin receiving deposits from wallets linked to a ransomware operation. Without KYT, this activity is invisible. The platform processes the transactions, the customer withdraws to fiat, and the business has unknowingly facilitated laundering — with a fully KYC-compliant customer record on file.
- KYT Without KYC: No Identity Behind the Risk. A transaction monitoring system flags a series of high-risk deposits from a wallet with direct mixer exposure. An alert is generated. But without KYC, the compliance team cannot identify who controls the account, cannot file a meaningful SAR (which requires identifying information), and cannot satisfy the regulatory requirement to know their customer. The risk is detected but cannot be acted upon effectively.
- KYC + KYT Together: Full Compliance Visibility. The same customer passes onboarding with verified identity. The KYT system monitors their transaction activity continuously. When high-risk deposits appear, the alert is linked to a verified identity — enabling the compliance team to investigate, escalate, file a SAR with complete identifying information, and take appropriate action (freezing the account, blocking withdrawals, or terminating the relationship).
This is not a theoretical distinction. Regulators conducting AML audits evaluate both layers. An audit that finds adequate KYC but no transaction monitoring will produce a finding — just as an audit that finds monitoring without proper customer identification will. The standard is both, not either.
How KYC and KYT Work Together in Practice
Understanding the difference between KYC and KYT is useful conceptually, but the real value lies in how the two layers interact operationally — creating a feedback loop that strengthens both.
- Onboarding: KYC Sets the Baseline. A new user submits identity documents and undergoes verification. Sanctions screening is performed. A risk score is assigned based on identity factors — jurisdiction, PEP status, source of funds. This baseline score determines the initial monitoring intensity applied by the KYT layer.
- First Transactions: KYT Begins Monitoring. As the user starts transacting, the KYT system evaluates every deposit and withdrawal — tracing fund origins, checking counterparty risk, and comparing behavioral patterns against known typologies. If the user's transaction behavior is consistent with their declared profile, the risk score remains stable.
- Risk Change: KYT Triggers Re-Assessment. If the KYT system detects a change — a deposit from a high-risk address, interaction with a mixer, a sudden spike in transaction volume — it generates an alert. This alert feeds back into the customer's overall risk profile, potentially escalating the customer from standard to enhanced due diligence. The compliance team may request additional documentation, restrict activity, or file a SAR.
- Ongoing Lifecycle: Continuous Feedback. Throughout the business relationship, KYT continuously re-evaluates transaction risk, and those evaluations continuously update the customer risk profile originally established by KYC. A customer who was low-risk at onboarding may become high-risk based on transaction behavior — and the system adjusts monitoring intensity, documentation requirements, and reporting obligations accordingly.
This feedback loop is what transforms two separate compliance processes into a unified system. The businesses that achieve this integration are the ones that detect risk effectively, respond proportionately, and produce the audit-ready documentation that regulators expect.
Common Misconceptions About KYT and KYC
Several persistent misconceptions lead crypto businesses to underinvest in one or both compliance layers — creating gaps that become visible during audits or enforcement actions.
- "KYC Is Enough." This is the most common and most dangerous assumption. KYC verifies identity at onboarding — it creates a record of who the customer claims to be. But it provides zero visibility into what happens after that point. A verified customer can begin laundering funds within hours of passing KYC. Without KYT, the business has no mechanism to detect this. Industry data shows that the majority of wallets eventually flagged as high-risk appeared clean at the time of initial screening.
- "KYT Is Optional." Transaction monitoring is not a value-add feature. It is a regulatory requirement under every major AML framework. The FATF Recommendations require ongoing monitoring of customer transactions. MiCA requires CASPs to apply ongoing monitoring of business relationships. The BSA requires MSBs to identify and report suspicious activity. A crypto business that has KYC but no KYT is operating with an incomplete compliance program — and auditors will identify this gap.
- "Monitoring Only Matters for Large Transactions." This misconception conflates threshold-based reporting (such as the BSA's $3,000 Travel Rule trigger or $10,000 CTR threshold) with the broader obligation to monitor all transactions for suspicious activity. The obligation to detect and report suspicious transactions applies regardless of amount. Money laundering schemes frequently use structuring — breaking large amounts into smaller transactions — specifically to avoid threshold-based detection. A monitoring system that only flags large transactions misses this entirely.
- "One-Time Wallet Screening Equals KYT." Checking a wallet address against a risk database at the time of a single transaction is not transaction monitoring. It is a screening check — useful, but fundamentally different from continuous monitoring. KYT requires ongoing re-evaluation of risk as the wallet's transaction history evolves, new intelligence becomes available, and the broader risk landscape changes. A wallet screened as clean today may be flagged tomorrow.
How AMLBot Supports KYC and KYT
AMLBot provides both KYC and KYT capabilities as integrated components of a unified compliance platform, enabling crypto businesses to operate both layers from a single system rather than managing separate, disconnected tools.
- KYC and KYB Verification. AMLBot's KYC Solution supports identity verification for both natural persons and legal entities — including document verification, sanctions and PEP screening, and risk-based onboarding workflows.
- Continuous Transaction Monitoring (KYT). AMLBot's KYT Platform provides continuous monitoring across major blockchains, with dynamic risk scoring, real-time alerts, behavioral pattern detection, and audit-ready documentation — ensuring that transaction risk is assessed not once, but throughout the entire customer lifecycle.
- Integrated Risk View. By operating KYC and KYT within a single platform, compliance teams can link identity data to transaction behavior — enabling the feedback loop described in this article, where monitoring alerts inform customer risk profiles and identity context informs monitoring decisions.
Conclusion
The difference between KYC and KYT is not a matter of choosing one over the other. It is the difference between knowing who your customer is and knowing what they do. In a compliance system that works, both questions are answered — continuously, in connection with each other, and with documentation sufficient to satisfy regulators, auditors, and banking partners.
KYC without KYT leaves a business blind to post-onboarding risk. KYT without KYC leaves a business unable to identify who is behind suspicious activity. Together, they form the two layers of a compliance program that can detect, investigate, and report the risks that crypto businesses are legally obligated to manage.
-AMLBot Team

FAQ
What Is the Difference Between KYC and KYT in Crypto?
KYC verifies a user's identity, while KYT monitors transaction activity to detect suspicious behavior and assess risk over time.
Do Crypto Businesses Need Both KYC and KYT?
Yes, both are essential. KYC identifies who the user is, and KYT tracks what they do with funds, providing full visibility for AML compliance.
Can KYT Replace KYC?
No, KYT cannot replace KYC. It complements identity verification by monitoring transactions after onboarding.
When Is KYC Performed Compared to KYT?
KYC is performed during onboarding, while KYT is continuous and monitors transactions throughout the user lifecycle.
Why Is KYC Alone Not Enough in Crypto?
KYC only verifies identity at a single point in time. It does not track how funds move or detect suspicious behavior after onboarding.
What Does KYT Monitor in Crypto Transactions?
KYT monitors wallet activity, transaction flows, risk exposure, and connections to high-risk or illicit entities.
How Do KYC and KYT Work Together in AML Compliance?
KYC links a real-world identity to a user, while KYT analyzes their transaction behavior, allowing businesses to detect and respond to risks effectively.
Is KYT Required by Regulators?
While not always explicitly named as "KYT," Transaction Monitoring is expected under global AML Frameworks such as FATF Recommendations and regional regulations like MiCA.
What Risks Can KYT Help Detect?
KYT helps detect fraud, money laundering, sanctions exposure, and suspicious transaction patterns.
What Happens If a Crypto Business Uses KYC but Not KYT?
The business may miss ongoing risks, including suspicious transactions, which can lead to regulatory issues, financial losses, or account restrictions.